Hw8 Solution Pdf Ip Address Computer Network
Computer Network Pdf Ip Address Computer Network Hw8 solution (1) free download as word doc (.doc), pdf file (.pdf), text file (.txt) or read online for free. the document contains answers to questions about computer communication networks. Assume that your laptop is configured with the ip address of a local dns server, as well as the ip address of a default gateway (a router through which traffic from your laptop will exit the local ip subnet).

Hw8 Solution Pdf Ip Address Computer Network In the ethernet fram containing the ip datagram, what are the source and destination ip and mac addresses? (b) suppose host e would like to send an ip datagram to host b, and assume that e’s arp cache does not contain b’s mac address. Com sci 118 spring 2018 computer network fundamentals ucla cs 118 hw hw8 sol.pdf at master · luckymicky ucla cs 118. Assign an ip address to each network interface of an end system and router. for subnet 1 use addresses from ip prefix 192.168.1.0 24; for subnet 2, from ip prefix 192.168.2.0 24; and for subnet 3, from ip prefix 192.168.3.0 24. Apply the subnet mask to the assigned ip address space to calculate the network address of the new possible subnets, the broadcast address for each possible subnet, and the range of usable ip addresses in each possible subnet.

Network Hardware Pdf Ip Address Computer Network Assign an ip address to each network interface of an end system and router. for subnet 1 use addresses from ip prefix 192.168.1.0 24; for subnet 2, from ip prefix 192.168.2.0 24; and for subnet 3, from ip prefix 192.168.3.0 24. Apply the subnet mask to the assigned ip address space to calculate the network address of the new possible subnets, the broadcast address for each possible subnet, and the range of usable ip addresses in each possible subnet. Solution: to break it into 8 subnets, we need to steal 3 bits from the host part and give it to the network part. these bits are in the 13th, 14th, and 15th position, i.e., the 5th, 6th, and 7th bits of the 2nd byte. The primary focus of this paper is to compare and analyze ipv4 and ipv6 networks, study their characteristics and header formats. the paper also attempts to outline the key deployment issues and security related challenges which are being faced and dealt with during the migration process. 1. based on the following routing table from a router, draw a diagram showing the approximate configuration of the network that the router is a part of. Ping is a utility for testing ip connectivity between hosts. ping sends out requests for responses from a specified host address. ping uses a layer 3 protocol that is a part on the tcp ip suite called internet control message protocol (icmp). ping uses an icmp echo request datagram.

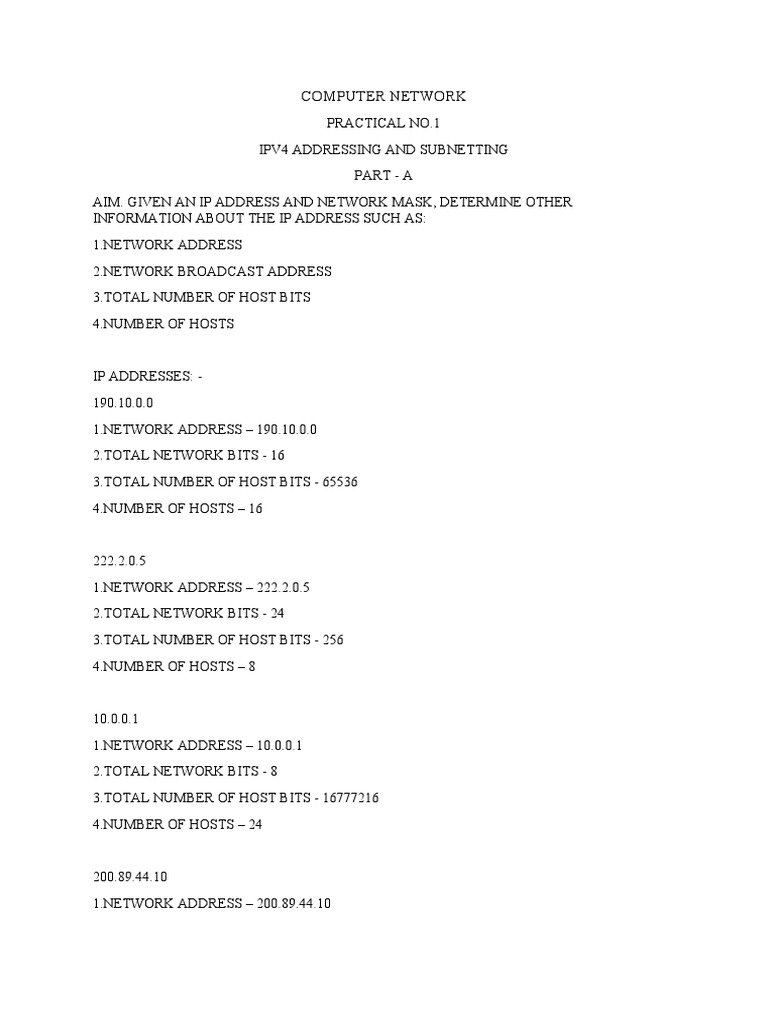
Lab01 Computer Networks Pdf Ip Address Computer Network Solution: to break it into 8 subnets, we need to steal 3 bits from the host part and give it to the network part. these bits are in the 13th, 14th, and 15th position, i.e., the 5th, 6th, and 7th bits of the 2nd byte. The primary focus of this paper is to compare and analyze ipv4 and ipv6 networks, study their characteristics and header formats. the paper also attempts to outline the key deployment issues and security related challenges which are being faced and dealt with during the migration process. 1. based on the following routing table from a router, draw a diagram showing the approximate configuration of the network that the router is a part of. Ping is a utility for testing ip connectivity between hosts. ping sends out requests for responses from a specified host address. ping uses a layer 3 protocol that is a part on the tcp ip suite called internet control message protocol (icmp). ping uses an icmp echo request datagram.

Network Season 6 Ip Addressing Pdf 1. based on the following routing table from a router, draw a diagram showing the approximate configuration of the network that the router is a part of. Ping is a utility for testing ip connectivity between hosts. ping sends out requests for responses from a specified host address. ping uses a layer 3 protocol that is a part on the tcp ip suite called internet control message protocol (icmp). ping uses an icmp echo request datagram.

Chapter 8 Computer Network Pdf Computer Network Network Topology
Comments are closed.