How To Hide Api Key On Github Secure Your Dotenv Files Fast

How To Use Github Actions Secrets To Hide Sensitive Data This article will guide you on how to hide api keys properly without excluding the entire file and removing them from the commit history if sensitive data has been already pushed. How to do so depends on the language and tools you use (for node.js, php, etc.). you can exclude .env file from commits by adding .env to the .gitignore. you can also upload an example configuration .env.example with dummy data or blanks to show the schema your application requires.

Github Security 101 Best Practices For Securing Your Repository One git push with a hardcoded api key can compromise your infrastructure. this guide covers .env file setup, language specific examples, automated secret scanning with git secrets and trufflehog, and how to deliver secrets to production safely with deployhq. Bots scrape github constantly for leaked keys, and a committed secret can be exploited within minutes. the fix is simple: use environment variables via .env files and never let secrets touch your codebase. Learning how to hide an api key in github protects your credentials, your users, and your budget. this guide covers four proven methods for keeping sensitive data out of your repository. In this article, i will explain, with simple examples for beginners, what the dotenv library is, why it is used, and how to use it. 📌 what is dotenv? dotenv takes its name from the .env.
Github Security 101 Best Practices For Securing Your Repository Learning how to hide an api key in github protects your credentials, your users, and your budget. this guide covers four proven methods for keeping sensitive data out of your repository. In this article, i will explain, with simple examples for beginners, what the dotenv library is, why it is used, and how to use it. 📌 what is dotenv? dotenv takes its name from the .env. In this guide, we’ll walk through how to use the `dotenv` gem to manage environment variables in rails and, most importantly, how to ensure your `.env` file is never uploaded to github. If you're deploying your app (e.g., to aws, heroku, or any cloud service), use their secret management tools to store your keys securely. this way, the api key is never exposed in your codebase, and you can still keep your repository public. Learn how to use python dotenv and .gitignore to hide api keys and protect your data pipelines from hackers. Go to the directory’s root and create .gitignore file. add .env (dot env) to .gitignore to hide from github. note: use one .env file per project, you can store multiple api keys, passwords and other sensitive info. best practice to store .env on same root directory as .gitignore.
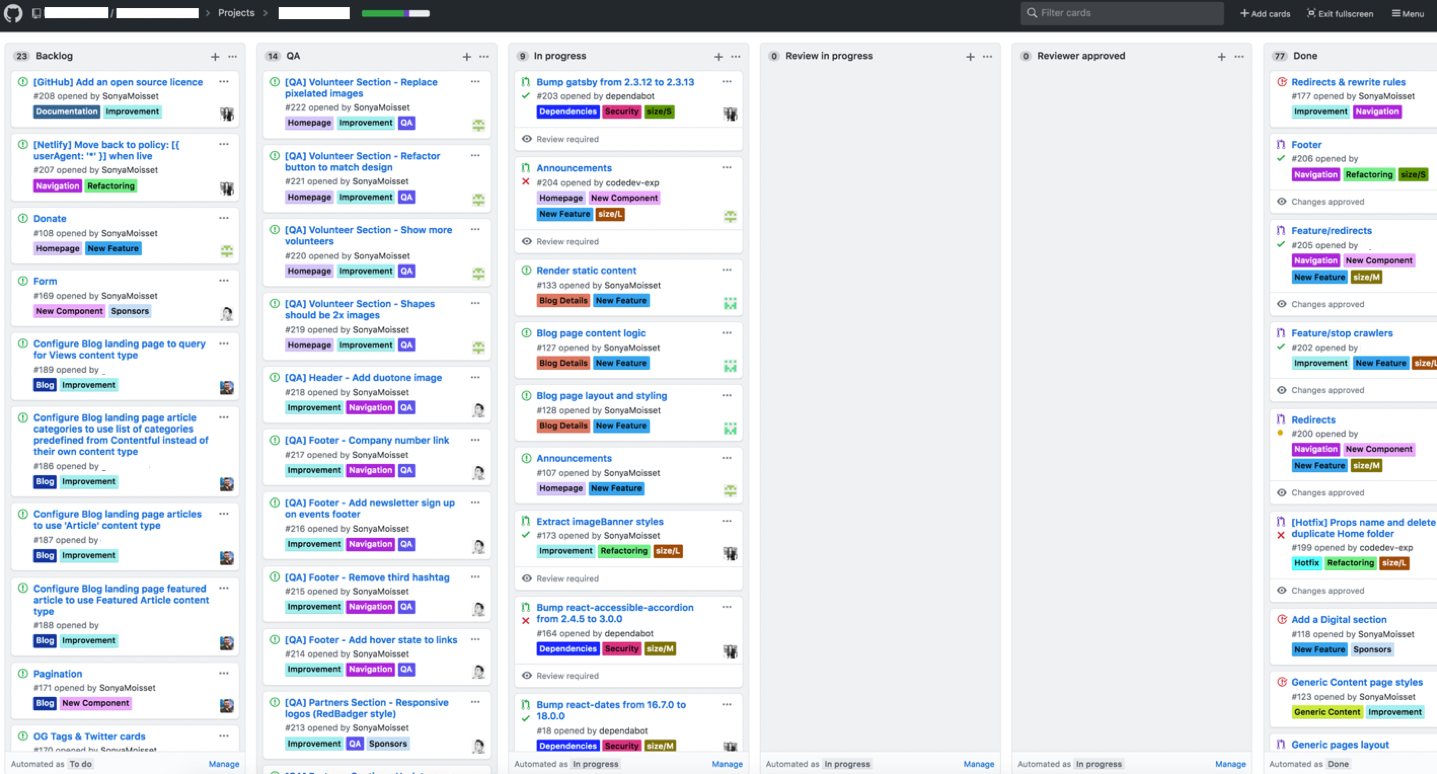
Github Security 101 Best Practices For Securing Your Repository In this guide, we’ll walk through how to use the `dotenv` gem to manage environment variables in rails and, most importantly, how to ensure your `.env` file is never uploaded to github. If you're deploying your app (e.g., to aws, heroku, or any cloud service), use their secret management tools to store your keys securely. this way, the api key is never exposed in your codebase, and you can still keep your repository public. Learn how to use python dotenv and .gitignore to hide api keys and protect your data pipelines from hackers. Go to the directory’s root and create .gitignore file. add .env (dot env) to .gitignore to hide from github. note: use one .env file per project, you can store multiple api keys, passwords and other sensitive info. best practice to store .env on same root directory as .gitignore.
Comments are closed.