Intrusion Detection System Ids Final Presentation

Intrusion Detection System Ids Pdf It defines intrusion, intrusion detection, and intrusion prevention. it explains the components of an ids including audit data, detection models, and detection and decision engines. Ids final presentation free download as powerpoint presentation (.ppt .pptx), pdf file (.pdf), text file (.txt) or view presentation slides online.

Chapter 4 Intrusion Detection System Ids 2 Pdf Computing Software Intrusion detection is the process of identifying and responding to malicious activity on computing and network resources. learn about the categories, characteristics, and motivations behind ids, and why it's crucial for detecting and reacting to attacks. understand the different kinds of. This research focuses on the development of an intrusion detection system (ids) utilizing the k means clustering algorithm to enhance detection rates while minimizing false positives. Learn about intrusion detection systems (ids), anomaly vs rule based detection, and network vs host based systems. includes snort nids demo. Intrusion detection system (ids) and intrusion prevention system (ips) monitor network traffic to detect and prevent malicious activities. these systems are either implemented on a dedicated hardware or implemented as applications on a general purpose server.
How To Set Up An Intrusion Detection System Ids Learn about intrusion detection systems (ids), anomaly vs rule based detection, and network vs host based systems. includes snort nids demo. Intrusion detection system (ids) and intrusion prevention system (ips) monitor network traffic to detect and prevent malicious activities. these systems are either implemented on a dedicated hardware or implemented as applications on a general purpose server. What is an ids? definition: a piece of software monitors a computer system to detect: intrusion: unauthorized attempts to use the system misuse: abuse of existing privileges responds: log activity notify a designated authority take appropriate countermeasures why use an ids?. Grab the ingenious ppt collections of intrusion detection systems ids presentation templates and google slides. Transcript and presenter's notes title: intrusion detection systems ids 1 intrusion detection systems (ids). Overview concept: “an intrusion detection system is required to detect all types of malicious network traffic and computer usage that can't be detected by a conventional firewall.
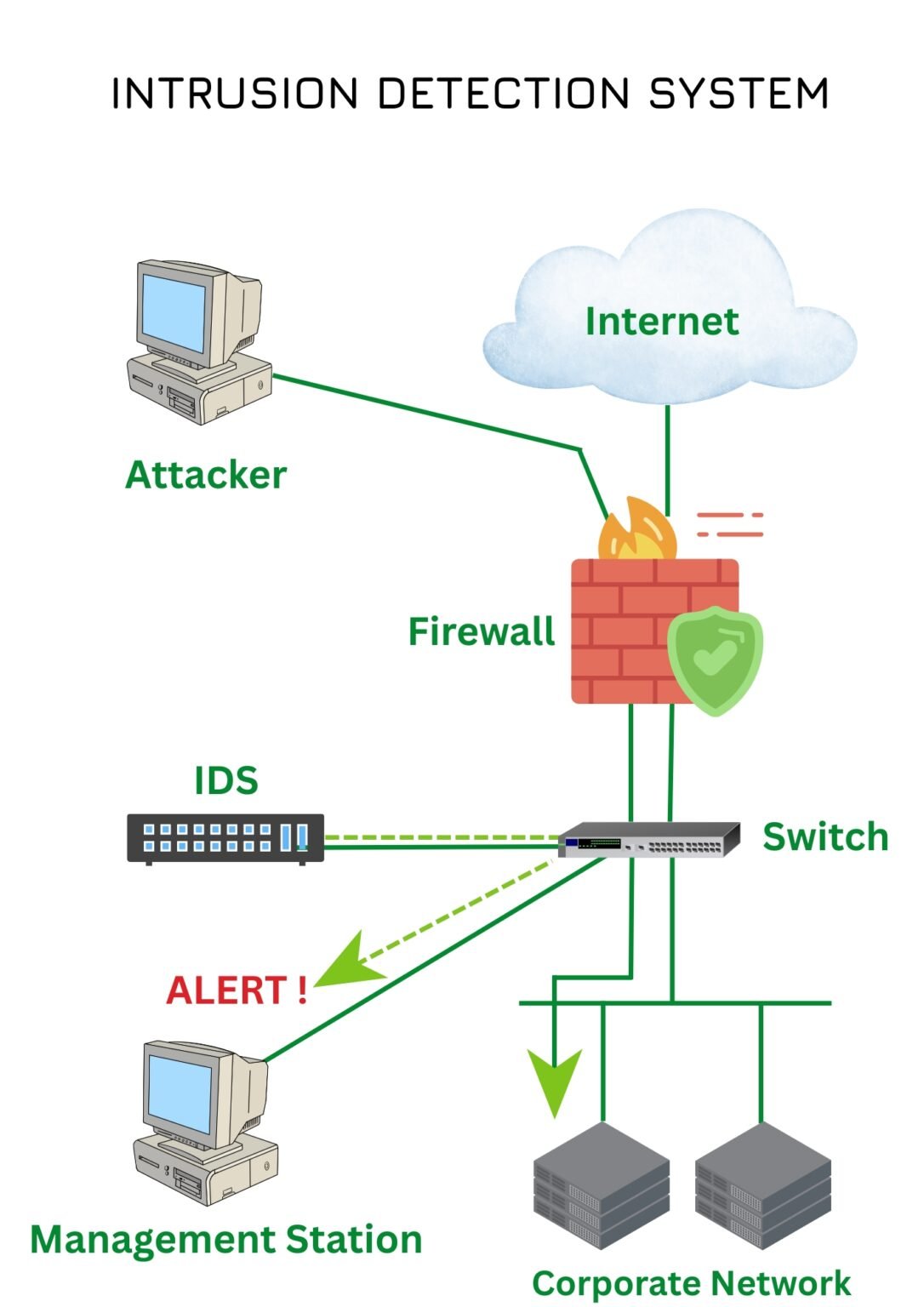
Intrusion Detection System Ids Insight Technology Pvt Ltd What is an ids? definition: a piece of software monitors a computer system to detect: intrusion: unauthorized attempts to use the system misuse: abuse of existing privileges responds: log activity notify a designated authority take appropriate countermeasures why use an ids?. Grab the ingenious ppt collections of intrusion detection systems ids presentation templates and google slides. Transcript and presenter's notes title: intrusion detection systems ids 1 intrusion detection systems (ids). Overview concept: “an intrusion detection system is required to detect all types of malicious network traffic and computer usage that can't be detected by a conventional firewall.

Ppt Intrusion Detection Systems Ids Powerpoint Presentation Free Transcript and presenter's notes title: intrusion detection systems ids 1 intrusion detection systems (ids). Overview concept: “an intrusion detection system is required to detect all types of malicious network traffic and computer usage that can't be detected by a conventional firewall.
Comments are closed.