Iot Data Analytics Archives Secure Iot Services

Secure Iot Data Using Blockchain Pdf Internet Of Things Cryptography To address this problem, researchers and practitioners have adopted numerous schemes to aggregate data while preserving data privacy. data privacy is critical to protect against network entities. This comprehensive review identifies and categorizes various recent solutions for secure and privacy preserving data aggregation in iot applications, while also highlighting ongoing research challenges and future directions in the field. this is an ai generated summary, check important information.

Iot Data Analytics Gain Actionable Insights From Your Iot Devices A thorough review is provided on the role of secure systems in navigating the complexities of the iot landscape, promoting resilience against emerging cyber threats, fostering trust in interconnected environments, and ensuring the integrity and privacy of data across diverse domains. Hence, sensitive iot data and rule based programs need to be protected against cyberattacks. to address this important challenge, in this paper, we propose a framework to maintain confidentiality and integrity of iot data and rule based program execution. Overview of all reports and databases published in the last 5 years. Our iot lab monitors global trends and publishes insights into new attack vectors, vulnerability types and best practices for securing connected devices from smart tvs and routers to wearables and phones.

Iot Data Analytics Archives Secure Iot Services Overview of all reports and databases published in the last 5 years. Our iot lab monitors global trends and publishes insights into new attack vectors, vulnerability types and best practices for securing connected devices from smart tvs and routers to wearables and phones. In this paper, we first introduce the concept and features of edge computing, and then propose a number of requirements for its secure data analytics by analyzing potential security threats in edge computing. Discover how to protect iot data privacy: encryption, firmware updates, privacy by design, and regulatory compliance. secure your connected devices confidently in 2025. Through an analysis of current solutions, including encryption techniques, privacy preserving frameworks, and performance optimization strategies, this survey highlights ongoing research efforts and identifies areas requiring further investigation. This paper provides an in depth analysis of state of the art (sota) pp solutions recently developed for iot based systems and applications. we delve into sota pp methods that preserve iot data privacy and categorize them into two scenarios: on device and cloud computing.
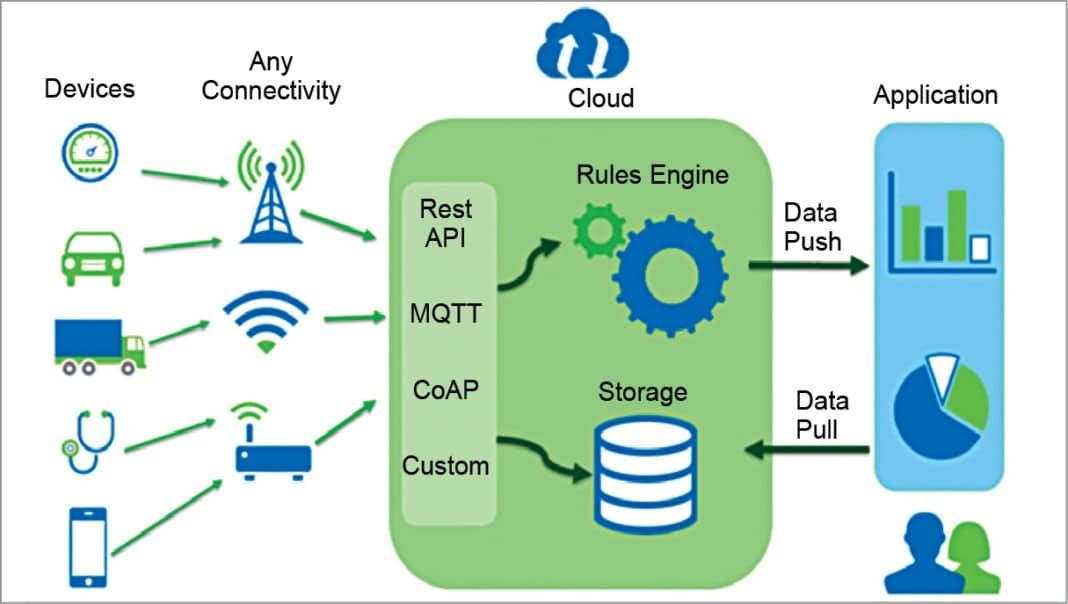
Iot Creating New Avenues For Data Analytics Must Read In this paper, we first introduce the concept and features of edge computing, and then propose a number of requirements for its secure data analytics by analyzing potential security threats in edge computing. Discover how to protect iot data privacy: encryption, firmware updates, privacy by design, and regulatory compliance. secure your connected devices confidently in 2025. Through an analysis of current solutions, including encryption techniques, privacy preserving frameworks, and performance optimization strategies, this survey highlights ongoing research efforts and identifies areas requiring further investigation. This paper provides an in depth analysis of state of the art (sota) pp solutions recently developed for iot based systems and applications. we delve into sota pp methods that preserve iot data privacy and categorize them into two scenarios: on device and cloud computing.

Ieee 2019 Secured Data Collection With Hardware Based Ciphers For Through an analysis of current solutions, including encryption techniques, privacy preserving frameworks, and performance optimization strategies, this survey highlights ongoing research efforts and identifies areas requiring further investigation. This paper provides an in depth analysis of state of the art (sota) pp solutions recently developed for iot based systems and applications. we delve into sota pp methods that preserve iot data privacy and categorize them into two scenarios: on device and cloud computing.

Iot Data Analytics Services Integration Visualization Yalantis
Comments are closed.