Information Security Management

Demonstrating A Robust Iso 27001 Information Security Management System Explore career pathways in information security management. learn what employers expect, discover skills needed, and access isaca resources to support your journey. Learn how to define and manage controls to protect the confidentiality, availability, and integrity of information assets from threats and vulnerabilities. explore the core concepts, standards, and best practices of information security management and system.

Iso 27001 Concept Information Security Management System Isms Information security management (ism) comprises strategies and practices to safeguard an organisation’s informational assets from various cyber threats. it aims to guarantee the privacy, security, and accessibility of data. Information security management describes the set of policies and procedural controls that it and business organizations implement to secure their informational assets against threats and vulnerabilities. An information security management system (isms) is a set of policies and procedures for systematically managing an organization's sensitive data. the goal of an isms is to minimize risk and ensure business continuity by proactively limiting the impact of a security breach. Information security management is defined as the systematic application of management policies, procedures, and practices aimed at establishing context, identifying, analyzing, evaluating, treating, monitoring, and communicating information security risks.
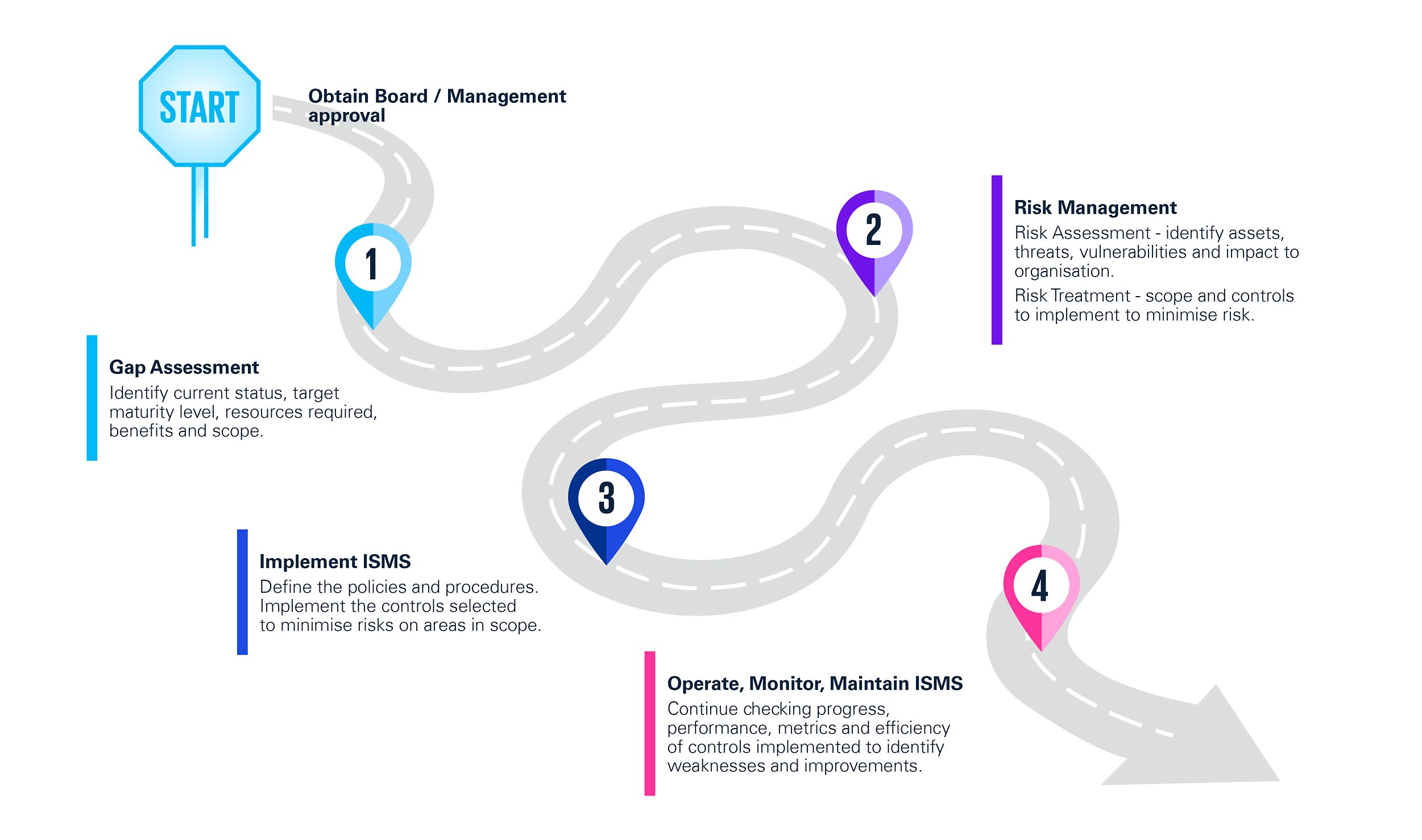
Information Security Management System How To Implement Iso 27001 An information security management system (isms) is a set of policies and procedures for systematically managing an organization's sensitive data. the goal of an isms is to minimize risk and ensure business continuity by proactively limiting the impact of a security breach. Information security management is defined as the systematic application of management policies, procedures, and practices aimed at establishing context, identifying, analyzing, evaluating, treating, monitoring, and communicating information security risks. Discover the essentials of information security management, its objectives, scope, and value in itil for effective data protection and risk management. It seems the information security manager role is constantly evolving—not only are the paths to get to an information security management position different, but the roles and responsibilities among information security professionals differ as well. Learn what information security management is, why it is important, and how it can protect data confidentiality, integrity, and availability. explore the standards and compliance factors that drive information security management, and the benefits of check point's unified cybersecurity platform. Learn how to ensure the confidentiality, integrity and availability of an organization's information, data and it services. explore the common data security policies, frameworks and standards, and security technologies for information security management and operations.

Iso 27001 Information Security Management System Discover the essentials of information security management, its objectives, scope, and value in itil for effective data protection and risk management. It seems the information security manager role is constantly evolving—not only are the paths to get to an information security management position different, but the roles and responsibilities among information security professionals differ as well. Learn what information security management is, why it is important, and how it can protect data confidentiality, integrity, and availability. explore the standards and compliance factors that drive information security management, and the benefits of check point's unified cybersecurity platform. Learn how to ensure the confidentiality, integrity and availability of an organization's information, data and it services. explore the common data security policies, frameworks and standards, and security technologies for information security management and operations.
Comments are closed.