Ios Hacking Inter App Communication

Guide To Hacking Ios Applications In the third video in our ios application hacking series, we’ll take a look at widely used mechanisms for inter app communication and how they can be abused when deployed insecurely. Learn how inter process communication (ipc) works in ios, common ipc security issues, real world exploitation techniques with commands, and how attackers abuse xpc, url schemes, and mach ports.

Hacker101 Ios Hacking Compared to android's extensive binder ipc facilities, ios offers very few ipc (inter process communication) options, minimizing the potential attack surface. uniform hardware and tight hardware software integration create another security advantage. In this comprehensive guide, we delve into the world of ios security from an offensive perspective, shedding light on the various techniques and methodologies used by attackers to compromise ios devices and infiltrate their sensitive data. The focus is on vulnerabilities in the applications’ code and only marginally covers general ios system security, darwin security, c objc c memory safety, or high level application security. Explore inter app communication mechanisms in ios and their potential security vulnerabilities in this 15 minute video from hackerone's ios application hacking series.

Apple Warns Iphone Users Over Hacking Risk And What You Need To Do To The focus is on vulnerabilities in the applications’ code and only marginally covers general ios system security, darwin security, c objc c memory safety, or high level application security. Explore inter app communication mechanisms in ios and their potential security vulnerabilities in this 15 minute video from hackerone's ios application hacking series. This section provides a comprehensive examination of ios security architecture and penetration testing methodologies. using corellium's virtualized environment, students gain hands on experience analyzing ios security controls, application data storage, and inter app communications. It is important that communication with this web application is secure because it is used for both device communication and profile administration. the setup process asks you to select an ssl certificate to use for the web service. Our approach statically analyzes the sensitivity and context of each inter app flow based on inter component communication (icc) between communicating apps, and defines fine grained security policies for inter app icc risk classification. This paper describes the creation of a malicious software (swishhijacker) and how it could be used for exploiting a benign app by using the inter app communication mechanisms on ios and the app2app api.

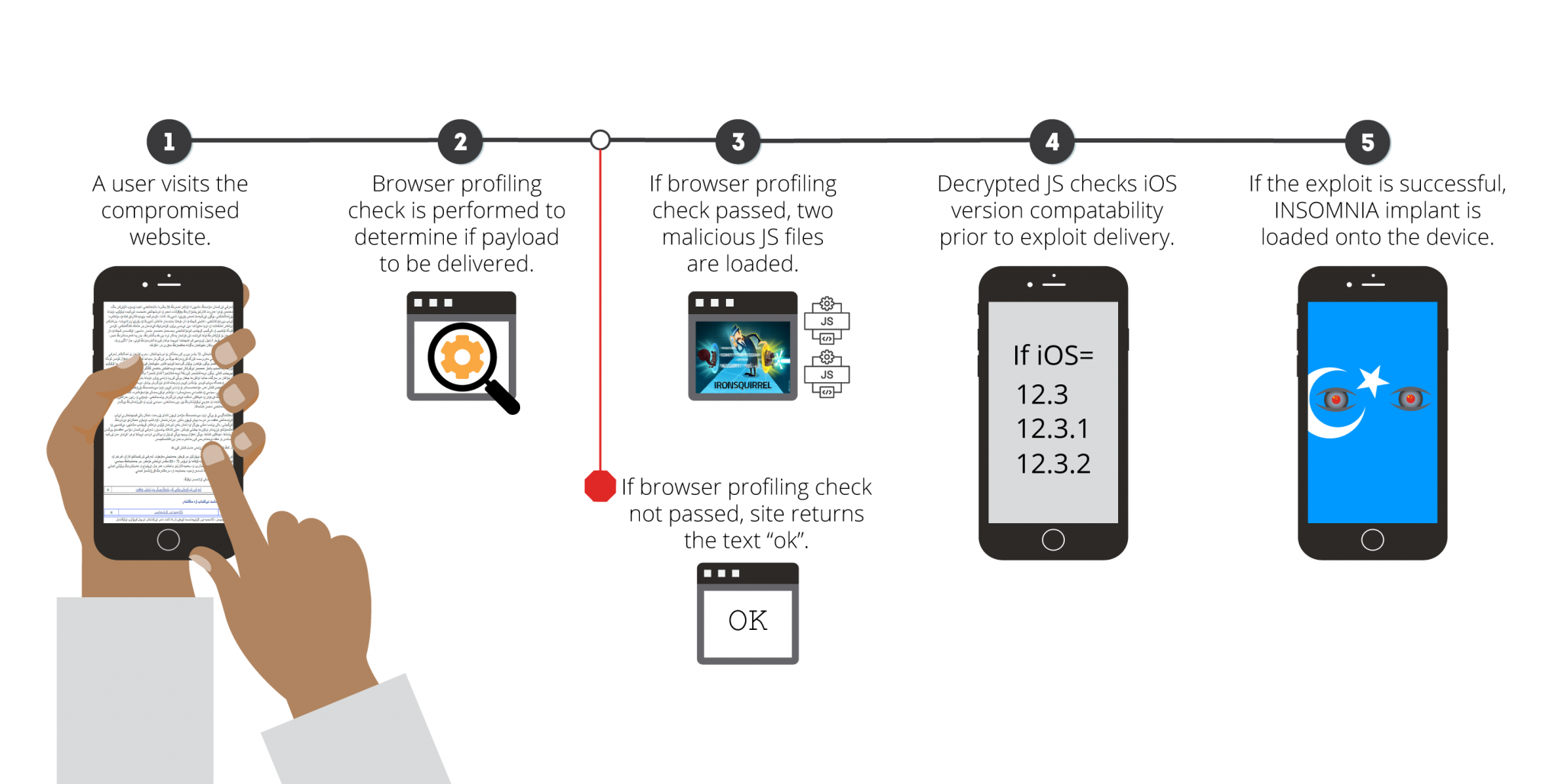
Mysterious Ios Attack Changes Everything We Know About Iphone Hacking This section provides a comprehensive examination of ios security architecture and penetration testing methodologies. using corellium's virtualized environment, students gain hands on experience analyzing ios security controls, application data storage, and inter app communications. It is important that communication with this web application is secure because it is used for both device communication and profile administration. the setup process asks you to select an ssl certificate to use for the web service. Our approach statically analyzes the sensitivity and context of each inter app flow based on inter component communication (icc) between communicating apps, and defines fine grained security policies for inter app icc risk classification. This paper describes the creation of a malicious software (swishhijacker) and how it could be used for exploiting a benign app by using the inter app communication mechanisms on ios and the app2app api.
Facebook Shuts Down Hackers Who Infected Ios And Android Devices Ars Our approach statically analyzes the sensitivity and context of each inter app flow based on inter component communication (icc) between communicating apps, and defines fine grained security policies for inter app icc risk classification. This paper describes the creation of a malicious software (swishhijacker) and how it could be used for exploiting a benign app by using the inter app communication mechanisms on ios and the app2app api.
Comments are closed.