Implementing Jwt For Api Security Api7 Ai
Implementing Jwt For Api Security Api7 Ai This guide provides a comprehensive walkthrough for developers on implementing jwt for robust api security, particularly in conjunction with api gateways. introduction to api security and the need for jwt. Understand how to implement jwt authentication in apache apisix, allowing secure and stateless authentication of api clients using json web tokens.
Implementing Jwt For Api Security Api7 Ai The following example demonstrates how you can use asymmetric algorithms, such as rs256, to sign and validate jwt when implementing jwt for consumer authentication. Learn how to configure apache apisix for secure authentication using oauth 2.0, jwt, and oidc. includes complete configuration examples and best practices. This guide will introduce using jwt auth to protect your apis when using api7 cloud. you can also safeguard services as long as you configure the service's authentication plugin (instead of a specific route). Apache apisix gateway provides multiple security plugins for identity authentication and api verification, including cors, jwt, key auth, openid connect (oidc), keycloak, etc. we put stability and security first. for more information, check here.
Github Codertechweb Jwt Apigateway Security This guide will introduce using jwt auth to protect your apis when using api7 cloud. you can also safeguard services as long as you configure the service's authentication plugin (instead of a specific route). Apache apisix gateway provides multiple security plugins for identity authentication and api verification, including cors, jwt, key auth, openid connect (oidc), keycloak, etc. we put stability and security first. for more information, check here. In the ecosystem, understanding how to implement robust authentication and authorization mechanisms—such as jwt and oauth—along with enforcing proper access controls, is crucial to protect your applications from potential threats. This guide explains, in simple terms, how to secure rest apis with jwt in core, including configuration, token generation, validation, and production best practices. Learn how to secure a api using json web tokens (jwts) with a step by step tutorial that walks through authentication configuration, token issuance, and endpoint protection. In this article, we will explore real world scenarios demonstrating how jwts work in a secure authentication system.
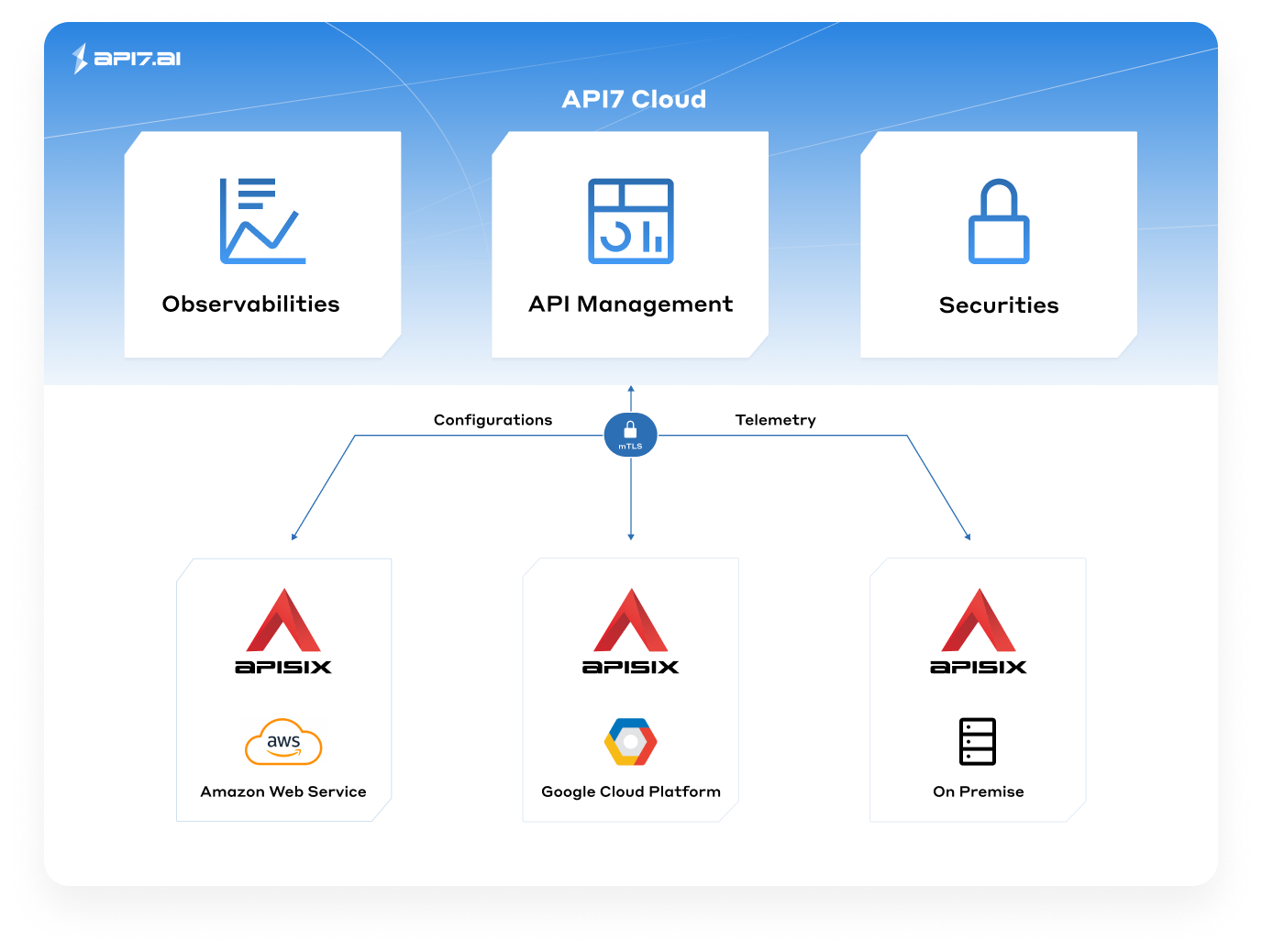
Api7 Enterprise Cloud Flexible Api Gateway Solutions Free Trial In the ecosystem, understanding how to implement robust authentication and authorization mechanisms—such as jwt and oauth—along with enforcing proper access controls, is crucial to protect your applications from potential threats. This guide explains, in simple terms, how to secure rest apis with jwt in core, including configuration, token generation, validation, and production best practices. Learn how to secure a api using json web tokens (jwts) with a step by step tutorial that walks through authentication configuration, token issuance, and endpoint protection. In this article, we will explore real world scenarios demonstrating how jwts work in a secure authentication system.
Comments are closed.