Identity Verification Security Without Compromising The User Experience
Overcoming Customer Identity Challenges Without Compromising The User How do you find the right balance between security, compliance, and user experience? discover the best strategies to optimize your customer journey while ensuring rigorous verification. Explore the importance of identity proofing in the digital age, balancing security measures with user experience. learn strategies to enhance trust and credibility in online interactions.

Improving User Experience With Identity Verification Entrust stands at the forefront of ai driven identity verification, offering solutions tailored to protect both your customers and your workforce without compromising user experience. Not all mfa is created equal duo delivers strong security without the hassle. it integrates easily, offers phishing resistant mfa in addition to options like biometrics and tokens, and includes user friendly identity verification. that means a smoother experience for users and less work for it support. Learn how hcltech built a custom idaas platform to address fragmented identity systems, enhance security, and improve user experience for a global finance and insurance corporation. To scale responsibly, bnpl providers must solve a strategic trilemma: how to fight increasingly sophisticated fraud, comply with tightening regulations like ccd2, and deliver a seamless user experience all at once. and at the center of this challenge is one common denominator: identity verification. fraud is now industrialized.

Enhancing User Experience In Identity Verification Processes Ppt Learn how hcltech built a custom idaas platform to address fragmented identity systems, enhance security, and improve user experience for a global finance and insurance corporation. To scale responsibly, bnpl providers must solve a strategic trilemma: how to fight increasingly sophisticated fraud, comply with tightening regulations like ccd2, and deliver a seamless user experience all at once. and at the center of this challenge is one common denominator: identity verification. fraud is now industrialized. Learn how to transform identity verification from a frustrating checkpoint into a seamless, inclusive experience that balances security with usability. By incorporating these key components—biometric authentication, automated id checkers, and comprehensive identity verification services—businesses can build a robust identity confirmation framework that addresses security concerns without compromising on user convenience. Explore the most common methods used to verify customer identity and compare their security, accuracy, and user experience. find the best solution for your business. From mapping your id verification user flow and designing trust first ui, to integrating providers and hardening architecture, the team knows how to balance security with humane ux.
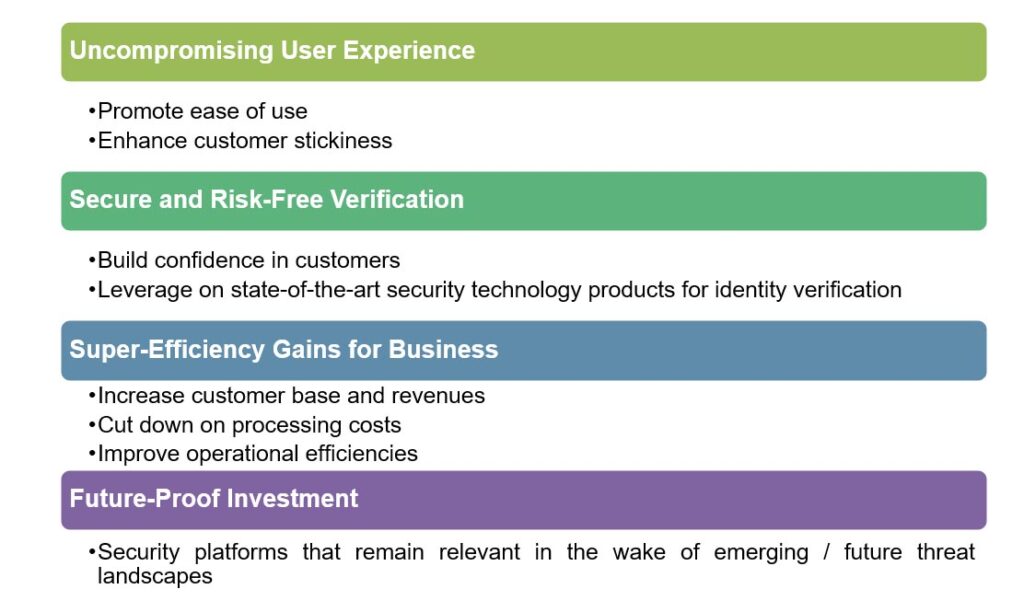
User Experience Driven Identity Verification Applications Will Power Learn how to transform identity verification from a frustrating checkpoint into a seamless, inclusive experience that balances security with usability. By incorporating these key components—biometric authentication, automated id checkers, and comprehensive identity verification services—businesses can build a robust identity confirmation framework that addresses security concerns without compromising on user convenience. Explore the most common methods used to verify customer identity and compare their security, accuracy, and user experience. find the best solution for your business. From mapping your id verification user flow and designing trust first ui, to integrating providers and hardening architecture, the team knows how to balance security with humane ux.

Ppt Identity Verification In E Commerce Fraud Protection Balancing Explore the most common methods used to verify customer identity and compare their security, accuracy, and user experience. find the best solution for your business. From mapping your id verification user flow and designing trust first ui, to integrating providers and hardening architecture, the team knows how to balance security with humane ux.

Identity Verification
Comments are closed.