Journeys With Risk Based Authentication
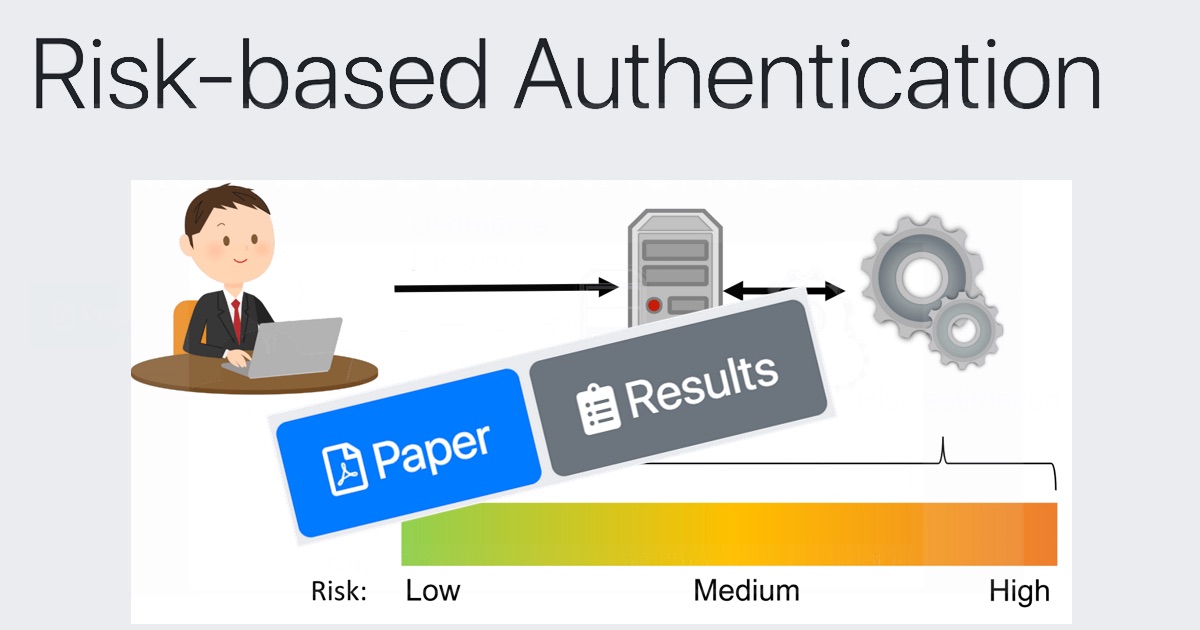
Risk Based Authentication Improves Password Security Without Assigns a risk score in real time that guides the authentication flow. enables seamless access for low risk users, while stepping up verification for suspicious activities. Skip the old, static logins—embrace adaptive security that evolves with every click. customize authentication journeys using risk based insights for seamless.
Open Source Risk Based Authentication In this use case, we’ll demonstrate how to build a simple journey with risk based authentication (rba) rules to determine what outcomes to take for certain risk score ranges. Learn risk based authentication strategies and best practices to strengthen identity security, reduce fraud, and improve user experience. This blog post covers these challenges and explains how a unified risk based authentication platform prevents ato fraud and improves the user experience (ux) while significantly reducing complexity and costs. Learn how risk based authentication (rba) enhances ciam security, improves user experience, and ensures regulatory compliance. explore implementation, risk scoring, and best practices.
Rba Risk Based Authentication Github This blog post covers these challenges and explains how a unified risk based authentication platform prevents ato fraud and improves the user experience (ux) while significantly reducing complexity and costs. Learn how risk based authentication (rba) enhances ciam security, improves user experience, and ensures regulatory compliance. explore implementation, risk scoring, and best practices. Explore key considerations for implementing risk based authentication (rba) to enhance security. learn about adaptive authentication, risk assessment, integration strategies, and maintaining user experience. Learn what risk based authentication is, how it works, key benefits, and real world use cases to strengthen security without adding login friction. Learn about risk based authentication (rba) and how it enhances security. explore examples, challenges, and tips for implementing rba in your organization. Journeys provide fine grained authentication by allowing multiple paths and decision points throughout the authentication flow. use them to build complex authorization scenarios, while offering a streamlined login experience to users.
Github Saksham1605 Risk Based Authentication Explore key considerations for implementing risk based authentication (rba) to enhance security. learn about adaptive authentication, risk assessment, integration strategies, and maintaining user experience. Learn what risk based authentication is, how it works, key benefits, and real world use cases to strengthen security without adding login friction. Learn about risk based authentication (rba) and how it enhances security. explore examples, challenges, and tips for implementing rba in your organization. Journeys provide fine grained authentication by allowing multiple paths and decision points throughout the authentication flow. use them to build complex authorization scenarios, while offering a streamlined login experience to users.
Authentication Journeys Learn about risk based authentication (rba) and how it enhances security. explore examples, challenges, and tips for implementing rba in your organization. Journeys provide fine grained authentication by allowing multiple paths and decision points throughout the authentication flow. use them to build complex authorization scenarios, while offering a streamlined login experience to users.
Cover
Comments are closed.