Introduction To Data Security Breach Preparedness With Model Data

Introduction To Data Security Breach Preparedness With Model Data All of this means that how a company responds to a data security breach is increasingly important. what follows is a model data security breach preparedne. guide designed to facilitate compliance with legal obligations and to address reputational issues. this is not a “one size fits all” guide that. Introduction to data security breach preparedness with model data security breach preparedness guide download as a pdf or view online for free.

A Closer Look At Data Breach Preparedness Help Net Security We would like to show you a description here but the site won’t allow us. In response to organizations’ increasing vulnerability to data breaches, we present an integrated risk model for data breach management based on a systematic review of the literature. This practice guide can help your organization: detect losses of data confidentiality in your organization. respond to data breach events using your organization’s security architecture. recover from a data breach in a manner that lessens monetary and reputational damage. This playbook is a cyber incident response plan (cirp) supplemental procedure and should be used in conjunction with the cirp to assist in responding to cyber incidents involving data breach or data loss.
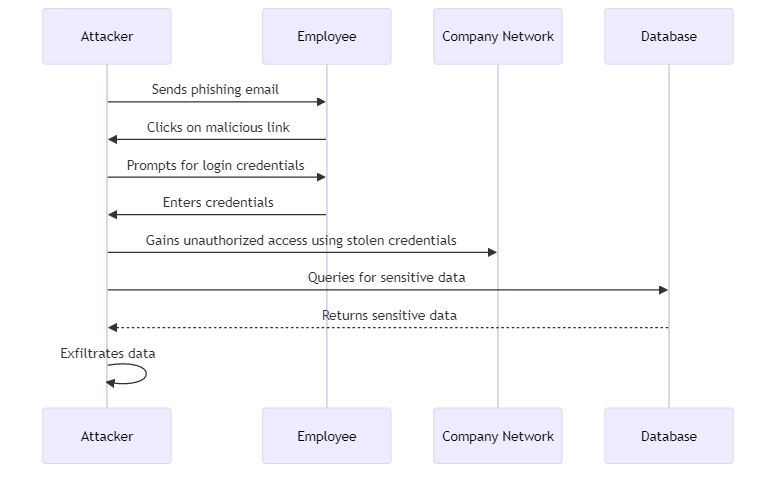
Data Breach This practice guide can help your organization: detect losses of data confidentiality in your organization. respond to data breach events using your organization’s security architecture. recover from a data breach in a manner that lessens monetary and reputational damage. This playbook is a cyber incident response plan (cirp) supplemental procedure and should be used in conjunction with the cirp to assist in responding to cyber incidents involving data breach or data loss. These playbooks provide fceb agencies with a standard set of procedures to identify, coordinate, remediate, recover, and track successful mitigations from incidents and vulnerabilities affecting fceb systems, data, and networks. This template provides a structured approach to managing data breaches, ensuring that your students have a practical tool they can adapt and implement in their organizations. Develop the skills to design, build and operate a comprehensive data protection program. Develop a data breach response plan with a dedicated team, clear roles, and communication protocols. train employees on security best practices and conduct phishing simulations to test their awareness.
Comments are closed.