Letsdefend Lab Review
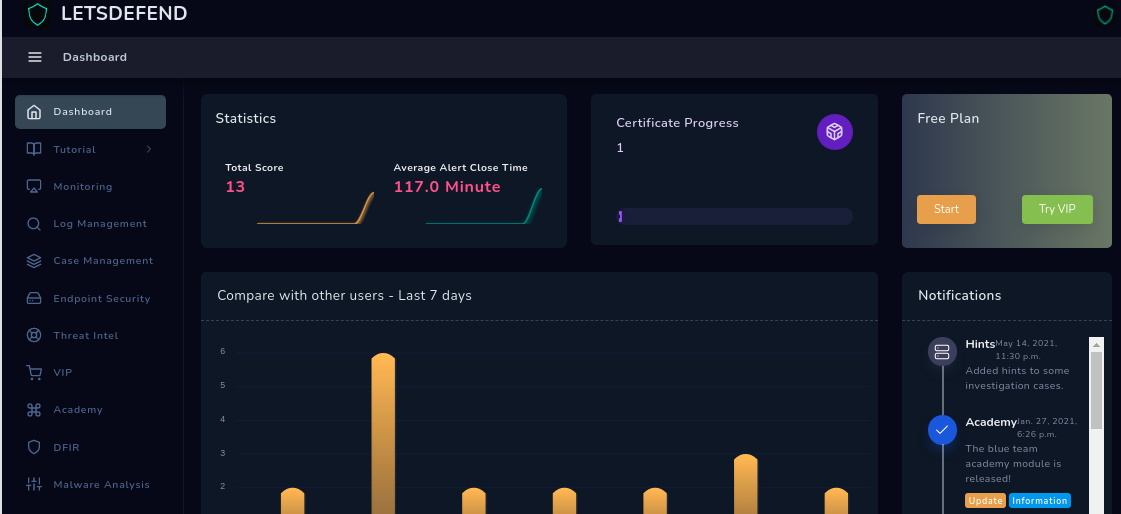
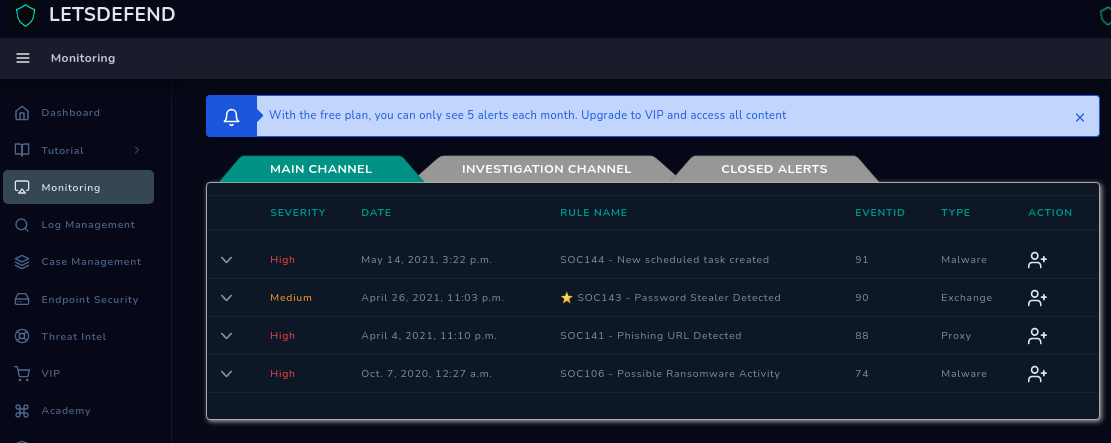
Letsdefend Lab Review This blog presents a hands on walkthrough of soc investigations performed using the letsdefend platform, drawing directly from cases i analyzed and closed in my letsdefend lab environment. 🚨 just completed the brute force room on letsdefend! 🧠🔐 this hands on lab challenged me to detect, investigate, and respond to brute force attack activity in a simulated soc environment.
Letsdefend Lab Review Soc analysts out there, which training platform offers the most realistic relevant experience? my goal is to land a role as a soc analyst. i’ve passed the security this month, i have an active ts sci, and a background in intelligence analysis. This review goes beyond letsdefend, and you see additional tools with security onion and elk. technically, we can finish the case in 5 minutes, but we go a long way and dive deep into real world stuff. This technology is designed to identify and remove content that breaches our guidelines, including reviews that are not based on a genuine experience. we recognise we may not catch everything, and you can flag anything you think we may have missed. Find top rated software and services based on in depth reviews from verified users. 400 software categories including paas, nosql, bi, hr, and more.

Letsdefend Lab Review This technology is designed to identify and remove content that breaches our guidelines, including reviews that are not based on a genuine experience. we recognise we may not catch everything, and you can flag anything you think we may have missed. Find top rated software and services based on in depth reviews from verified users. 400 software categories including paas, nosql, bi, hr, and more. Having finished the letsdefend’s soc analyst path, i have some thoughts on it. for me, it was the very first blue team learning path that i ever took and so far i think it has done a good job of introducing me to some of the very basic terms, concepts, and tools of this field. Your role is to review events generated from the fictional network you defend. investigate the event for signs of malicious activity, correctly respond to the alert and protect your network from further compromise. With that said, i am researching letsdefend, security blueteam, and cyberdefenders to curate a more practical learning path to actually obtain the skills required to do the job i am aiming for which would be entry level cyber. This blog presents a hands on walkthrough of soc investigations performed using the letsdefend platform, drawing directly from cases i analyzed and closed in my letsdefend lab environment.
Comments are closed.