Introduction To Gvisor Sandboxed Linux Container Runtime

Containerd Linux Complete Guide To Industry Standard Container Runtime Gvisor is an open source linux compatible sandbox that runs anywhere existing container tooling does. it enables cloud native container security and portability. gvisor leverages years of experience isolating production workloads at google. Gvisor includes an open container initiative (oci) runtime called runsc that makes it easy to work with existing container tooling. the runsc runtime integrates with docker and kubernetes, making it simple to run sandboxed containers.
Containerd Linux Complete Guide To Industry Standard Container Runtime Introducing gvisor, a new kind of sandbox that helps provide secure isolation for containers, while being more lightweight than a virtual machine (vm). Emma haruka iwao introduces the architecture of gvisor and its benefits and discusses differences between other isolation mechanisms. Learn how to install and configure gvisor as a container runtime on talos linux for sandboxed workload execution and enhanced container security. Overview gvisor provides an oci compliant container runtime called runsc (run sandboxed container). the runtime manages the complete lifecycle of containers, from creation through execution to termination.
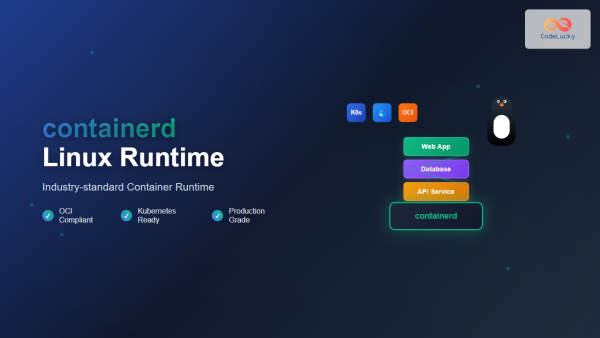
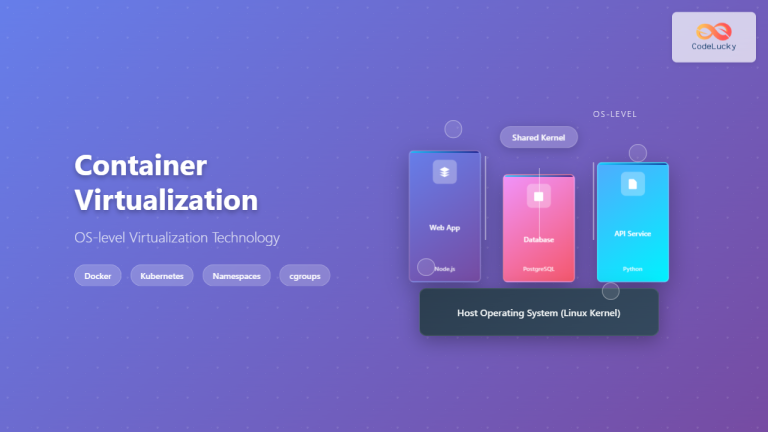
Cri O Linux Complete Guide To Lightweight Container Runtime For Learn how to install and configure gvisor as a container runtime on talos linux for sandboxed workload execution and enhanced container security. Overview gvisor provides an oci compliant container runtime called runsc (run sandboxed container). the runtime manages the complete lifecycle of containers, from creation through execution to termination. What is gvisor? at its core, gvisor is an application kernel, written in the memory safe language go, that provides an additional layer of isolation between containerized applications and the host operating system. Google’s gvisor is a solution to this issue, offering an additional layer of security by isolating the kernel of each container from the host os. this blog will explore how gvisor works and. Gvisor is an open source application kernel developed by google that sandboxes containers by intercepting system calls in user space. it sits between your containerised workload and the host kernel, handling syscalls through its own sandboxed process rather than passing them directly to the host. this article covers how gvisor works, what its components do, where it fits against containers and. This guide will show you exactly how to implement gvisor to achieve military grade sandbox isolation, complete with production ready python automation, performance benchmarks, and real world deployment strategies.

Google Open Sources Gvisor A Sandboxed Container Runtime Techcrunch What is gvisor? at its core, gvisor is an application kernel, written in the memory safe language go, that provides an additional layer of isolation between containerized applications and the host operating system. Google’s gvisor is a solution to this issue, offering an additional layer of security by isolating the kernel of each container from the host os. this blog will explore how gvisor works and. Gvisor is an open source application kernel developed by google that sandboxes containers by intercepting system calls in user space. it sits between your containerised workload and the host kernel, handling syscalls through its own sandboxed process rather than passing them directly to the host. this article covers how gvisor works, what its components do, where it fits against containers and. This guide will show you exactly how to implement gvisor to achieve military grade sandbox isolation, complete with production ready python automation, performance benchmarks, and real world deployment strategies.
Comments are closed.