Implementing Phishing Resistant Solution Pdf

Phishing Pdf This fact sheet provides an overview of threats against accounts and systems that use mfa and provides guidance on implementing phishing resistant mfa, which is the most secure form of mfa. This document provides guidance for it leaders on implementing phishing resistant multifactor authentication (mfa) to enhance security against cyber threats. it outlines various methods of mfa, their vulnerabilities, and emphasizes the necessity of adopting phishing resistant forms like fido webauthn as a priority.
Implementing Phishing Resistant Solution Pdf The cybersecurity and infrastructure security agency (cisa) recently (oct 31, 2022) released fact sheets urging all organizations to implement phishing resistant multi factor authentication. Our solutions integrate seamlessly with existing iam infrastructures, enabling organizations to shrink their attack surface and adopt phishing resistant, strong authentication methods. The requirement for phishing resistant mfa considering the prevalence and success of mfa fatigue attacks, governments and security agencies suggest phishing resistant mfa. Once an attacker gains control of a user’s account, they can move laterally within an organization’s network and gain persistence, often going undetected for days. you need to secure your users with phishing resistant authentication and protect against ato attacks.
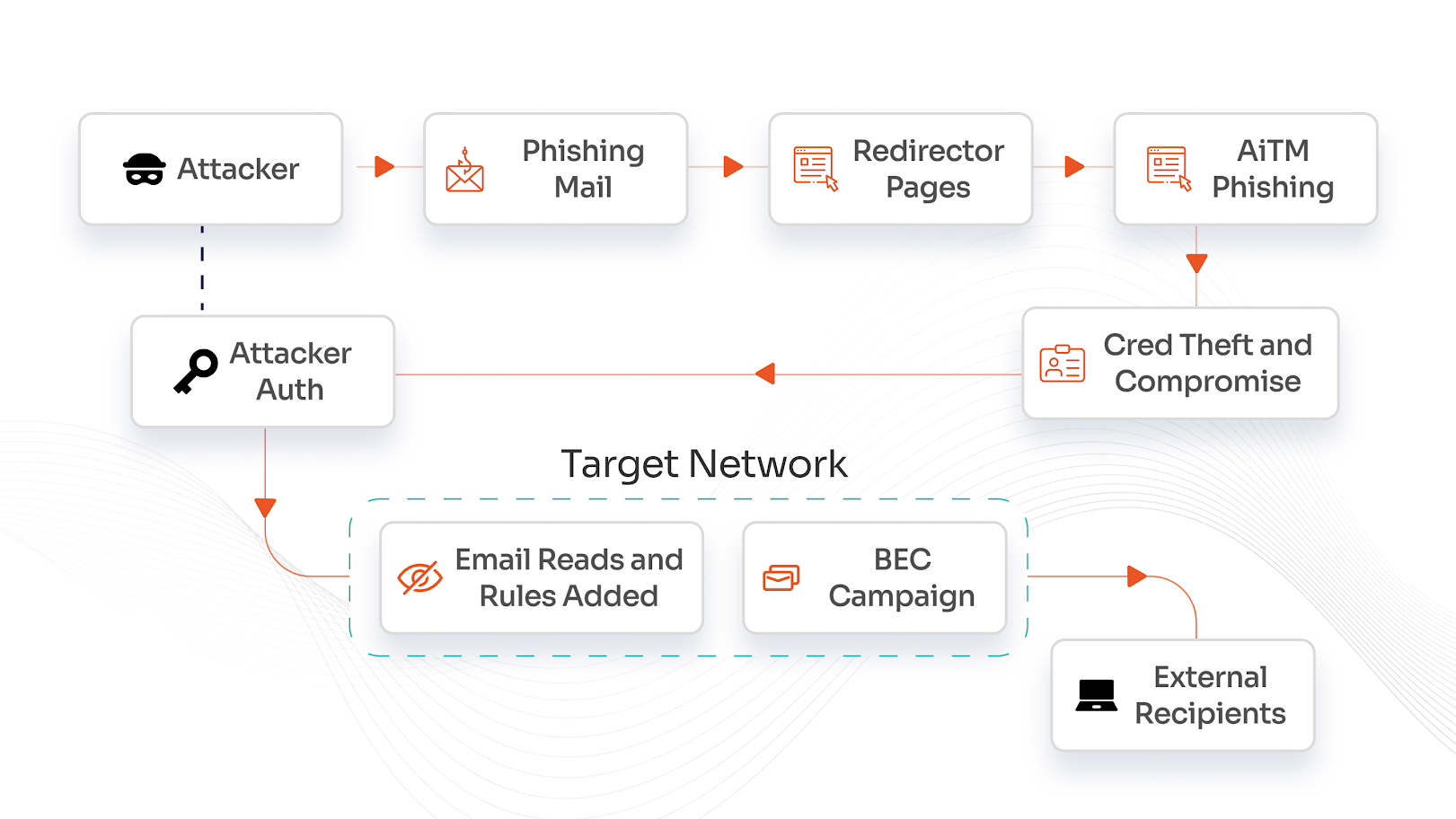
What Is A Phishing Resistant Mfa Solution The requirement for phishing resistant mfa considering the prevalence and success of mfa fatigue attacks, governments and security agencies suggest phishing resistant mfa. Once an attacker gains control of a user’s account, they can move laterally within an organization’s network and gain persistence, often going undetected for days. you need to secure your users with phishing resistant authentication and protect against ato attacks. Part 3: full prevention explains how to achieve comprehensive phishing resistance. the full prevention stage can be achieved by gradually expanding a limited passkey only strategy from the partial prevention stage until passkeys are required in all areas and for all users. This guide will provide you with best practices to enhance your organization’s security posture, focusing on the critical role of phishing resistant multi factor authentication (mfa) and how it fits within the deployment of your planned or existing microsoft ecosystem. For further information, see cisa’s fact sheets for implementing phishing resistant mfa and implementing number matching in mfa applications. note: deploying pki based mfa requires highly mature identity access and management programs and is not widely supported by commonly used services. Aims: this study addresses the current lack of resources and guidelines for the design, implementation and evaluation of anti phishing interventions, by presenting person alized guidelines to.

Expert Panel How To Choose The Right Phishing Protection Solution Part 3: full prevention explains how to achieve comprehensive phishing resistance. the full prevention stage can be achieved by gradually expanding a limited passkey only strategy from the partial prevention stage until passkeys are required in all areas and for all users. This guide will provide you with best practices to enhance your organization’s security posture, focusing on the critical role of phishing resistant multi factor authentication (mfa) and how it fits within the deployment of your planned or existing microsoft ecosystem. For further information, see cisa’s fact sheets for implementing phishing resistant mfa and implementing number matching in mfa applications. note: deploying pki based mfa requires highly mature identity access and management programs and is not widely supported by commonly used services. Aims: this study addresses the current lack of resources and guidelines for the design, implementation and evaluation of anti phishing interventions, by presenting person alized guidelines to.
Comments are closed.