How To Reduce Vulnerabilities Malware Attacks On Android Devices
How To Reduce Vulnerabilities Malware Attacks On Android Devices Every android release brings performance and security enhancements, and with android 16, you can take simple, significant steps to strengthen your app’s defenses. check out our video or continue reading to learn more about our enhanced protections for accessibility apis. Taking cyber security seriously will help reduce your risk of falling victim to android malware. here are some malware protection tips to help keep your android device safe:.

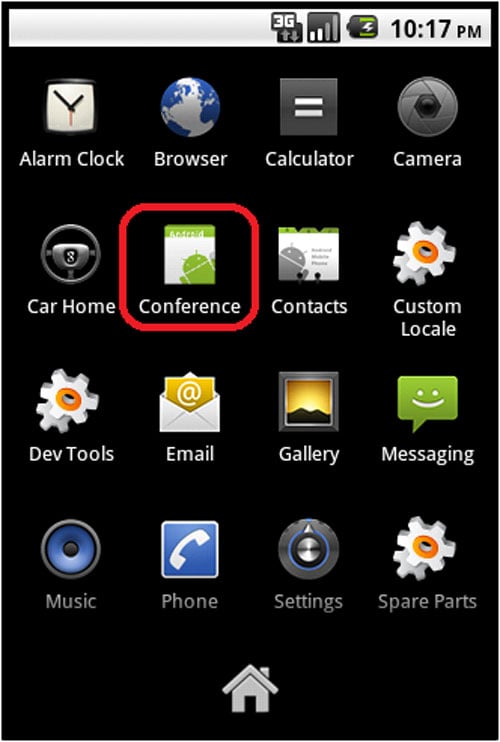
How To Reduce Vulnerabilities Malware Attacks On Android Devices This paper investigates the vulnerabilities inherent in the android operating system architecture and examines how malware developers exploit these weaknesses to execute a variety of. If an android phone shows signs of malware, it's crucial to remove the malicious software and protect the endpoint from future threats. mobile threat detection and mdm tools can help prevent and eliminate threats, and there are a few other steps that admins can take if malware persists. This guide walks you through practical steps to safeguard your device from malware and vulnerabilities, all while keeping things light and easy to follow. because protecting yourself from malware and vulnerabilities doesn’t have to feel like a chore — it can actually be empowering. Android devices’ vulnerabilities are giving enough reasons to the cyber thieves for creating new varieties of malware, some of which posses the capability to gain root access on mobile devices and then install additional malware packages.

Android Vulnerabilities And Attacks Pdf This guide walks you through practical steps to safeguard your device from malware and vulnerabilities, all while keeping things light and easy to follow. because protecting yourself from malware and vulnerabilities doesn’t have to feel like a chore — it can actually be empowering. Android devices’ vulnerabilities are giving enough reasons to the cyber thieves for creating new varieties of malware, some of which posses the capability to gain root access on mobile devices and then install additional malware packages. Now that you know the risks, here are 10 practical, smart security moves to prevent an android phone hack. follow these steps, and you’ll be miles ahead of the hackers. This paper explores the factors contributing to the growing vulnerabilities in android devices, including its open source nature, ecosystem fragmentation, delayed security updates, and the proliferation of unregulated third party app stores. This article provides overview of life cycle of common vulnerabilities and exposure (cves) and explains the process of security updates from google highlighting collaborative efforts of various. Cybercriminals are constantly refining their methods, which means you need to take a proactive approach to android security. dive into this comprehensive guide to common android threats and practical steps to transform your smartphone into a digital fortress. here are some of the top security threats currently affecting android users.
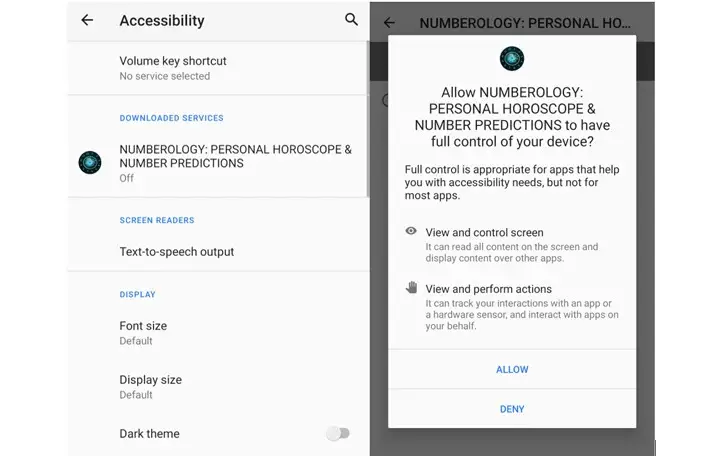
330k Android Devices Compromised Through New Malware Now that you know the risks, here are 10 practical, smart security moves to prevent an android phone hack. follow these steps, and you’ll be miles ahead of the hackers. This paper explores the factors contributing to the growing vulnerabilities in android devices, including its open source nature, ecosystem fragmentation, delayed security updates, and the proliferation of unregulated third party app stores. This article provides overview of life cycle of common vulnerabilities and exposure (cves) and explains the process of security updates from google highlighting collaborative efforts of various. Cybercriminals are constantly refining their methods, which means you need to take a proactive approach to android security. dive into this comprehensive guide to common android threats and practical steps to transform your smartphone into a digital fortress. here are some of the top security threats currently affecting android users.
Android Phones Now Subject To Targeted Malware Attacks Hothardware This article provides overview of life cycle of common vulnerabilities and exposure (cves) and explains the process of security updates from google highlighting collaborative efforts of various. Cybercriminals are constantly refining their methods, which means you need to take a proactive approach to android security. dive into this comprehensive guide to common android threats and practical steps to transform your smartphone into a digital fortress. here are some of the top security threats currently affecting android users.
Comments are closed.