Introduction To Google Hacking Database Pptx

New Google Hacking Database 2024 Pdf Computer File Computing It highlights methods for finding security vulnerabilities on poorly constructed web applications and offers examples of combined search queries to enhance results. Run regular vulnerability scans against your site, these usually already use popular google dorks queries and can be pretty effective in detecting the most common ones.

Google Hacking Database Ghdb Google Dorks Osint Recon Pdf Web enabled network devices • the google webspider often encounters web enabled devices. these allow an administrator to query their status or manage their configuration using a web browser. This chapter discusses using google search techniques to find security vulnerabilities on websites. it covers both basic operators like , , and " to refine searches, as well as advanced operators like allintext:, filetype:, and intitle: to search specific fields. This document provides an introduction to "google hacking", which is using google searches and advanced operators to uncover sensitive information on websites that may have been inadvertently exposed. It demonstrates how to use these individually and combined, such as "intitle:index finances.xls" to find excel files indexed on websites. the goal of google hacking is to search like a hacker to find sensitive information exposed online. download as a pdf, pptx or view online for free.
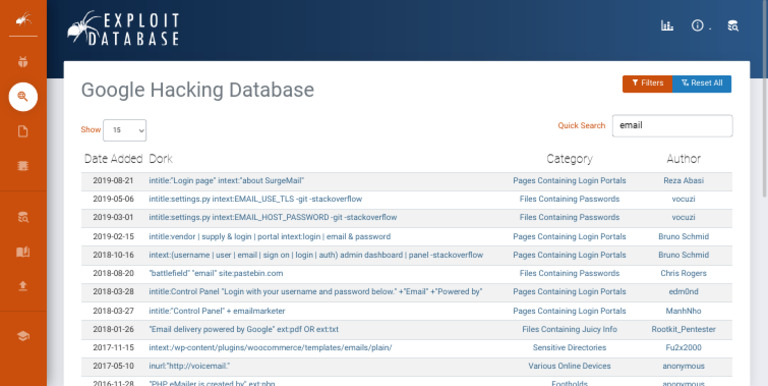
Google Hacking Database Ghdb Google Dorks Osint Recon Pdf This document provides an introduction to "google hacking", which is using google searches and advanced operators to uncover sensitive information on websites that may have been inadvertently exposed. It demonstrates how to use these individually and combined, such as "intitle:index finances.xls" to find excel files indexed on websites. the goal of google hacking is to search like a hacker to find sensitive information exposed online. download as a pdf, pptx or view online for free. This document provides an overview of google hacking techniques. it explains that google hacking involves using google search operators and modifiers to identify vulnerabilities on websites. It discusses the use of various search engines and tools for harvesting information, as well as google hacks for uncovering sensitive data. recommendations are provided for improving security by limiting web accessible information and understanding the tools and techniques discussed. Google dorks, also known as google hacking, involves using specific search operators and techniques on google to find sensitive information on websites. some key points made in the document include: google dorking uses operators like "site:", "filetype:", "intitle:", and "inurl:" to refine search results and maximize search value. The google hacker‘s guide: understanding and defending against the google hacker. retrieved january 20, 2010, from encription website: encription.co.uk downloads the google hackers guide v1.0.pdf.

Google Hacking Database Ghdb Google Dorks Osint Recon2 Pdf This document provides an overview of google hacking techniques. it explains that google hacking involves using google search operators and modifiers to identify vulnerabilities on websites. It discusses the use of various search engines and tools for harvesting information, as well as google hacks for uncovering sensitive data. recommendations are provided for improving security by limiting web accessible information and understanding the tools and techniques discussed. Google dorks, also known as google hacking, involves using specific search operators and techniques on google to find sensitive information on websites. some key points made in the document include: google dorking uses operators like "site:", "filetype:", "intitle:", and "inurl:" to refine search results and maximize search value. The google hacker‘s guide: understanding and defending against the google hacker. retrieved january 20, 2010, from encription website: encription.co.uk downloads the google hackers guide v1.0.pdf.

Google Hacking Pdf Google dorks, also known as google hacking, involves using specific search operators and techniques on google to find sensitive information on websites. some key points made in the document include: google dorking uses operators like "site:", "filetype:", "intitle:", and "inurl:" to refine search results and maximize search value. The google hacker‘s guide: understanding and defending against the google hacker. retrieved january 20, 2010, from encription website: encription.co.uk downloads the google hackers guide v1.0.pdf.
Comments are closed.