Information Technology Security Management

Mastering Information Security Management Essential Strategies For Pr This chapter delves into the multifaceted domain of information security management, providing a holistic perspective encompassing seven key subjects. we start by exploring the critical alignment between information security strategies and an organization's overall business strategy. Explore career pathways in information security management. learn what employers expect, discover skills needed, and access isaca resources to support your journey.

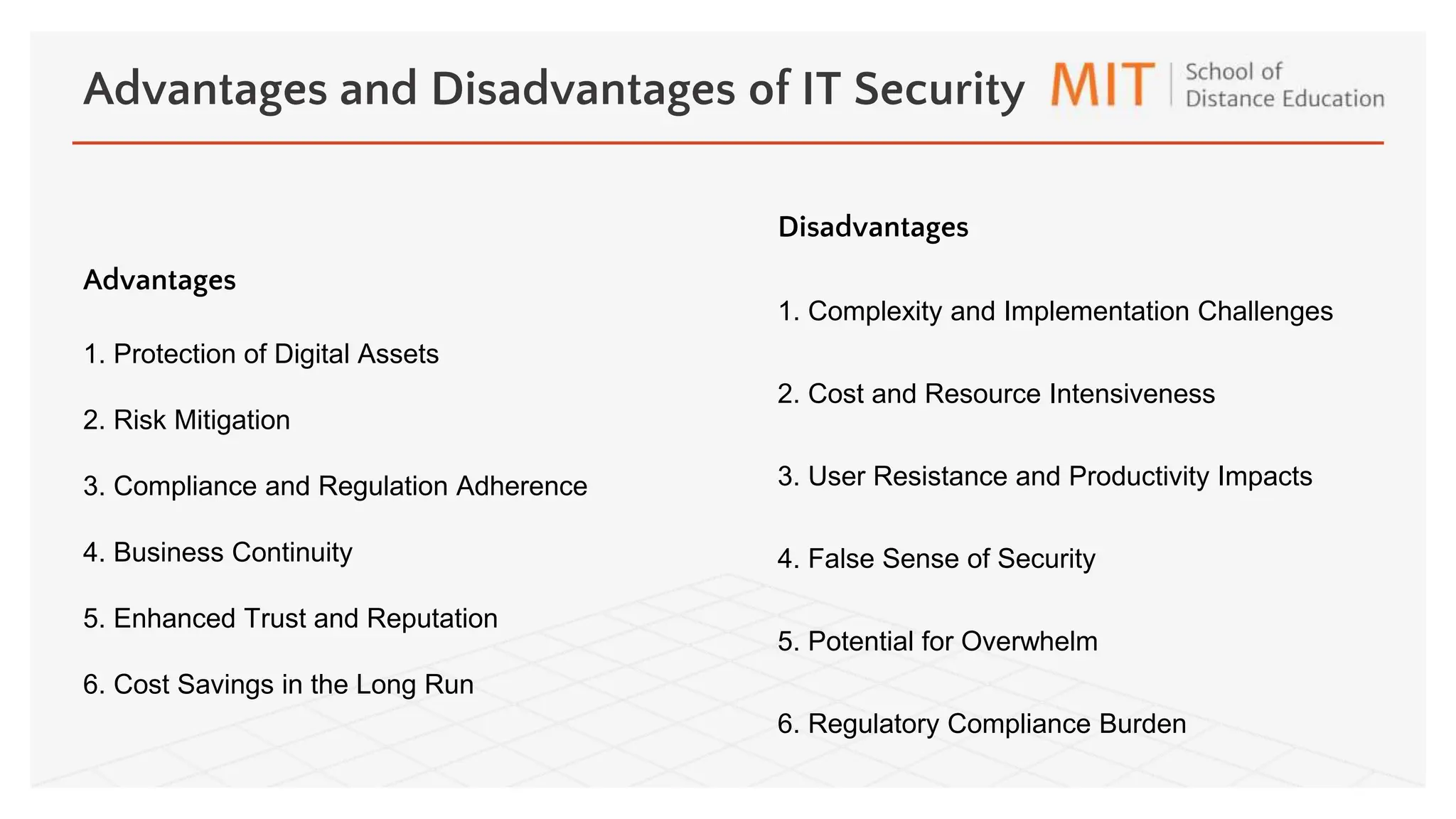
Information Security Management Services Esw Information security management describes the set of policies and procedural controls that it and business organizations implement to secure their informational assets against threats and vulnerabilities. Information security management (ism) comprises strategies and practices to safeguard an organisation’s informational assets from various cyber threats. it aims to guarantee the privacy, security, and accessibility of data. It highlights various types of it security, including network, endpoint, data, application, and cloud security, along with their advantages and disadvantages. Information security management (ism) defines and manages controls that an organization needs to implement to ensure that it is sensibly protecting the confidentiality, availability, and integrity of assets from threats and vulnerabilities.
Information Technology Security Management Pptx It highlights various types of it security, including network, endpoint, data, application, and cloud security, along with their advantages and disadvantages. Information security management (ism) defines and manages controls that an organization needs to implement to ensure that it is sensibly protecting the confidentiality, availability, and integrity of assets from threats and vulnerabilities. Iso 27001 specifies the requirements to plan, establish, implement, operate, monitor, review, maintain and continually improve a management system, as well as prepare, respond and deal with the consequences of information security incidents which are likely to happen. Information security management is a very important issue for anyone working in the field of technology, or for anyone at risk of security breach, who understands the implications of these. Learn more about an information security manager career, including what the job entails, what education and experience it requires, and what you can expect to earn. information security managers oversee cybersecurity measures, detect vulnerabilities, establish safeguards, and respond to incidents. Learn how information security management and operations provides the essential foundation to define, plan, measure, implement, and assess security abilities.
Information Technology Security Management Pptx Iso 27001 specifies the requirements to plan, establish, implement, operate, monitor, review, maintain and continually improve a management system, as well as prepare, respond and deal with the consequences of information security incidents which are likely to happen. Information security management is a very important issue for anyone working in the field of technology, or for anyone at risk of security breach, who understands the implications of these. Learn more about an information security manager career, including what the job entails, what education and experience it requires, and what you can expect to earn. information security managers oversee cybersecurity measures, detect vulnerabilities, establish safeguards, and respond to incidents. Learn how information security management and operations provides the essential foundation to define, plan, measure, implement, and assess security abilities.

Information Technology Security Management Pptx Learn more about an information security manager career, including what the job entails, what education and experience it requires, and what you can expect to earn. information security managers oversee cybersecurity measures, detect vulnerabilities, establish safeguards, and respond to incidents. Learn how information security management and operations provides the essential foundation to define, plan, measure, implement, and assess security abilities.
Information Technology Security Management Pptx
Comments are closed.