Keylogging Via Phishing Attack
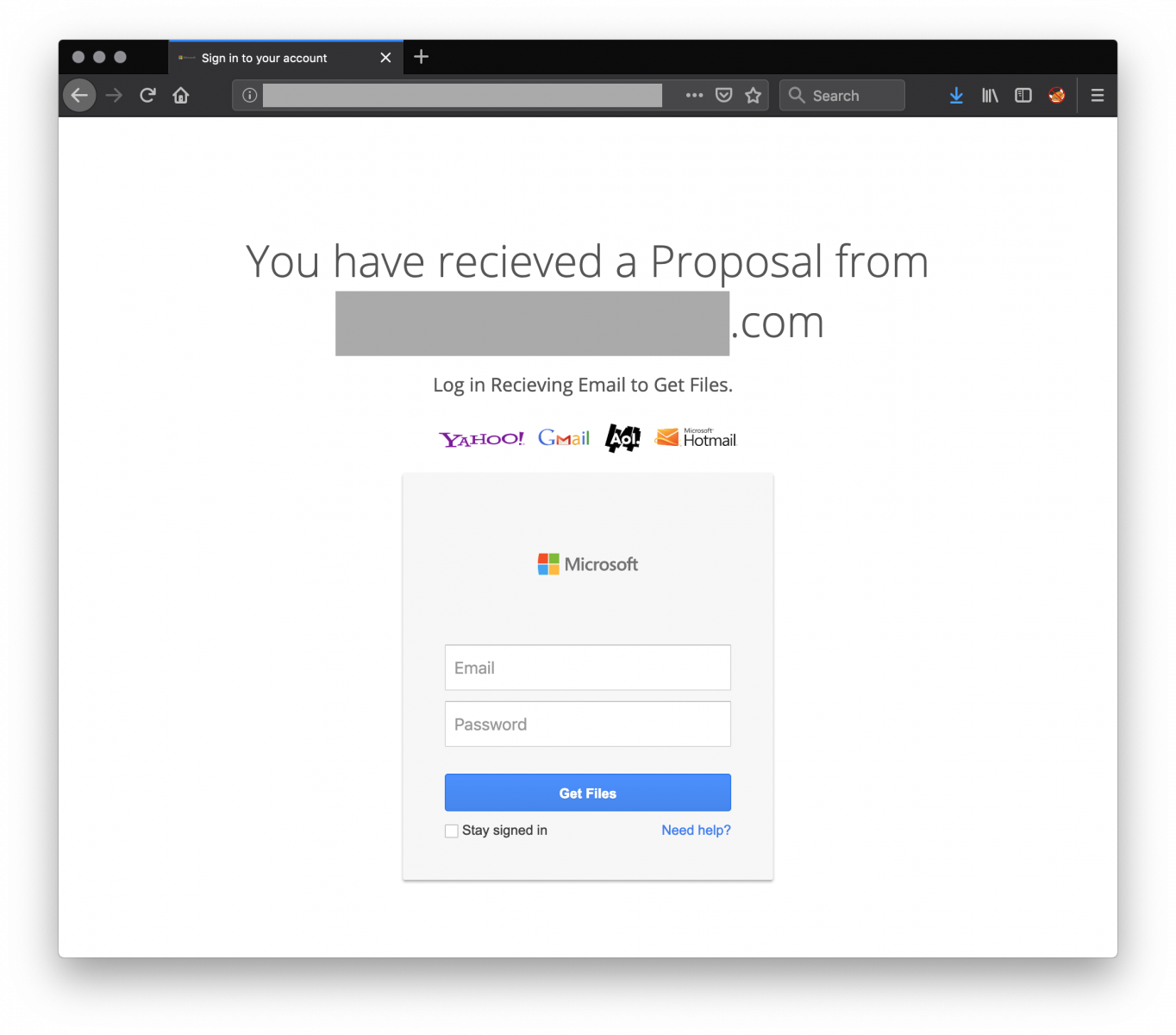
Phishing Kit With Javascript Keylogger Sans Isc This type of keylogging software is typically deployed on a website rather than downloaded on a victim’s computer. a hacker might use form grabbing keyloggers on a malicious website that prompts victims to enter their credentials. Keyloggers are often delivered through phishing emails, fake software, or infected websites. use multi factor authentication (mfa). even if a password is captured, mfa adds another layer of protection that makes it harder for cyberattackers to access your accounts. secure shared or public devices.

Phishing Scam Fraud Security Breach Cyber Attack Concept A Red Lock Consider, in a spear phishing attack, hackers may use keyloggers to gather information about an employee, such as their login credentials and interests, before sending a specially tailored phishing email that includes malware, or requesting sensitive information. In 2021, we fully anticipate that the greatest danger to organisations and especially in smaller enterprises, will come from keylogging and screen grabbing malware, primarily because they are the attack vector through which sensitive data is most often and most easily, stolen. On android, eset mobile security helps protect users by detecting and blocking malicious links and phishing attempts, reducing the risk of malware including keyloggers being installed. Phishing emails are a common vector for distributing keyloggers. these emails are crafted to appear legitimate and often mimic messages from trusted sources such as banks, service providers, or colleagues.

How Multi Stage Phishing Attacks Exploit Qrs Captchas And On android, eset mobile security helps protect users by detecting and blocking malicious links and phishing attempts, reducing the risk of malware including keyloggers being installed. Phishing emails are a common vector for distributing keyloggers. these emails are crafted to appear legitimate and often mimic messages from trusted sources such as banks, service providers, or colleagues. Software keyloggers are malicious programs installed through phishing emails or drive by downloads. they also come bundled with pirated software. they run invisibly in the background, capturing keystrokes at the operating system level. hardware keyloggers are physical devices. Attack tactics like phishing and social engineering are some of the common ways keyloggers are installed in a malicious scenario. but there is another way this software can find its way to your computer. Whether introduced through phishing emails, infected downloads, or physical devices, keyloggers pose a serious risk to both individuals and organizations. their ability to remain undetected makes them particularly dangerous, demanding proactive detection and strong protection measures. Keyloggers are often deployed through phishing attacks, malicious downloads or vulnerabilities in outdated software. once installed, they run quietly in the background, capturing every keystroke you make.
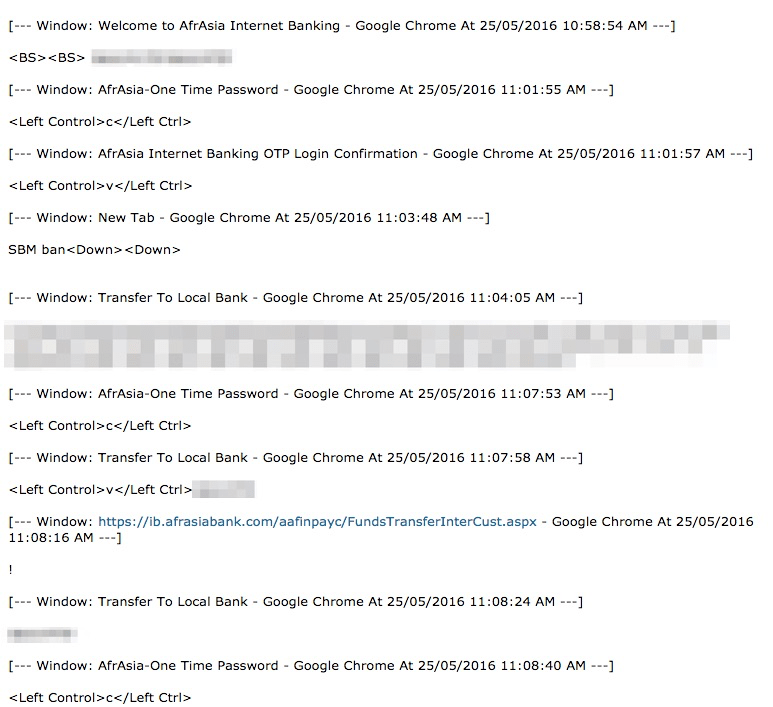
Credential Phishing Leads To Ispy Keylogger Proofpoint Us Software keyloggers are malicious programs installed through phishing emails or drive by downloads. they also come bundled with pirated software. they run invisibly in the background, capturing keystrokes at the operating system level. hardware keyloggers are physical devices. Attack tactics like phishing and social engineering are some of the common ways keyloggers are installed in a malicious scenario. but there is another way this software can find its way to your computer. Whether introduced through phishing emails, infected downloads, or physical devices, keyloggers pose a serious risk to both individuals and organizations. their ability to remain undetected makes them particularly dangerous, demanding proactive detection and strong protection measures. Keyloggers are often deployed through phishing attacks, malicious downloads or vulnerabilities in outdated software. once installed, they run quietly in the background, capturing every keystroke you make.
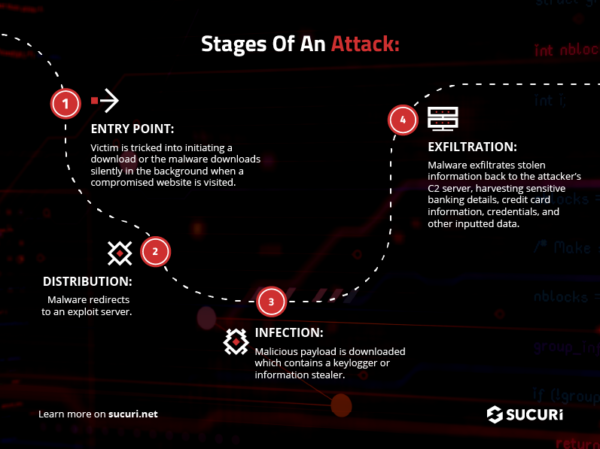
What Is A Keylogger Whether introduced through phishing emails, infected downloads, or physical devices, keyloggers pose a serious risk to both individuals and organizations. their ability to remain undetected makes them particularly dangerous, demanding proactive detection and strong protection measures. Keyloggers are often deployed through phishing attacks, malicious downloads or vulnerabilities in outdated software. once installed, they run quietly in the background, capturing every keystroke you make.

What Is Keylogging Cybersecurity Tips Devoteam Cyber Trust
Comments are closed.