Injecting Dll With Shellcode
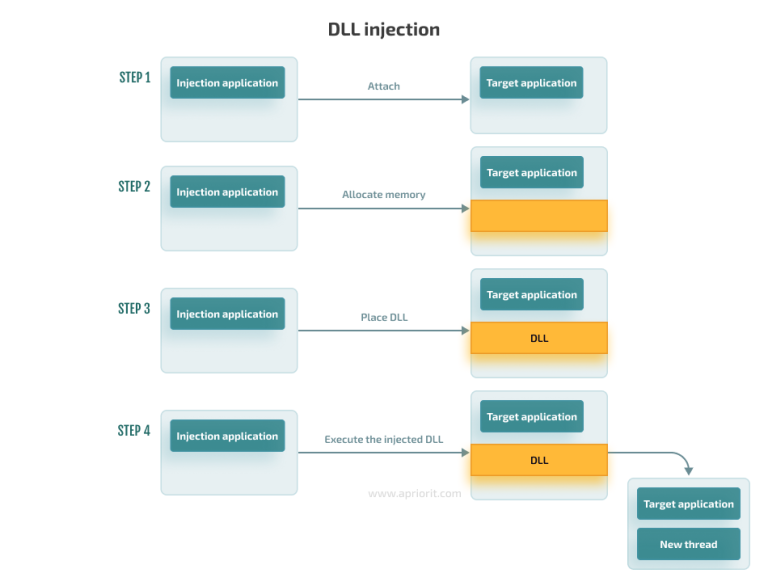
Mitigate Dll Injection Attacks Apriorit Discover how modern malware uses shellcode injection to evade detection. a practical guide for ethical red team research and mastering stealth techniques. Srdi allows for the conversion of dll files to position independent shellcode. it attempts to be a fully functional pe loader supporting proper section permissions, tls callbacks, and sanity checks.
3 Effective Dll Injection Techniques For Setting Api Hooks Apriorit Discover the art of dll injection combined with antivirus evasion techniques. learn how to bypass security measures and advance your red teaming skills. In this lab, i will inject amsi.dll into a notepad.exe process, but this of course could be done with any other dll and process. Injecting shellcode into windows executables with shellter and metasploit is a powerful and stealthy technique for gaining remote access to a system. this method allows you to deliver payloads that can evade detection, providing attackers with persistence and control over the compromised system. Dinjector repository is an accumulation of my code snippets for various shellcode injection techniques using fantastic d invoke api by @thewover and @fuzzysecurity.
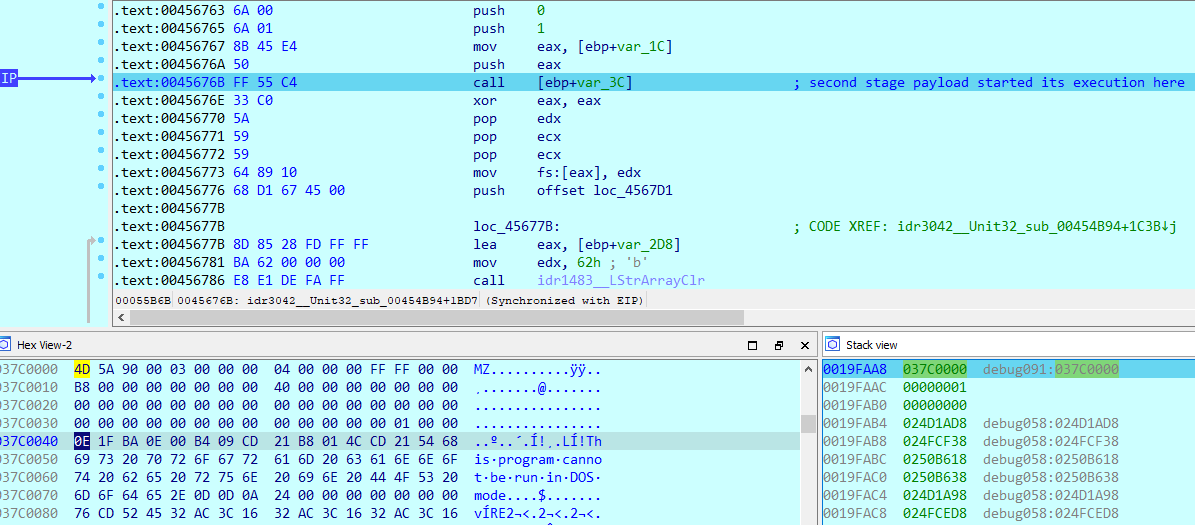
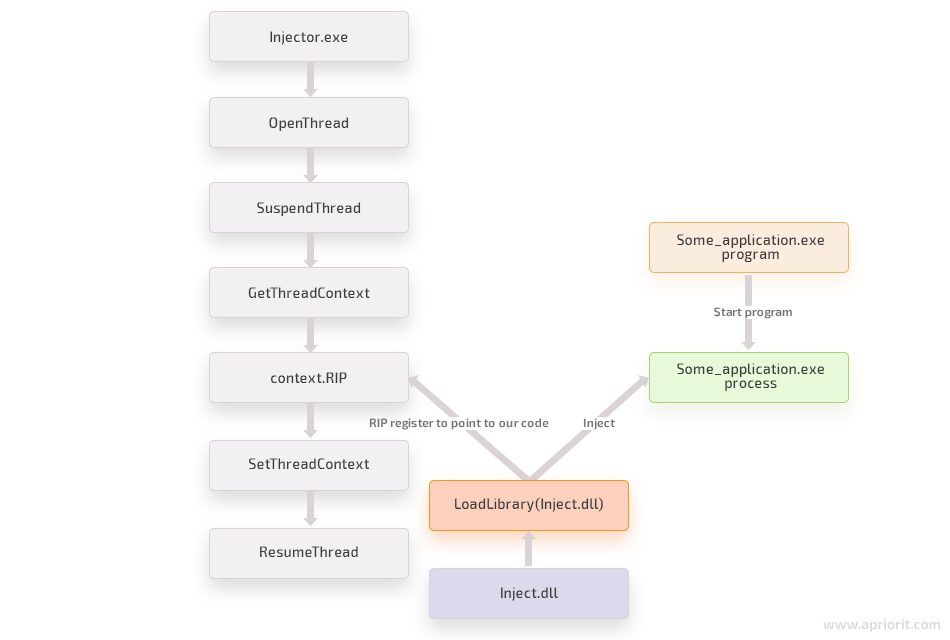
Dbatloader Reloaded Dual Injection And Resilience Injecting shellcode into windows executables with shellter and metasploit is a powerful and stealthy technique for gaining remote access to a system. this method allows you to deliver payloads that can evade detection, providing attackers with persistence and control over the compromised system. Dinjector repository is an accumulation of my code snippets for various shellcode injection techniques using fantastic d invoke api by @thewover and @fuzzysecurity. The y switch invokes dll self registration, loading the dll into the msiexec process and triggering shellcode execution. many security products whitelist msiexec by default. mitre att&ck: t1218.007 — signed binary proxy execution: msiexec rundll32 rundll32.exe is the canonical windows utility for invoking dll functions. This article explores a method of injecting a dll from a windows driver without dropping it to disk, loading it directly from memory before the executable’s entry point. This document provides comprehensive technical documentation of the manual mapping system, the most sophisticated dll injection technique implemented in the guidedhacking injector. Let's do a deep dive on how to write a reflective loader in assembly, that turns any dll into position independent shellcode. in this article i went through the code of creating a reflective loader using go.
Comments are closed.