How To Secure Your Portainer Setup With Security Controls

Get Portainer Set Up Learn how to harden your portainer installation with essential security controls including https, strong authentication, network restrictions, and access policies. In this video, you're going to learn about some very interesting security controls that portainer provides.

Get Portainer Setup This article describes the recommended steps when accessing portainer for the first time, including creating the initial administrator account and securing access to the instance. This guide covers the essential security measures to protect your portainer instance against unauthorized access, privilege escalation, and data exposure. apply these measures before exposing portainer to any network beyond localhost. Therefore it is now possible to use a default portainer installation in an environment with potentially untrusted users (and potentially untrusted images) without fully compromising the security of the host. Security considerations and best practices for running portainer mcp.
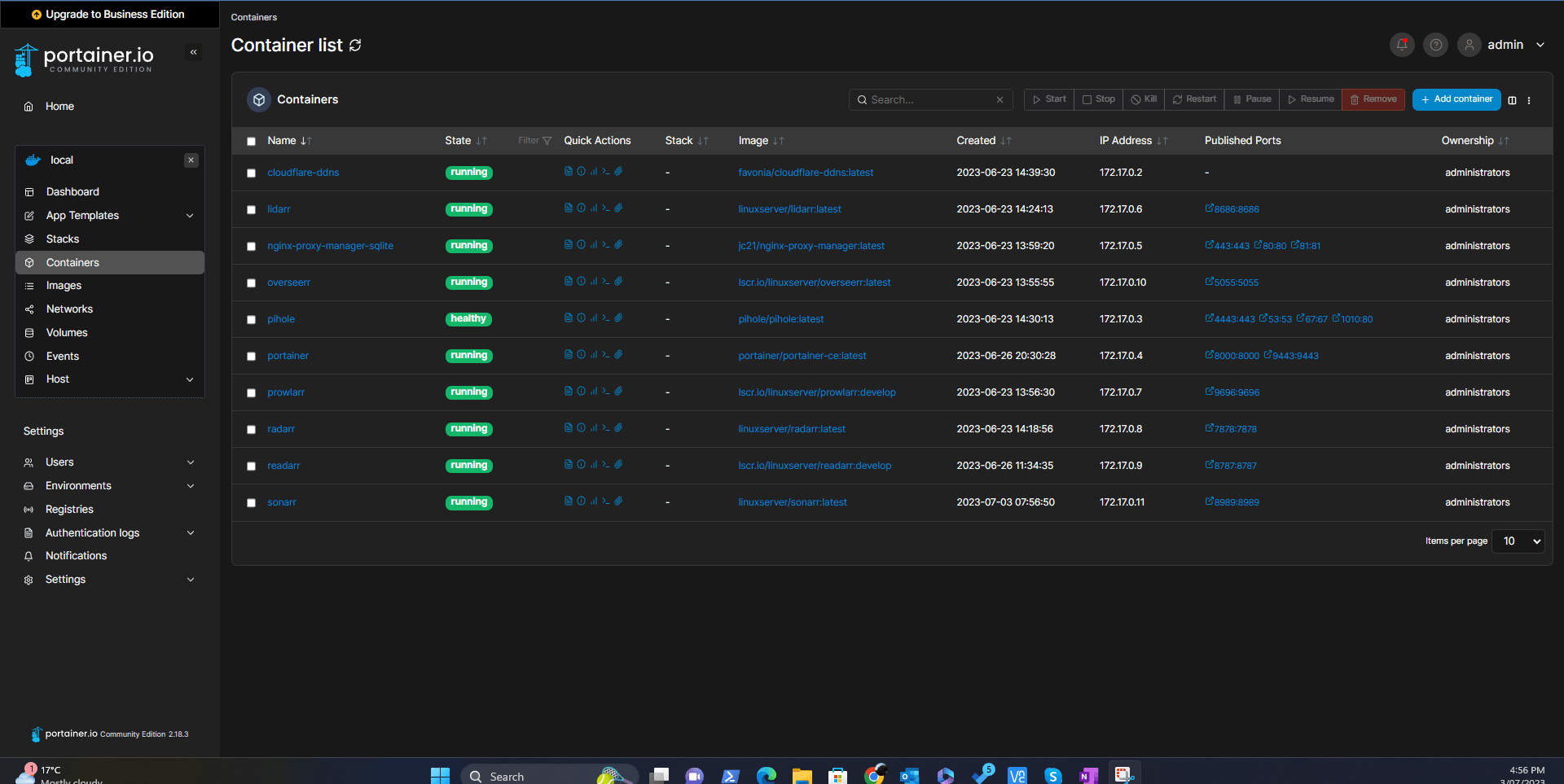
Portainer Setup Geldenhuys Tech Therefore it is now possible to use a default portainer installation in an environment with potentially untrusted users (and potentially untrusted images) without fully compromising the security of the host. Security considerations and best practices for running portainer mcp. Portainer has native capability to discourage the use of public repositories, the configure opa gatekeeper policies, and to correctly secure the platform with rbac, quotas, and namespace. If you run portainer, and you seek a modern, flexible recipe for how to make it secure while also providing flexible access to your authorized users, this article is for you. Fortunately, portainer makes it easy to enable the forcing of https and upload your ssl certificates. i’ll show you how this is done. note: when you force https in portainer, http access will. Portainer can be easily tuned using cli flags. portainer allows you to specify an encrypted password from the command line for the admin account. you need to generate the encrypted password first. you can generate an encrypted password with the following command:.

Portainer Setup Geldenhuys Tech Portainer has native capability to discourage the use of public repositories, the configure opa gatekeeper policies, and to correctly secure the platform with rbac, quotas, and namespace. If you run portainer, and you seek a modern, flexible recipe for how to make it secure while also providing flexible access to your authorized users, this article is for you. Fortunately, portainer makes it easy to enable the forcing of https and upload your ssl certificates. i’ll show you how this is done. note: when you force https in portainer, http access will. Portainer can be easily tuned using cli flags. portainer allows you to specify an encrypted password from the command line for the admin account. you need to generate the encrypted password first. you can generate an encrypted password with the following command:.
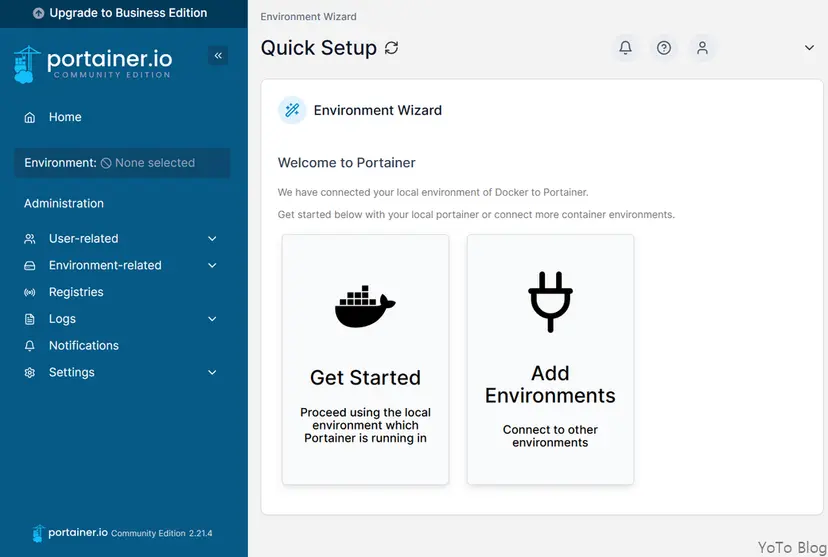
Launching Portainer On Docker Fortunately, portainer makes it easy to enable the forcing of https and upload your ssl certificates. i’ll show you how this is done. note: when you force https in portainer, http access will. Portainer can be easily tuned using cli flags. portainer allows you to specify an encrypted password from the command line for the admin account. you need to generate the encrypted password first. you can generate an encrypted password with the following command:.
Comments are closed.