Implementing Json Web Token Jwt Authentication Using Spring Security
Implementing Json Web Token Jwt Authentication Using Spring Security Introduction in this tutorial, you will learn to implement json web token ( jwt ) authentication using spring boot and spring security. A practical guide to implementing json web token authentication in spring boot applications using spring security 6, covering token generation, validation, and securing rest endpoints.
Implementing Json Web Token Jwt Authentication Using Spring Security This post shows how to secure a spring boot 3 application by implementing json web token (jwt) authentication step by step using spring security 6. Step by step implementation and best practices to secure rest apis in java with json web token, persistence in postgresql, and effective management of roles and permissions. Welcome to our guide on implementing token based authentication with spring boot and spring security using json web tokens (jwt). Learn how to implement jwt authentication in spring boot 3.x.x with this step by step guide. secure your rest apis with json web tokens, explore best practices, and enhance security using spring security and bcrypt.
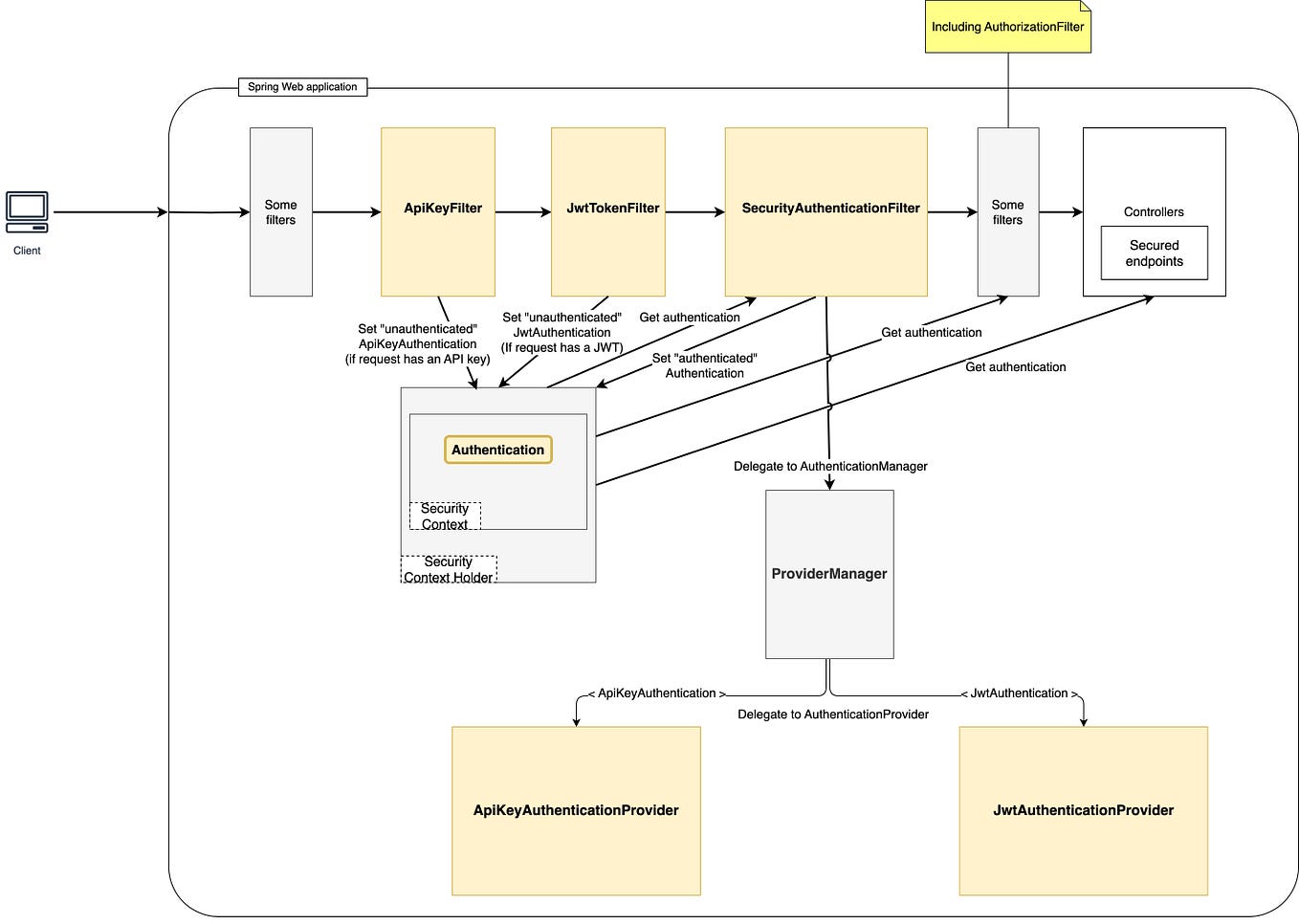
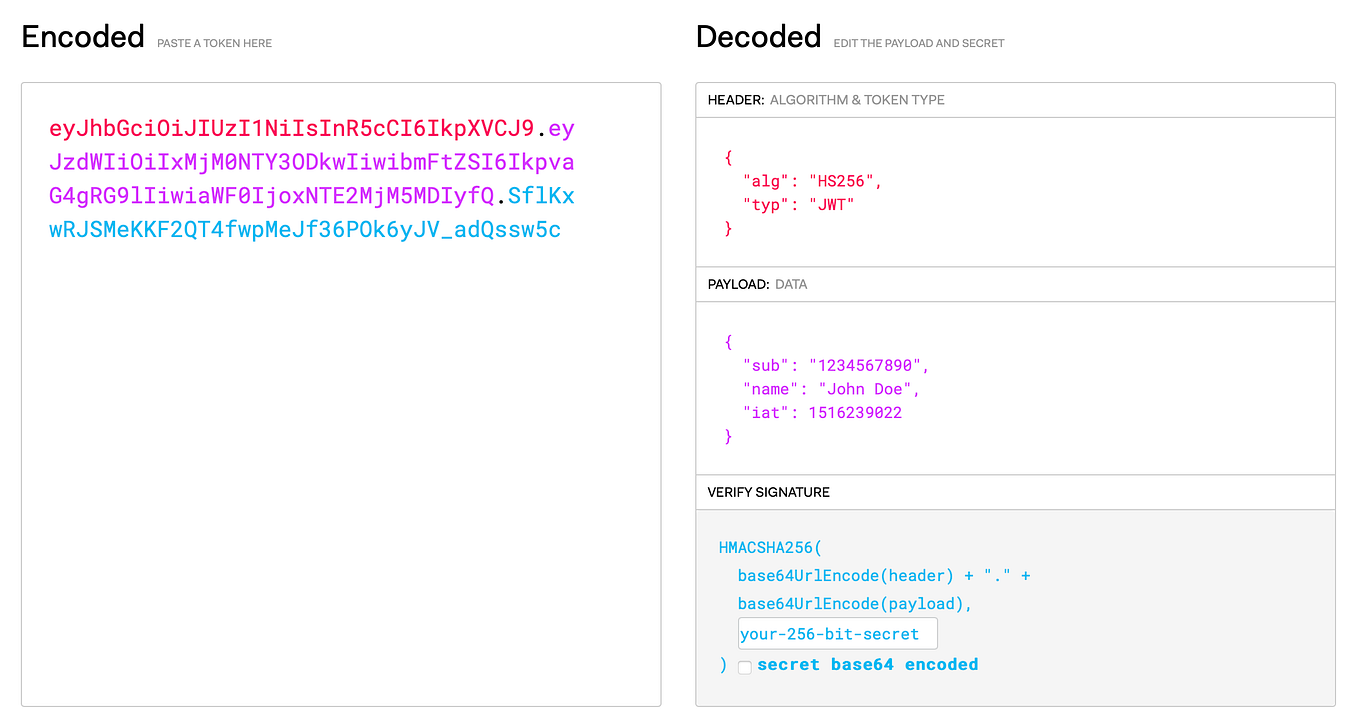
Implementing Json Web Token Jwt Authentication Using Spring Security Welcome to our guide on implementing token based authentication with spring boot and spring security using json web tokens (jwt). Learn how to implement jwt authentication in spring boot 3.x.x with this step by step guide. secure your rest apis with json web tokens, explore best practices, and enhance security using spring security and bcrypt. This tutorial will guide you through implementing jwt (json web token) authentication in a spring boot application using spring security with jdbc template. jwt (json web token) is a compact, url safe way of representing claims transferred between two parties. Securing rest apis is a part of building enterprise applications. spring security uses session based authentication, but in modern distributed systems, jwt (json web token) is preferred as it provides a stateless, scalable and secure way of handling authentication. In this tutorial, we’ll discuss how to get our spring security oauth2 implementation to make use of json web tokens. we’re also continuing to build on the spring rest api oauth2 angular article in this oauth series. In this tutorial, i’m happy to guide you through the development of securing rest api end points using jwt and spring security in a spring based application, from scratch.
Comments are closed.