John The Ripper Tutorial Cybersecurity Tech Hacker Linux
Use John The Ripper Linux Fodfactor In this tutorial, you will see how to install john the ripper on various major linux distributions, and get started with using the program to crack passwords via linux commands. John the ripper (jtr) is one of the most popular open source password crackers, renowned for its flexibility, speed, and support for hundreds of hash algorithms. this blog will demystify password cracking with john the ripper on linux.
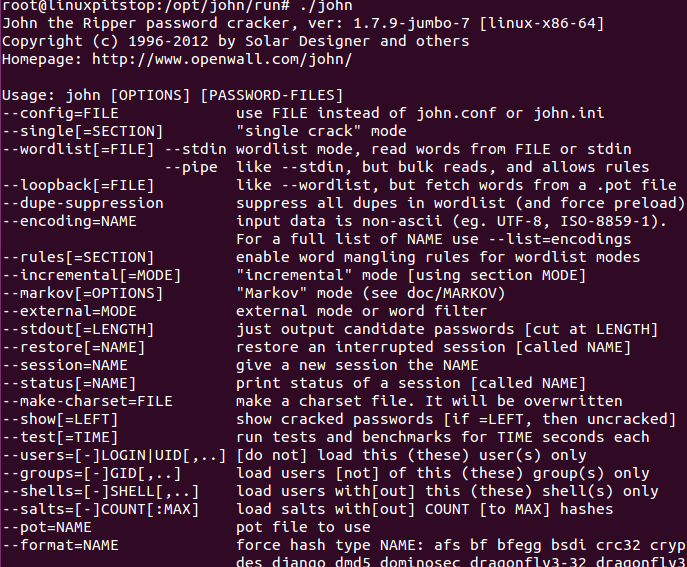
How To Install John The Ripper On Linux A Free Password Cracker This project will help you understand how to crack password hashes using john the ripper on kali linux, highlighting the importance of strong password policies and secure hashing algorithms. John the ripper — crack hashes fast 🚀 (offline password cracking) (theory practical) in this cyber security tutorial, i explain offline password cracking and demonstrate john the. In this lab, you will explore the process of extracting, preparing, and cracking linux password hashes using a powerful tool called john the ripper. understanding how password cracking works is crucial for implementing robust security measures. Here is the working of john the ripper: it takes a password hash (an encrypted form of a password). then it applies different cracking techniques (like dictionary attack, brute force, or incremental mode). if successful, it reveals the original password.
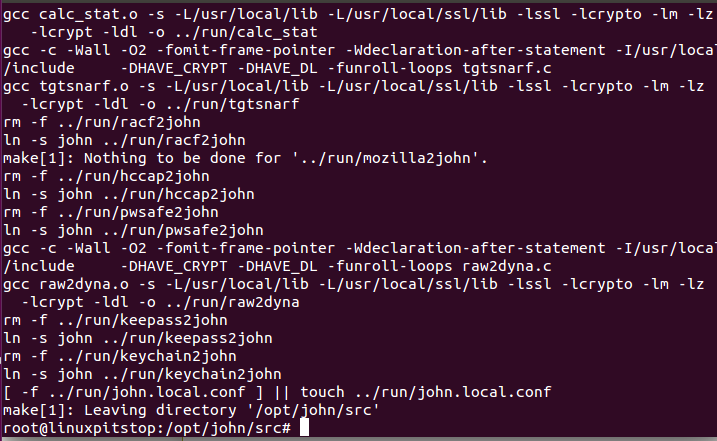
How To Install John The Ripper On Linux A Free Password Cracker In this lab, you will explore the process of extracting, preparing, and cracking linux password hashes using a powerful tool called john the ripper. understanding how password cracking works is crucial for implementing robust security measures. Here is the working of john the ripper: it takes a password hash (an encrypted form of a password). then it applies different cracking techniques (like dictionary attack, brute force, or incremental mode). if successful, it reveals the original password. This repository contains a set of shell scripts designed to facilitate the ethical hacking process using john the ripper, a powerful password cracking tool. the project is divided into two main scripts: prerequisites.sh and pass crack.sh, each serving a distinct purpose in the password cracking workflow. Kali linux, a debian based linux distribution, is pre installed with john the ripper, making it easily accessible for users to conduct password related experiments and security assessments. this blog will guide you through the fundamental concepts, usage methods, common practices, and best practices of using john the ripper in kali linux. This article guides you on how to use john the ripper with the shadow and password files to retrieve plaintext passwords for penetration testing purposes. understanding the etc passwd and etc shadow files. I envision these tutorials as step by step guides or examples for specific use cases e.g., auditing passwords on a windows system (that's one tutorial), then auditing passwords from various unix like systems and windows on a linux system (that's another tutorial).
Comments are closed.