How To Manage Software Security Vulnerabilities

Manage Vulnerabilities With Darwin Attack Evolve Security Learn what vulnerability management is, what steps are involved in the process, and how you can implement a robust vulnerability management program that leverages automation. Explore the top 10 vulnerability management best practices to protect systems, apply proactive methods, and secure your it infrastructure.
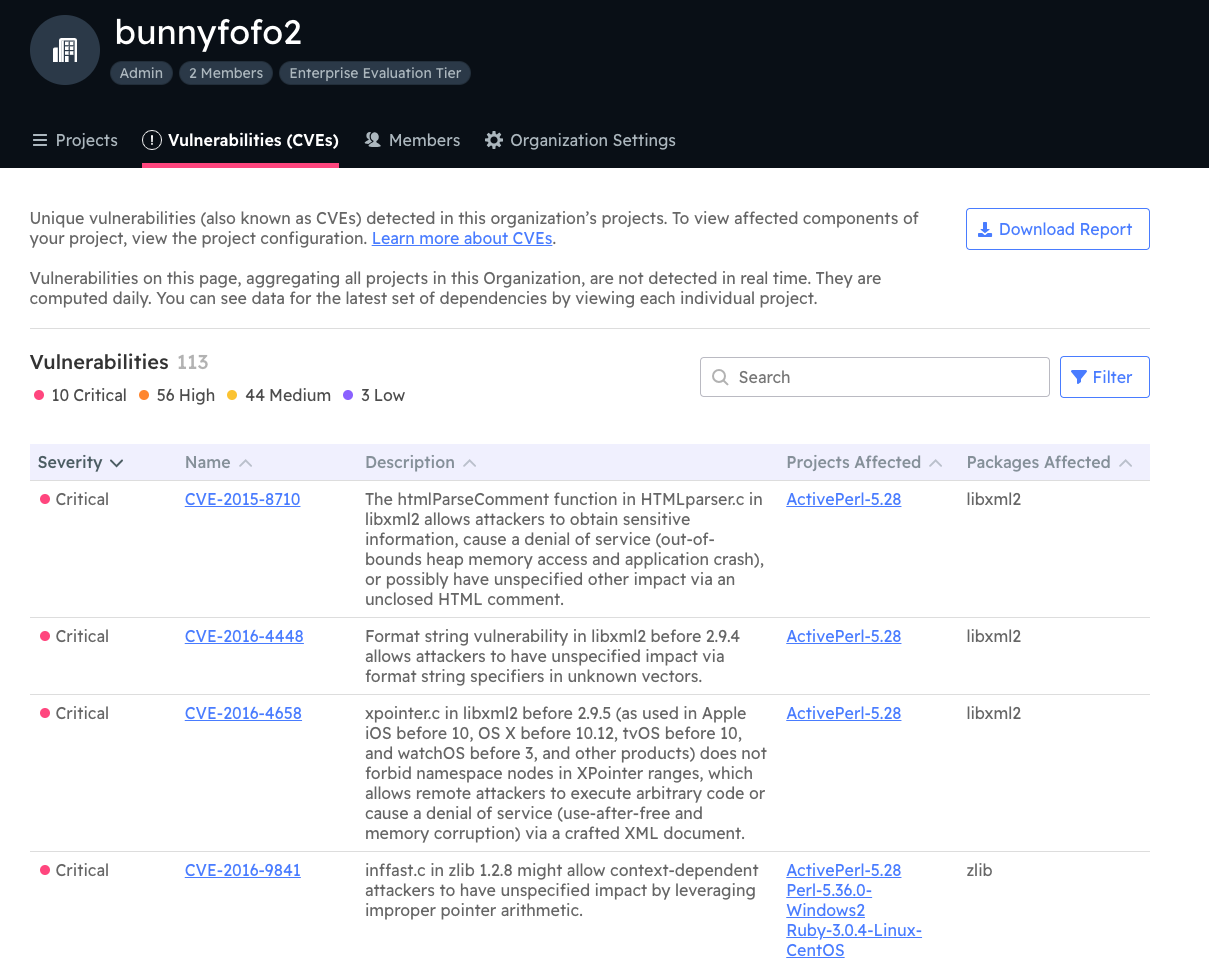
How To Manage Software Security Vulnerabilities Learn top vulnerability management, scanning, and remediation best practices to protect your systems and reduce security risks effectively. read today!. This article will cover everything you need to know about vulnerability management in cybersecurity: the definition and benefits of vulnerability management, steps, and best practices for vulnerability management, and more. The guide provides in depth coverage of the full vulnerability management lifecycle including the preparation phase, the vulnerability identification scanning phase, the reporting phase, and remediation phase. Learn how to effectively manage and mitigate vulnerabilities in software by integrating security throughout the development process and utilizing automated security testing and continuous monitoring.

How To Manage Software Security Vulnerabilities The guide provides in depth coverage of the full vulnerability management lifecycle including the preparation phase, the vulnerability identification scanning phase, the reporting phase, and remediation phase. Learn how to effectively manage and mitigate vulnerabilities in software by integrating security throughout the development process and utilizing automated security testing and continuous monitoring. Learn the 7 stages of the vulnerability management lifecycle, with a proven vulnerability management process flow chart, tools, and best practices. Addressing security vulnerabilities in software development is crucial for preventing exploits and maintaining compliance with security standards. this framework outlines best practices for secure coding, automated vulnerability scanning, patch management, and penetration testing. Vulnerability management in software development refers to the systematic, proactive process of identifying, assessing, prioritizing, and mitigating security vulnerabilities throughout the software development lifecycle. There are 8 vulnerability management best practices including: conduct asset discovery and inventory. classify assets and assign tasks. run frequent automated vulnerability scanning. prioritize vulnerabilities and take corrective actions. establish a comprehensive vulnerability management strategy. use automated tools and leverage automation.
Altis Infonet Pvt Ltd Preventing Software Vulnerabilities A Learn the 7 stages of the vulnerability management lifecycle, with a proven vulnerability management process flow chart, tools, and best practices. Addressing security vulnerabilities in software development is crucial for preventing exploits and maintaining compliance with security standards. this framework outlines best practices for secure coding, automated vulnerability scanning, patch management, and penetration testing. Vulnerability management in software development refers to the systematic, proactive process of identifying, assessing, prioritizing, and mitigating security vulnerabilities throughout the software development lifecycle. There are 8 vulnerability management best practices including: conduct asset discovery and inventory. classify assets and assign tasks. run frequent automated vulnerability scanning. prioritize vulnerabilities and take corrective actions. establish a comprehensive vulnerability management strategy. use automated tools and leverage automation.
Comments are closed.