Identity Is The New Attack Surface And The New Control Plane
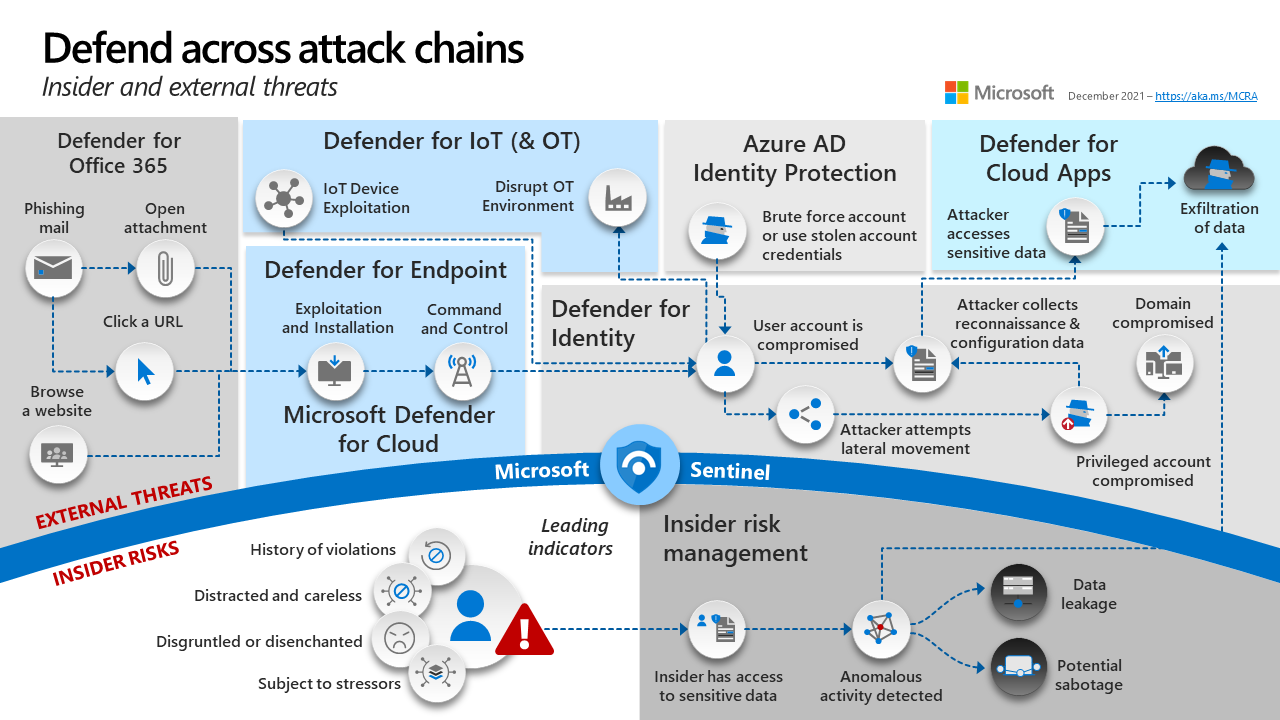
Identity Is The New Attack Surface And The New Control Plane Securing identity in this reality requires more than incremental improvements. it calls for a shift from fragmented controls to an integrated, end to end approach that treats identity as a shared control plane that is informed by a continuous, foundational security signal. Identity is now the primary attack vector because it is far easier to gain access through compromised credentials than through software vulnerabilities.

Way Too Vulnerable Uncovering The State Of The Identity Attack Surface After reading this, you’ll know how to architect identity controls that actually stop lateral movement, reduce blast radius from compromised accounts, and give you detection capability before an attacker reaches your data. Identity security fabric integrates iam, governance, and adaptive authentication into a continuous, unified identity centric control plane that spans hybrid environments, including both human and ai agents. Attackers are increasingly leveraging techniques that bypass existing controls, forcing enterprises to adopt more advanced security measures. 90% of organizations experienced an identity related breach in the past year, with 93% of these breaches being preventable through improved controls. Discover why identity is now your enterprise's primary attack surface, and how executives can lead a resilient identity defense strategy.

Limiting Your Identity Attack Surface Youattest Attackers are increasingly leveraging techniques that bypass existing controls, forcing enterprises to adopt more advanced security measures. 90% of organizations experienced an identity related breach in the past year, with 93% of these breaches being preventable through improved controls. Discover why identity is now your enterprise's primary attack surface, and how executives can lead a resilient identity defense strategy. This article dissects the attack surface of the modern identity control plane, providing security professionals with a technical blueprint to map, audit, and harden identity architectures across hybrid and ai driven environments. Whether human or non human, identities have become the new control plane of modern cybersecurity. in this blog, i break down five identity security lessons we can learn from the research. Across ai misuse, ransomware, fraud, supply chain compromise, and cloud outages, identity remains the dominant attack path. whether human or non human, identities have become the new control plane of modern cybersecurity. In this blog, we examine why identity threat detection and response (itdr) has become essential, how it addresses emerging attack methodologies, and why organizations must integrate identity response into their broader cybersecurity posture.
Comments are closed.