Into To Malware Analysis Ida Pro V 6 2

Unveiling The Hacker S Mindset With Ida Pro In Malware Analysis By Enjoy the videos and music you love, upload original content, and share it all with friends, family, and the world on . Ida pro is by far the industry standard tool for reverse engineering (and not just malicious code.) the commercial version includes support for a large number of processors, easy analysis of shellcode, and lots of other features.

Unveiling The Hacker S Mindset With Ida Pro In Malware Analysis By Solutions for lab 5 within practical malware analysis. ida pro, an interactive disassembler, is a disassembler for computer programs that generates assembly language source code from an. In this work, a novel approach for the analysis of mobile malware is explored. the mobile malware is analyzed buying the commercially available reverse engineering tools. In this article, you will learn how to use ida pro to analyze malware samples in a systematic and efficient way. Powerful disassembler, decompiler and versatile debugger in one tool. unparalleled processor support. analyze binaries in seconds for any platform.
Practical Malware Analysis Ch 5 Ida Pro Pptx In this article, you will learn how to use ida pro to analyze malware samples in a systematic and efficient way. Powerful disassembler, decompiler and versatile debugger in one tool. unparalleled processor support. analyze binaries in seconds for any platform. Idahunt is a framework to analyze binaries with ida pro and hunt for things in ida pro. it is command line tool to analyse all executable files recursively from a given folder. The third chapter to contain lab assignments is chapter 5: “ida pro”. as the name suggests, this chapter discusses the use of the interactive disassembler tool. ida’s true power comes from its interactive ability, and the book gives tips and tricks to assist in performing analysis with ida. The document outlines steps for reverse engineering malware, including analyzing file formats to check for packing, unpacking packed files, disassembling malware, and finding interesting code. The malware might try to detect, using this function, how much time has elapsed since its execution. this can be an anti analysis tactic that tries to prevent the debugging of the malware.
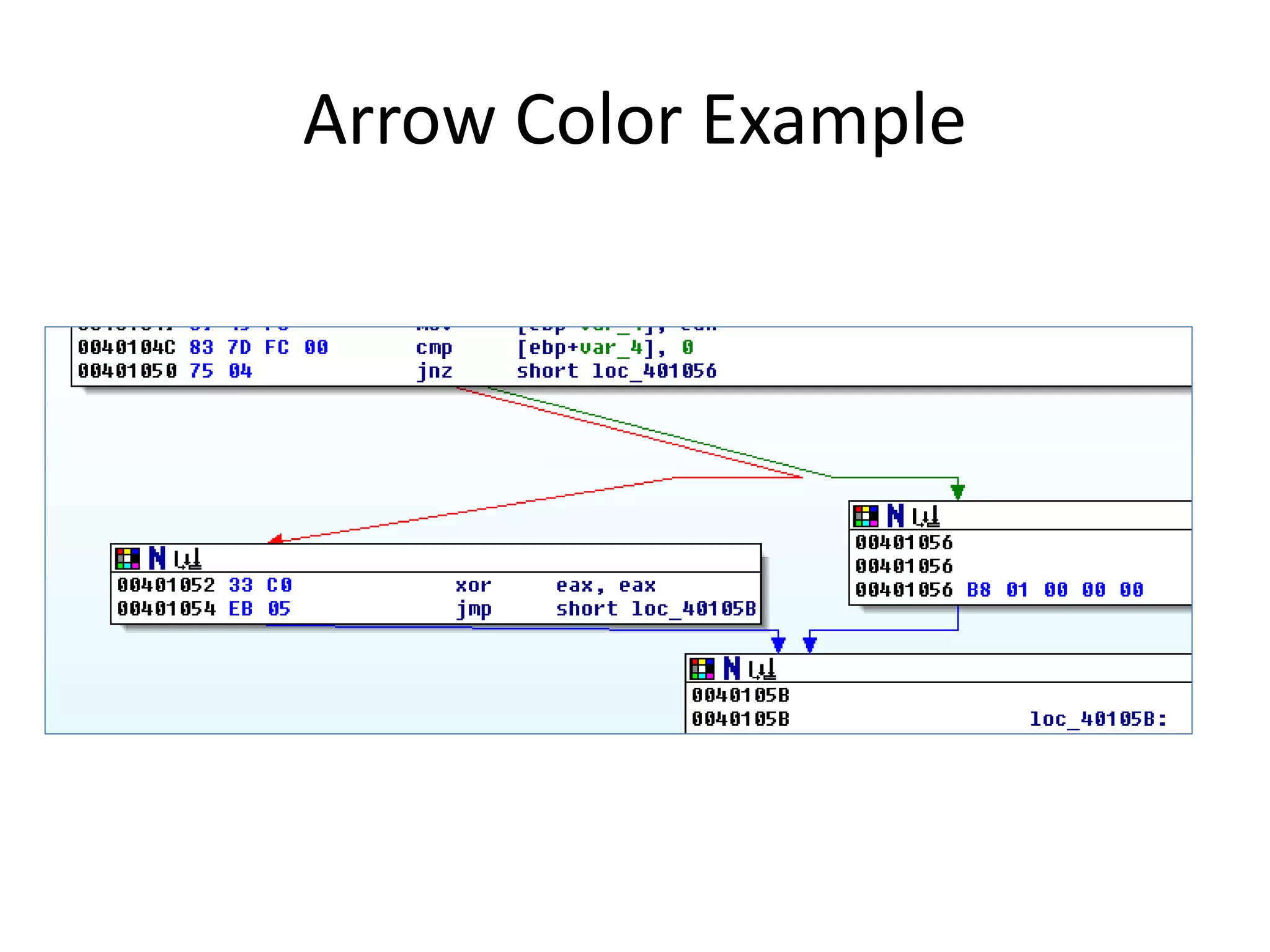
Practical Malware Analysis Ch 5 Ida Pro Pptx Idahunt is a framework to analyze binaries with ida pro and hunt for things in ida pro. it is command line tool to analyse all executable files recursively from a given folder. The third chapter to contain lab assignments is chapter 5: “ida pro”. as the name suggests, this chapter discusses the use of the interactive disassembler tool. ida’s true power comes from its interactive ability, and the book gives tips and tricks to assist in performing analysis with ida. The document outlines steps for reverse engineering malware, including analyzing file formats to check for packing, unpacking packed files, disassembling malware, and finding interesting code. The malware might try to detect, using this function, how much time has elapsed since its execution. this can be an anti analysis tactic that tries to prevent the debugging of the malware.

Practical Malware Analysis Ch 5 Ida Pro Pptx The document outlines steps for reverse engineering malware, including analyzing file formats to check for packing, unpacking packed files, disassembling malware, and finding interesting code. The malware might try to detect, using this function, how much time has elapsed since its execution. this can be an anti analysis tactic that tries to prevent the debugging of the malware.
Comments are closed.