Learning Lab Understanding Deep Packet Inspection Dpi In Endpoint

Learning Lab Understanding Deep Packet Inspection Dpi In Endpoint You’ll discover how to configure and optimize dpi for effective threat detection, application control, and data loss prevention—without compromising performance or privacy. What is deep packet inspection? an advanced network filtering method, deep packet inspection (dpi) examines the actual content (“payload”) of data packets traveling through a network checkpoint, not just the basic addressing information.
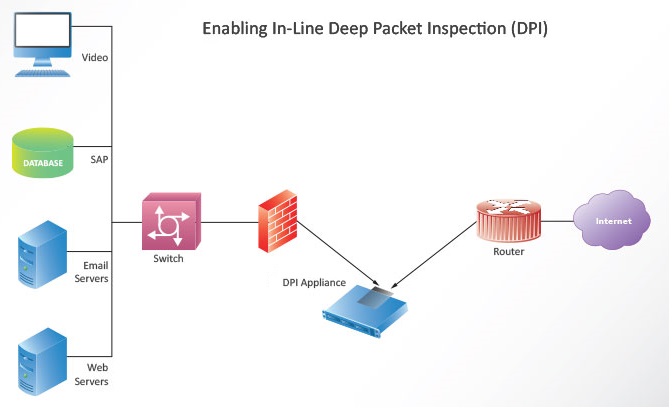
Deep Packet Inspection Understanding deep packet inspection dpi operates at the application layer of the osi model, enabling security tools to identify malware, prevent data leaks, enforce compliance, and optimize bandwidth. Deep packet inspection (dpi) is a network packet filtering technology that inspects the data contained in packets as they pass through inspection points, enabling control over network. Explore what dpi is, how it works, and why it’s vital for network security. learn key functions, osi layers, firewalls, and its role in ndr. Deep packet inspection (dpi) is an extraction technique in which we can filter out unnecessary malware and filter them out to reduce the unwanted traffic that may cause congestion on the network.
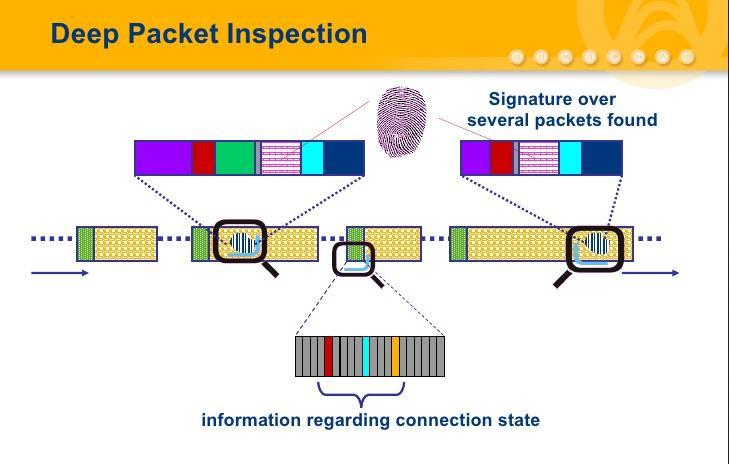
Deep Packet Inspection Dpi Cyber Arts Explore what dpi is, how it works, and why it’s vital for network security. learn key functions, osi layers, firewalls, and its role in ndr. Deep packet inspection (dpi) is an extraction technique in which we can filter out unnecessary malware and filter them out to reduce the unwanted traffic that may cause congestion on the network. Learn what deep packet inspection (dpi) is and how dpi works to block malware and stop data leaks. discover how the fortigate ngfw uses dpi to identify threats. Deep packet inspection (dpi) inspects packet payloads and metadata beyond header fields to identify applications, protocols, content patterns, and anomalies. analogy: dpi is like an airport security scanner that opens luggage rather than just checking luggage size. Learn what a dpi firewall is, how deep packet inspection works, why it’s essential for security, and how it detects apps, threats, vpns, and encrypted traffic. Understanding how dpi functions, why it is used, and where its technical limitations lie offers crucial insight into the ongoing tension between privacy, performance, and control in the global internet ecosystem.
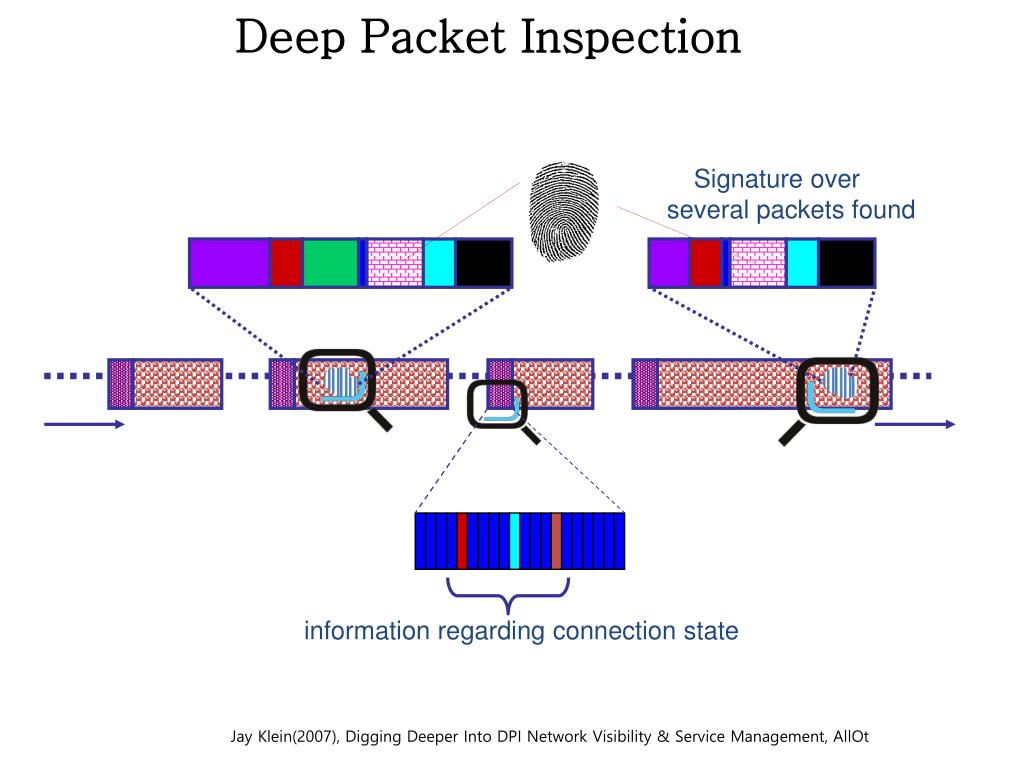
Ppt Deep Packet Inspection And Net Neutrality Packet Dpi Spi Tcp Learn what deep packet inspection (dpi) is and how dpi works to block malware and stop data leaks. discover how the fortigate ngfw uses dpi to identify threats. Deep packet inspection (dpi) inspects packet payloads and metadata beyond header fields to identify applications, protocols, content patterns, and anomalies. analogy: dpi is like an airport security scanner that opens luggage rather than just checking luggage size. Learn what a dpi firewall is, how deep packet inspection works, why it’s essential for security, and how it detects apps, threats, vpns, and encrypted traffic. Understanding how dpi functions, why it is used, and where its technical limitations lie offers crucial insight into the ongoing tension between privacy, performance, and control in the global internet ecosystem.

Deep Packet Inspection Dpi Uses That Shape Network Security Network Learn what a dpi firewall is, how deep packet inspection works, why it’s essential for security, and how it detects apps, threats, vpns, and encrypted traffic. Understanding how dpi functions, why it is used, and where its technical limitations lie offers crucial insight into the ongoing tension between privacy, performance, and control in the global internet ecosystem.
Comments are closed.