Learn Cryptography 5 Encryption Using Python Symmetric Stream
Learn Cryptography 5 Encryption Using Python Symmetric Stream A stream cipher is a method of encrypting text (to produce ciphertext) in which a cryptographic key and algorithm are applied to each binary digit in a data stream, one bit at a time. Unit 2: symmetric key the key concepts involved are defining key entropy; key generators (such as using hashing methods to generate keys based on passphrases); symmetric key methods (aes, twofish, 3des, rc4 and chacha20); stream or block encryption; symmetric key modes (ecb cbc ofb); and salting iv.

Learn Cryptography 5 Encryption Using Python Symmetric Stream Encryption is the process of converting readable data into an unreadable format to protect its contents. this is useful when storing or sharing sensitive information. in python, we can encrypt and decrypt files using the cryptography library’s fernet module, which uses symmetric encryption. Learn how to securely implement aes symmetric encryption and decryption in python. step by step tutorial with code for encrypting messages and files using cryptography library. In this section you will first learn the definition of symmetric encryption, and about the two main forms of symmetric encryption which are stream ciphers and block ciphers. One of the simplest ways to perform symmetric encryption in python is to use fernet algorithm from cryptography module. let's see how to use it.
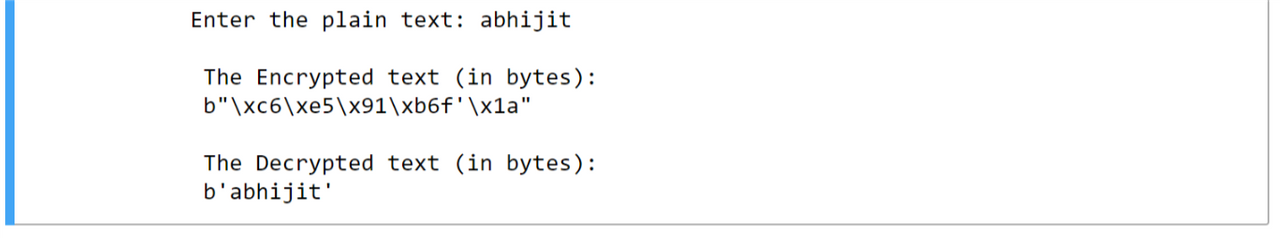
Learn Cryptography 5 Encryption Using Python Symmetric Stream In this section you will first learn the definition of symmetric encryption, and about the two main forms of symmetric encryption which are stream ciphers and block ciphers. One of the simplest ways to perform symmetric encryption in python is to use fernet algorithm from cryptography module. let's see how to use it. C.1. symmetric key algorithms other terms for symmetric key encryption are single key, one key, and private key encryption. use of the latter term can sometimes conflict with the term private key in public key cryptography disadvantage: key distribution symmetric key algorithms can be divided into: stream ciphers: encrypt the bits of the message one at a time block ciphers: take a number of. Welcome to pyca cryptography cryptography includes both high level recipes and low level interfaces to common cryptographic algorithms such as symmetric ciphers, message digests, and key derivation functions. In this lesson we will look at symmetric key cryptography which secures much of the data at rest and in transit by virtue of its efficiency. Outline •case study •python: performing symmetric encryption •python: using hash function 2the reading materials can be accessed on moodle. a total of 15 minutes is allocated for each question for both self reading answering.
Module 2 Symmetric Encryption Algorithms 5 Pdf Encryption C.1. symmetric key algorithms other terms for symmetric key encryption are single key, one key, and private key encryption. use of the latter term can sometimes conflict with the term private key in public key cryptography disadvantage: key distribution symmetric key algorithms can be divided into: stream ciphers: encrypt the bits of the message one at a time block ciphers: take a number of. Welcome to pyca cryptography cryptography includes both high level recipes and low level interfaces to common cryptographic algorithms such as symmetric ciphers, message digests, and key derivation functions. In this lesson we will look at symmetric key cryptography which secures much of the data at rest and in transit by virtue of its efficiency. Outline •case study •python: performing symmetric encryption •python: using hash function 2the reading materials can be accessed on moodle. a total of 15 minutes is allocated for each question for both self reading answering.
Comments are closed.