Iam Best Practices For Cloud Loves Cloud

Iam Best Practices Pdf Learn practical iam best practices for secure cloud computing covering federation, least privilege, mfa, and governance—with diagrams, steps, and tools. In this comprehensive guide, we’ll walk you through battle tested best practices that fortune 500 companies and security conscious startups use to protect their cloud environments.

Iam Best Practices For Cloud Loves Cloud By implementing robust iam strategies, you can significantly reduce the risk of data breaches, improve compliance, and streamline your cloud operations. this comprehensive overview explores the core concepts, best practices, and emerging trends in cloud iam. A practical guide to cloud iam best practices — from least privilege and ciem to cross cloud federation and automated policy reviews. Comprehensive guide to cloud iam best practices across aws, azure, and gcp. learn how to manage multi cloud iam permissions, implement cis benchmarks, and secure identities at scale. Identity and access management is the foundation of cloud security. properly configured iam policies prevent unauthorized access and limit the blast radius of security incidents. this guide covers essential iam best practices for aws, azure, and gcp.
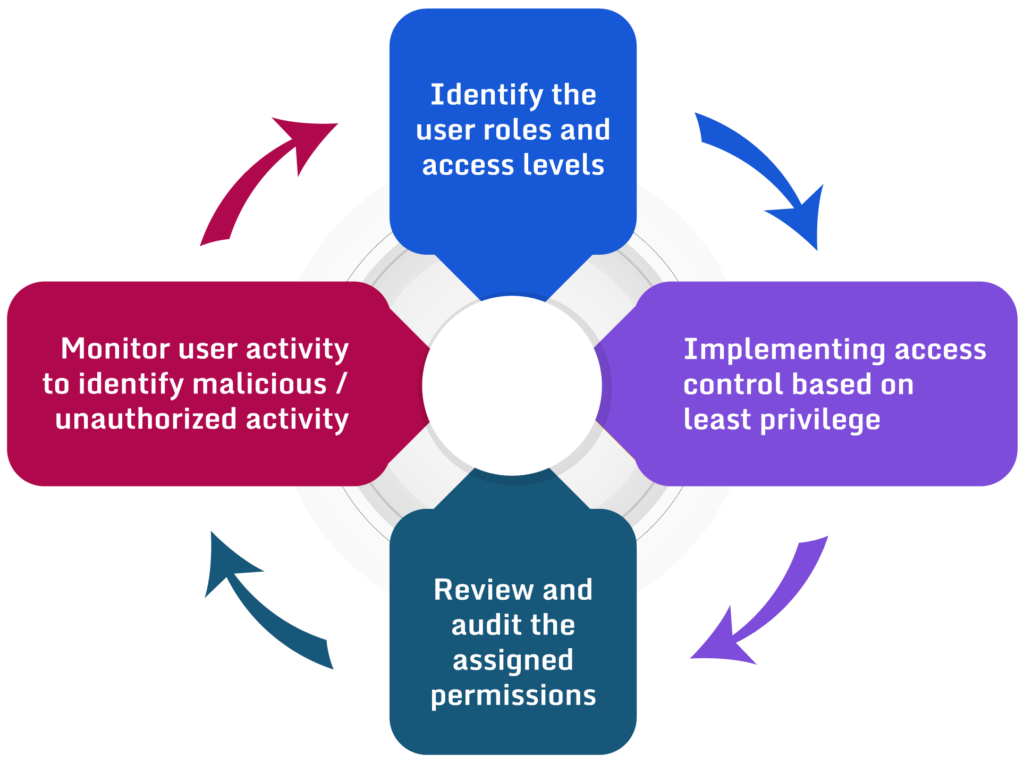
Guide To Iam Best Practices Paladin Cloud Comprehensive guide to cloud iam best practices across aws, azure, and gcp. learn how to manage multi cloud iam permissions, implement cis benchmarks, and secure identities at scale. Identity and access management is the foundation of cloud security. properly configured iam policies prevent unauthorized access and limit the blast radius of security incidents. this guide covers essential iam best practices for aws, azure, and gcp. Follow these best practices for using aws identity and access management (iam) to help secure your aws account and resources. Aws iam best practices: securing identity in amazon web services bottom line up front aws identity and access management (iam) is your first and most critical line of defense in cloud security. properly configured iam ensures that only authorized users can access your aws resources, and only for the actions they need to perform. Regular audits and penetration testing further strengthen the iam posture by identifying loopholes and ensuring alignment with best practices. such continuous oversight is vital for maintaining trust and integrity in cloud systems. This article explores cloud identity and access management best practices for 2026, covering modern risks, evolving identity models, and practical steps organisations should take to strengthen their cloud security posture.

Aws Iam Best Practices Cheat Sheet Cybr Follow these best practices for using aws identity and access management (iam) to help secure your aws account and resources. Aws iam best practices: securing identity in amazon web services bottom line up front aws identity and access management (iam) is your first and most critical line of defense in cloud security. properly configured iam ensures that only authorized users can access your aws resources, and only for the actions they need to perform. Regular audits and penetration testing further strengthen the iam posture by identifying loopholes and ensuring alignment with best practices. such continuous oversight is vital for maintaining trust and integrity in cloud systems. This article explores cloud identity and access management best practices for 2026, covering modern risks, evolving identity models, and practical steps organisations should take to strengthen their cloud security posture.

Aws Iam Best Practices Cheat Sheet Cybr Regular audits and penetration testing further strengthen the iam posture by identifying loopholes and ensuring alignment with best practices. such continuous oversight is vital for maintaining trust and integrity in cloud systems. This article explores cloud identity and access management best practices for 2026, covering modern risks, evolving identity models, and practical steps organisations should take to strengthen their cloud security posture.
Comments are closed.