Kali Linux Vm Setup For A Safe Hacking Lab

How To Set Up A Kali Linux Virtual Machine On Azure To Serve As A This repository provides a comprehensive guide for setting up a penetration testing lab using oracle virtualbox with ubuntu, kali linux, and metasploitable. you can use this lab for ethical hacking, ctfs, and cybersecurity learning. This project aims to set up a cybersecurity lab using virtualbox as our virtual host and kali linux as our virtual machine. if you’re learning cybersecurity and still haven’t built a home lab, this is your sign.
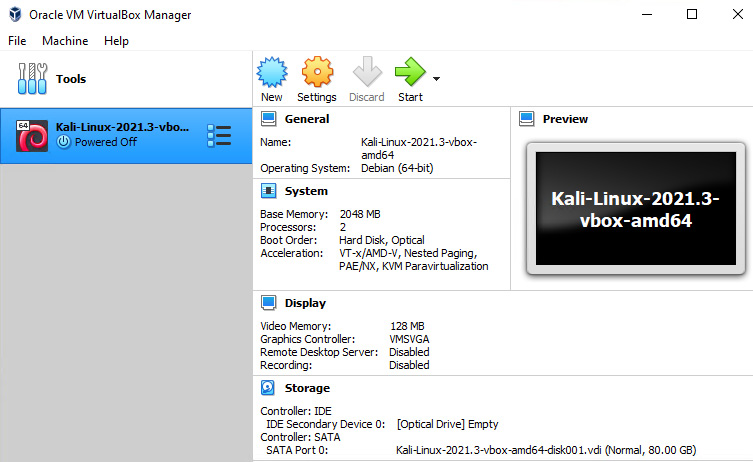
Hands On Ethical Hacking Tactics Security Ebook We have successfully set up our lab with both the attacker machine (kali linux) and the victim machine (metasploitable 2). you can see this clearly in the image below. A step by step guide to building a safe, isolated cybersecurity lab at home using virtualbox or vmware — with kali parrot, vulnerable targets, hosted labs, network modes, snapshots, and best practices. Setup notes documented so you can reproduce everything quickly. if you hit all of those points, you now have a lab that is safe, fast to recover, and useful for real security practice. Want to practice hacking legally? this guide shows you how to build a safe penetration testing lab at home using virtualbox, kali linux, and vulnerable vms. follow our step by step 2025 guide.

1 2 Lab Setup Virtualbox And Kali Linux V1 Pdf Virtual Machine Setup notes documented so you can reproduce everything quickly. if you hit all of those points, you now have a lab that is safe, fast to recover, and useful for real security practice. Want to practice hacking legally? this guide shows you how to build a safe penetration testing lab at home using virtualbox, kali linux, and vulnerable vms. follow our step by step 2025 guide. In this detailed guide, we'll walk you through the process of setting up a kali linux penetration testing lab. by the end of this tutorial, you'll have a fully functional lab to practice. In this guide, i’ll walk you through the step by step process of setting up kali linux as part of a cybersecurity lab. the goal is to create a robust environment where you can simulate. In this video, you’ll learn how to safely set up your own ethical hacking lab by installing kali linux in a virtual machine. this step by step guide is perfe. In this tutorial, we will build a complete penetration testing lab using virtualbox, where kali linux acts as the attacker machine and metasploitable 2 acts as the vulnerable target. this lab is completely offline, isolated, and suitable for academic and self learning purposes.
Comments are closed.