Json Web Token Jwt Explained From Scratch Spring Security 6

01 Jwt Authentication In Spring Boot 3 With Spring Security 6 Pdf In this video, we do a complete deep dive into jwt (json web token) and understand why jwt is needed, how it works internally, and how to implement jwt authentication and authorization. A practical guide to implementing json web token authentication in spring boot applications using spring security 6, covering token generation, validation, and securing rest endpoints.
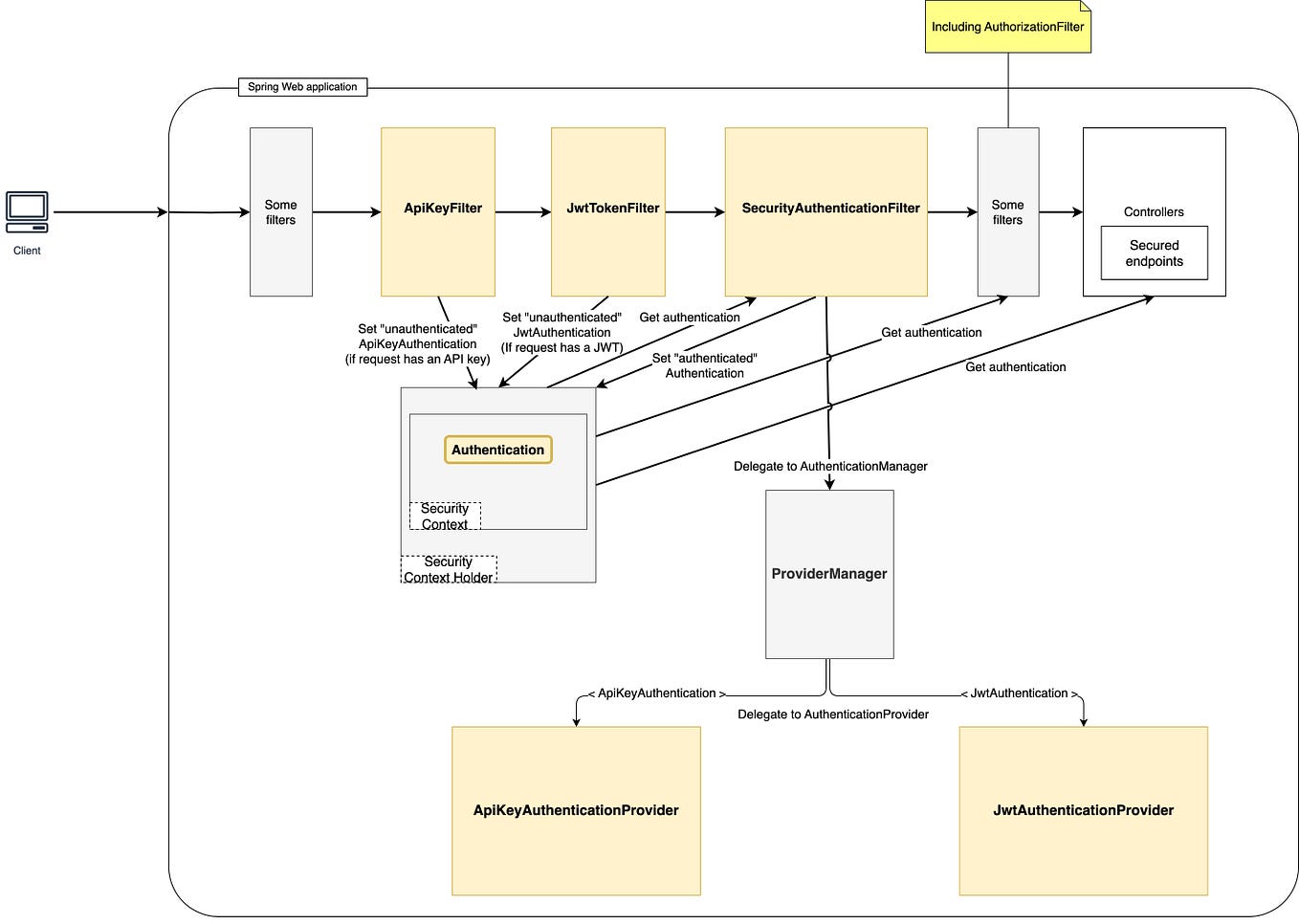
Implementing Json Web Token Jwt Authentication Using Spring Security Learn how to implement jwt authentication with spring 6 security following best practices recommended in spring docs and without creating complex custom filters. In this guide, we’ll walk through how to implement jwt authentication in spring security 6, emphasizing key changes and optimizations. why jwt? jwt is a compact, self contained token that can securely transmit information between parties. An implementation of an abstractoauth2token representing a json web token (jwt). jwts represent a set of "claims" as a json object that may be encoded in a json web signature (jws) and or json web encryption (jwe) structure. This post shows how to secure a spring boot 3 application by implementing json web token (jwt) authentication step by step using spring security 6.
Implementing Json Web Token Jwt Authentication Using Spring Security An implementation of an abstractoauth2token representing a json web token (jwt). jwts represent a set of "claims" as a json object that may be encoded in a json web signature (jws) and or json web encryption (jwe) structure. This post shows how to secure a spring boot 3 application by implementing json web token (jwt) authentication step by step using spring security 6. Learn how json web tokens (jwt) work internally, common mistakes developers make, and how to implement secure jwt authentication in spring boot. includes a browser based jwt decoder and validator. In this tutorial, i’m happy to guide you through the development of securing rest api end points using jwt and spring security in a spring based application, from scratch. Learn to implement jwt authentication with spring security 6. learn about token creation, validation, filters, securing apis using modern best practices. Json web tokens (jwt) offer a modern approach to secure apis by providing a stateless authentication mechanism. in this blog, we will explore how to secure a spring boot application using spring security 6 and jwt.

Implementing Json Web Token Jwt Authentication Using Spring Security Learn how json web tokens (jwt) work internally, common mistakes developers make, and how to implement secure jwt authentication in spring boot. includes a browser based jwt decoder and validator. In this tutorial, i’m happy to guide you through the development of securing rest api end points using jwt and spring security in a spring based application, from scratch. Learn to implement jwt authentication with spring security 6. learn about token creation, validation, filters, securing apis using modern best practices. Json web tokens (jwt) offer a modern approach to secure apis by providing a stateless authentication mechanism. in this blog, we will explore how to secure a spring boot application using spring security 6 and jwt.
Comments are closed.