Html5 Cross Document Messaging Vulnerabilities
Html5 Cross Document Messaging Vulnerabilities Appcheck Never evaluate passed messages as code (e.g. via eval()) or insert it to a page dom (e.g. via innerhtml), as that would create a dom based xss vulnerability. for more information see dom based xss prevention cheat sheet. check the origin properly exactly to match the fqdn (s) you expect. In this article, we take a look at the security model that the web messaging api (a.k.a. “cross document messaging”) – is built on, why the security measures that it introduces are necessary, and some of the potential mis configurations that can undermine the api’s security model.
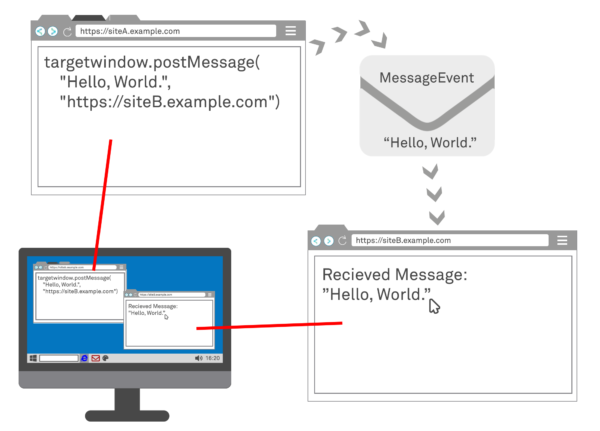
Html5 Cross Document Messaging Vulnerabilities Appcheck This section introduces a messaging system that allows documents to communicate with each other regardless of their source domain, in a way designed to not enable cross site scripting attacks. Testers should analyze the code and look for insecure methods, in particular where data is being evaluated via eval() or inserted into the dom via the innerhtml property, which may create dom based xss vulnerabilities. We do not need to analyze the entire html5 rfc and its related features; however, what we are going to explore in this recap section is the major features that are interesting from a security perspective. Web message vulnerabilities arise when a script sends attacker controllable data as a web message to another document within the browser.

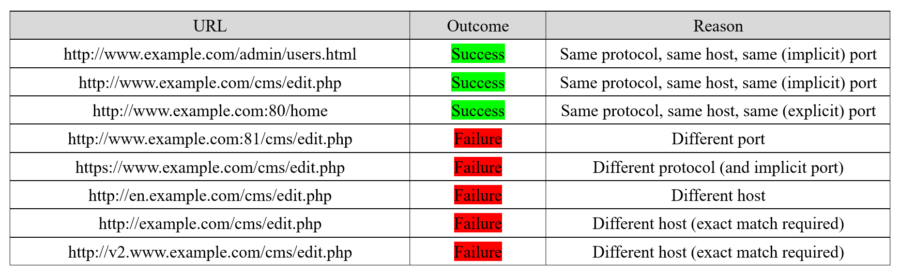
Html5 Cross Document Messaging Vulnerabilities Appcheck We do not need to analyze the entire html5 rfc and its related features; however, what we are going to explore in this recap section is the major features that are interesting from a security perspective. Web message vulnerabilities arise when a script sends attacker controllable data as a web message to another document within the browser. Abstract the program posts a cross document message with an overly permissive target origin. Unlock the power of html5 web messaging with our comprehensive guide. learn cross origin communication, security best practices, and real world applications. Javascript code should be analyzed to determine how web messaging is implemented. in particular, testers should be interested in how the website is restricting messages from untrusted domains, and how the data is handled even for trusted domains. Web messaging (also known as cross domain messaging) provides a means of messaging between documents from different origins in a way that is generally safer than the multiple hacks used in the past to accomplish this task.
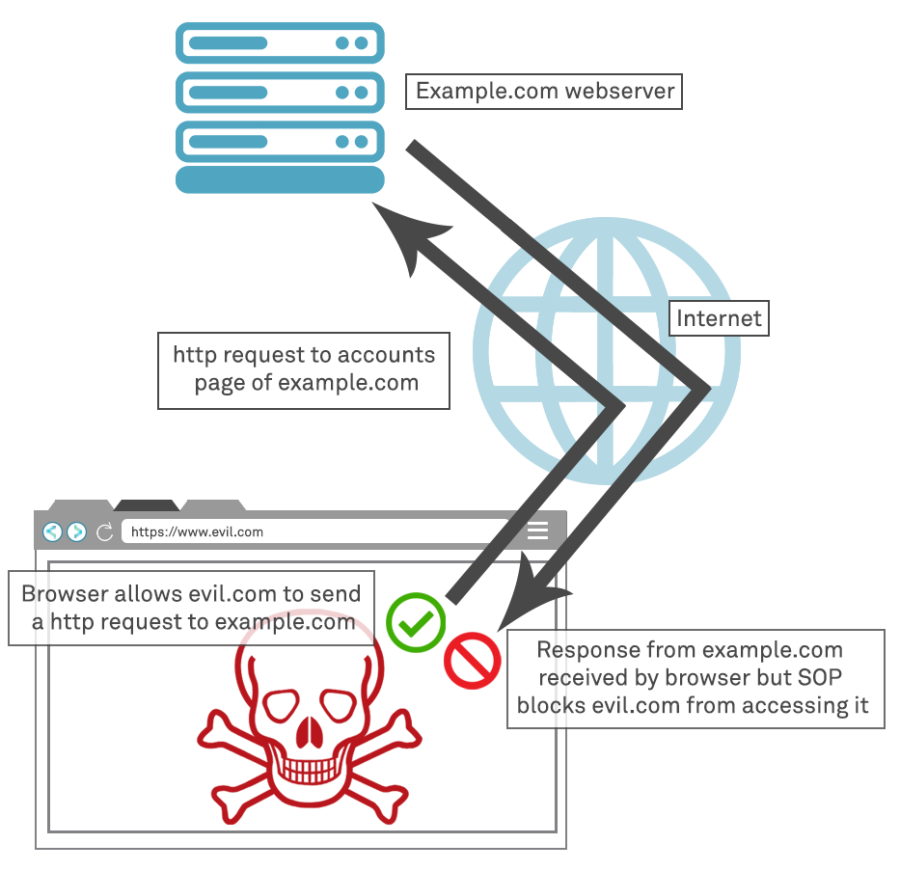
Html5 Cross Document Messaging Vulnerabilities Appcheck Abstract the program posts a cross document message with an overly permissive target origin. Unlock the power of html5 web messaging with our comprehensive guide. learn cross origin communication, security best practices, and real world applications. Javascript code should be analyzed to determine how web messaging is implemented. in particular, testers should be interested in how the website is restricting messages from untrusted domains, and how the data is handled even for trusted domains. Web messaging (also known as cross domain messaging) provides a means of messaging between documents from different origins in a way that is generally safer than the multiple hacks used in the past to accomplish this task.
Comments are closed.