What About Risk Based Authentication
Risk Based Authentication Improves Password Security Without Risk based authentication assesses the probability of account compromise with each login. if the request seems unusual or suspect, the user must do something extra to gain access. Risk based authentication (rba) is an authentication method in which varying levels of stringency are applied to a system's authentication process based on the likelihood that access to that system could result in its compromise.
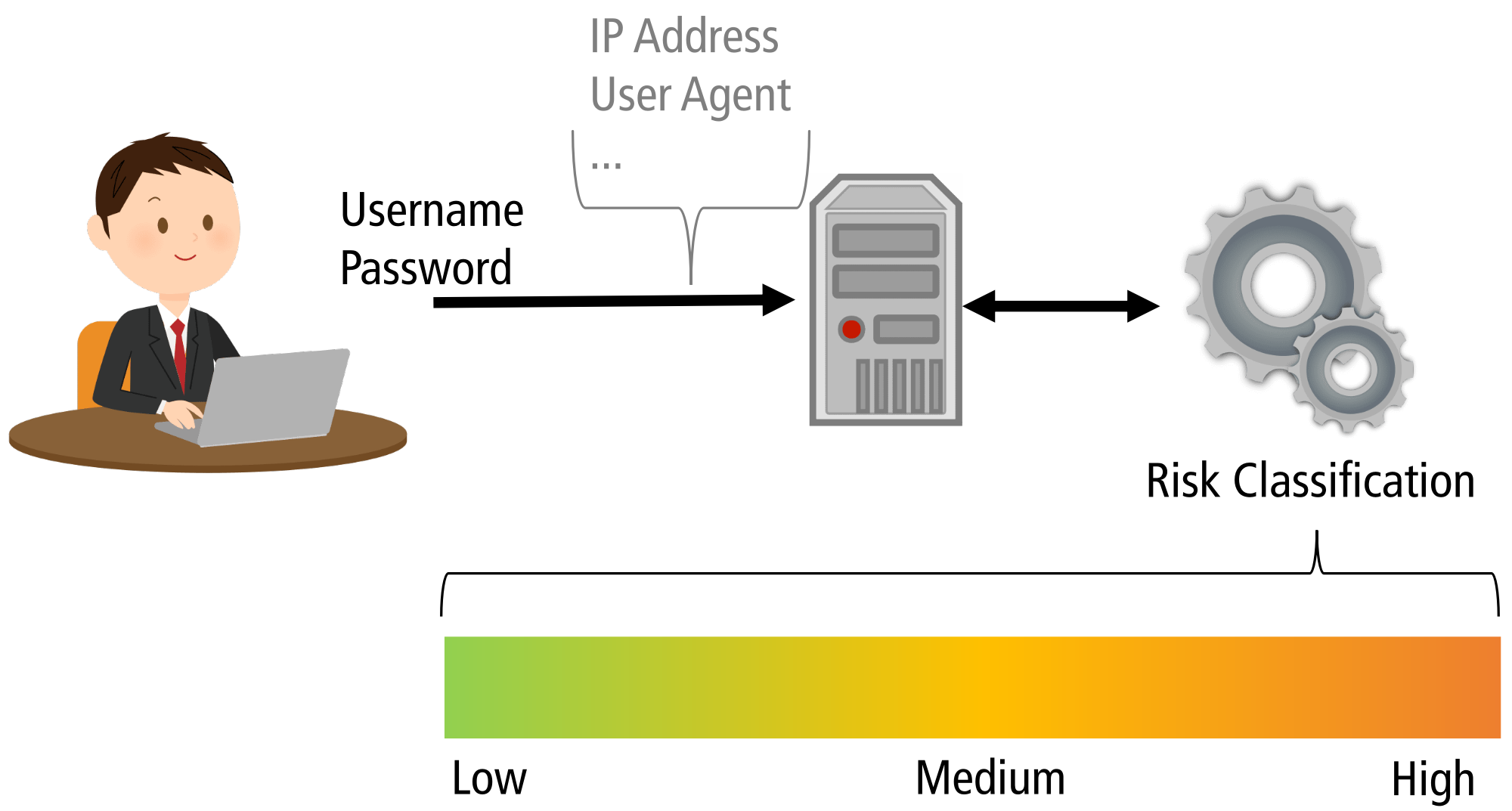
Media Risk Based Authentication In a risk based authentication system, the institution decides if additional authentication is necessary. if the risk is deemed appropriate, enhanced authentication will be triggered, such as a one time password delivered via an out of band communication. On a low risk (e.g. same device as always), access to the website is granted. on a medium risk (e.g. unknown device), the website asks for additional information to confirm the claimed identity (e.g. confirmation of email address). on a high risk, access is denied. Discover what is risk based authentication, how it works, key benefits, use cases, and how to choose the right rba solution for stronger security. This article discusses everything you need to know about risk based authentication. learn what rba is and how it works.
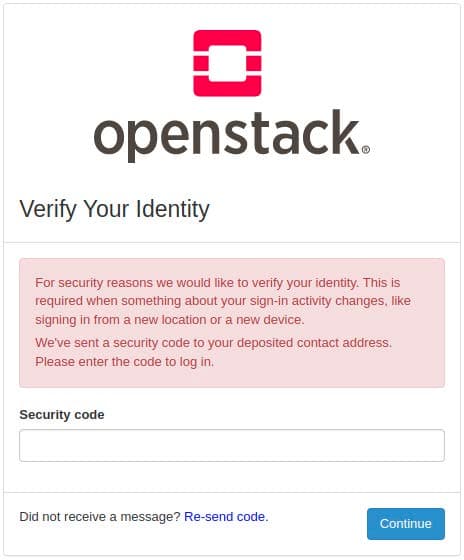
Open Source Risk Based Authentication Discover what is risk based authentication, how it works, key benefits, use cases, and how to choose the right rba solution for stronger security. This article discusses everything you need to know about risk based authentication. learn what rba is and how it works. Explore risk based authentication, how it works, and its benefits in enhancing security by assessing user risks before granting access to sensitive systems. Explore key considerations for implementing risk based authentication (rba) to enhance security. learn about adaptive authentication, risk assessment, integration strategies, and maintaining user experience. Learn about risk based authentication (rba) and how it enhances security. explore examples, challenges, and tips for implementing rba in your organization. First things first, defining those risk factors and thresholds is crucial. you gotta figure out what's considered "risky" for your specific application and users.
Comments are closed.