How To Successfully Deploy Soar D3 Security

How To Successfully Deploy Soar D3 Security Learn how to deploy soar effectively by focusing on three key milestones in this whitepaper. How do you overcome the complexities of deploying soar in challenging environments? discover key strategies in our whitepaper, which details how to use our smart soar platform for strategic.
How To Successfully Deploy Soar D3 Security With d3 security’s smart soar, teams have a single pane of glass for managing automated incident response across their security stack. the technology transforms thousands of low fidelity alerts into few high fidelity, high confidence incidents, giving responders more time to investigate real threats. The zscaler and d3 security deployment guide provides instructions on how to configure zscaler api to work with the d3 security's security orchestration, automation and response (soar) platform. If you haven’t used soar before, you probably have a lot of questions about deploying it in your organization. our new guide offers winning strategies for a streamlined soar implementation. At d3, we are committed to ensuring that your deployment is smooth, efficient, and cost effective. this document provides insights into our existing azure deployment regions and the potential implications of expanding to other regions.

Soar Security Orchestration Automation And Response Elastic If you haven’t used soar before, you probably have a lot of questions about deploying it in your organization. our new guide offers winning strategies for a streamlined soar implementation. At d3, we are committed to ensuring that your deployment is smooth, efficient, and cost effective. this document provides insights into our existing azure deployment regions and the potential implications of expanding to other regions. Rather than going through the playbook step by step, the demonstration showcases the investigation tab, presenting analysts with a consolidated and organized summary of the entire attack scenario . With expert guidance, a strong focus on core functionalities, and rigorous testing, your security operations can be up and running on a new soar system—or other major tool in your soc—with minimal disruption. A detailed step by step guide to creating and automating playbooks in d3 from versprite's threat intelligence analyst. Using d3’s advanced capabilities, soc operators around the world have expanded the speed and scale of their security operations, while strengthening their ability to identify suspicious behaviors, conduct eficient investigations, and remediate critical threats.

Supercharge Microsoft Security Tools With D3 Security Smart Soar邃 D3 Rather than going through the playbook step by step, the demonstration showcases the investigation tab, presenting analysts with a consolidated and organized summary of the entire attack scenario . With expert guidance, a strong focus on core functionalities, and rigorous testing, your security operations can be up and running on a new soar system—or other major tool in your soc—with minimal disruption. A detailed step by step guide to creating and automating playbooks in d3 from versprite's threat intelligence analyst. Using d3’s advanced capabilities, soc operators around the world have expanded the speed and scale of their security operations, while strengthening their ability to identify suspicious behaviors, conduct eficient investigations, and remediate critical threats.
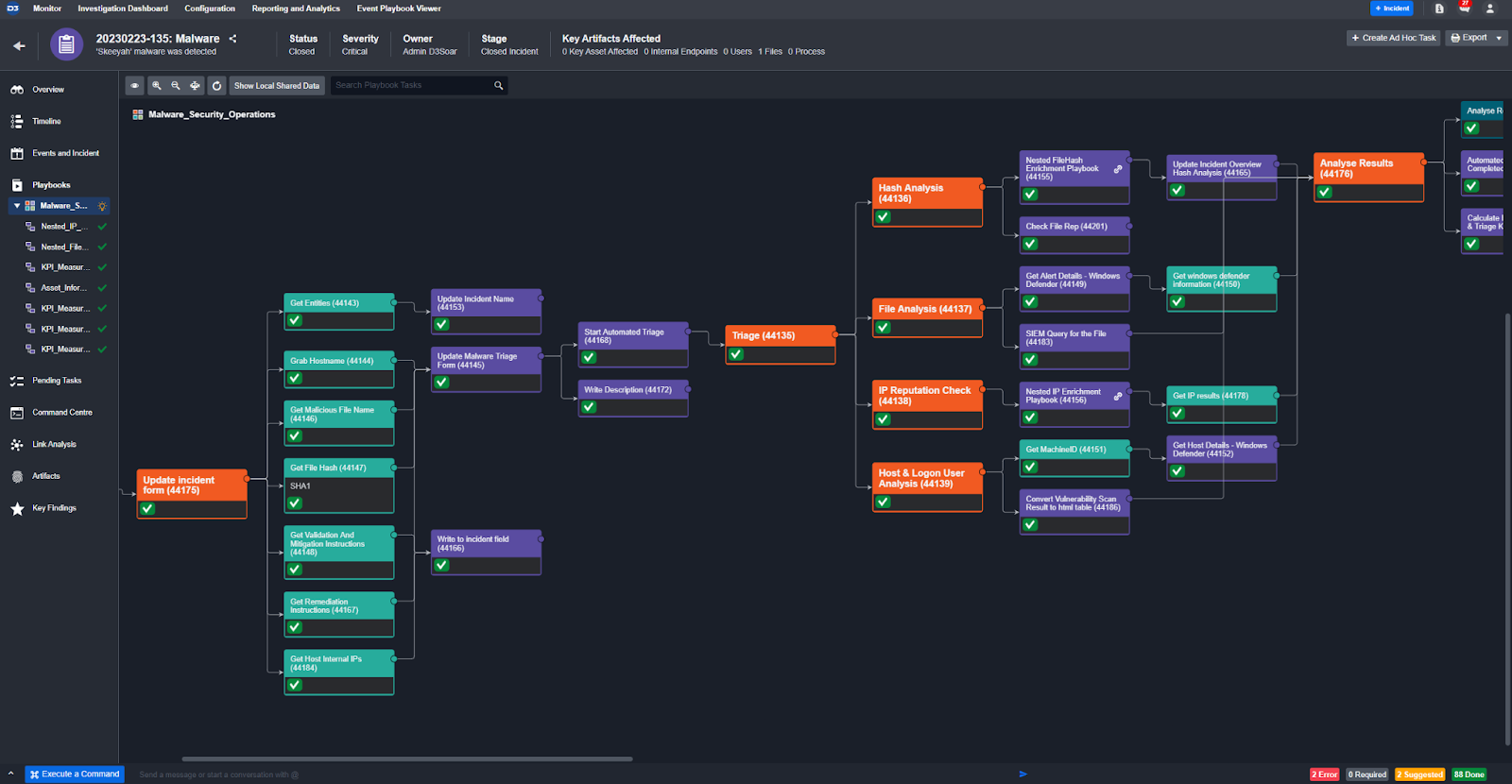
Smart Soar Gives You The Best Cybersecurity Playbooks D3 Security A detailed step by step guide to creating and automating playbooks in d3 from versprite's threat intelligence analyst. Using d3’s advanced capabilities, soc operators around the world have expanded the speed and scale of their security operations, while strengthening their ability to identify suspicious behaviors, conduct eficient investigations, and remediate critical threats.

Legacy Soar Migration D3
Comments are closed.