How To Hack Smart Contracts Solidity Vulnerability Integer Overflow Underflow Explained
Common Vulnerabilities In Solidity Arithmetic Overflow And Underflow Integer overflow and underflow describe situations where arithmetic operations produce values outside the representable range of the operand type. in solidity 0.8 , arithmetic is checked by default and reverts on overflow underflow. In this article, we’ll explore integer overflow and underflow in detail, demonstrate how they can be exploited in smart contracts, and walk through a working example using ethereum remix.

Hacking Solidity Smart Contracts Cobalt An overflow error attack on a smart contract occurs when more value is provided than the maximum value. when this happens, it circles back to zero, and this feature can be exploited by repeatedly invoking the feature that increases the value. We'll briefly describe the concept of arithmetic underflow and arithmetic overflow in solidity and explain how they can lead to real world bugs and exploits. we’ll also highlight some tips for mitigating underflow and overflow issues in smart contracts. Integer overflow and underflow fall into the latter category, capable of causing catastrophic losses in smart contracts if left unchecked. these vulnerabilities exploit the inherent limitations of fixed width integer types in solidity, leading to unintended behavior. Among the most common and damaging bugs in smart contracts are arithmetic errors—integer overflows and underflows. this article unpacks those risks, shows how they are exploited, and outlines robust defenses that go beyond simple type safety.
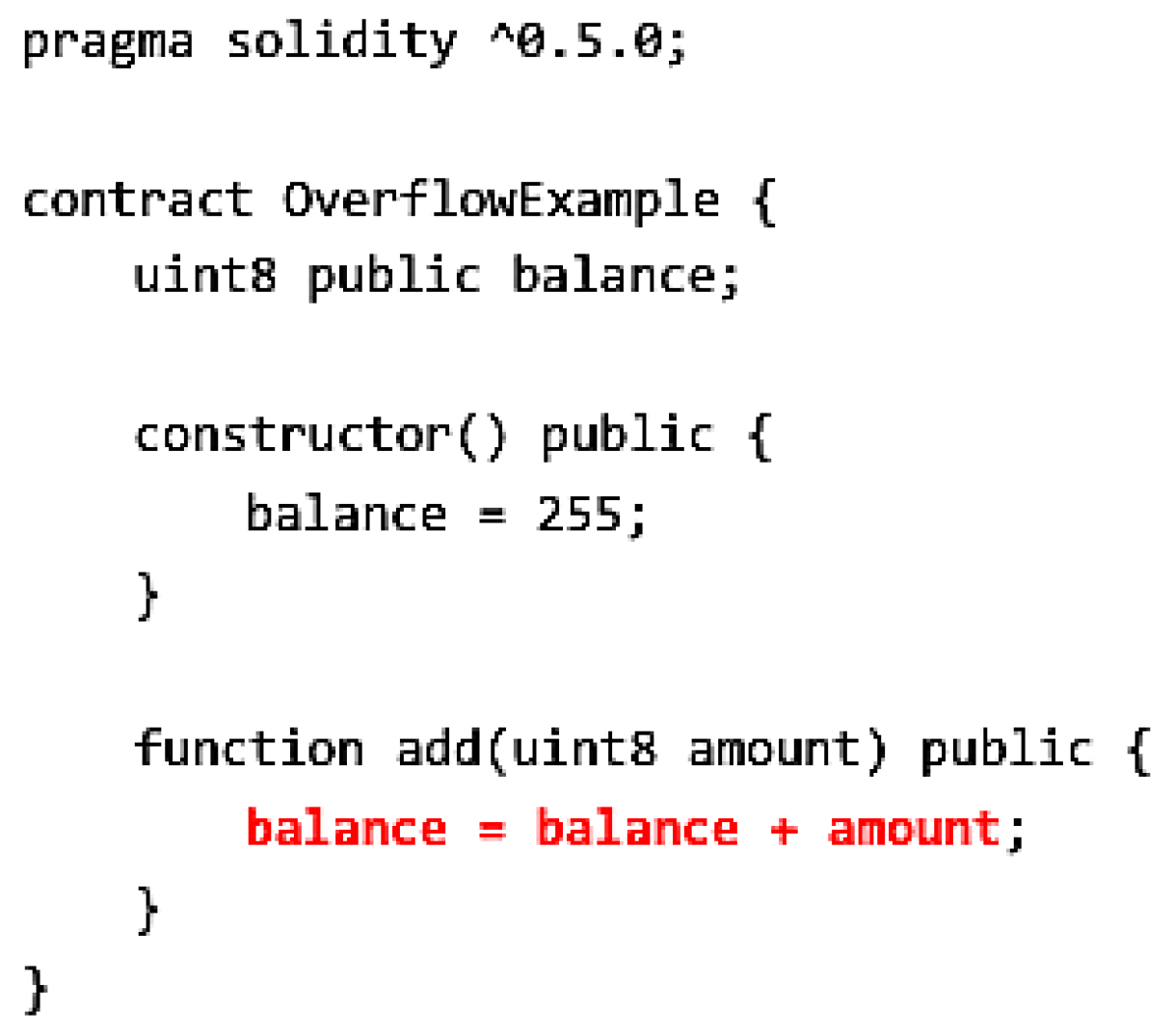
A Hybrid Semantic And Multi Attention Mechanism Approach For Detecting Integer overflow and underflow fall into the latter category, capable of causing catastrophic losses in smart contracts if left unchecked. these vulnerabilities exploit the inherent limitations of fixed width integer types in solidity, leading to unintended behavior. Among the most common and damaging bugs in smart contracts are arithmetic errors—integer overflows and underflows. this article unpacks those risks, shows how they are exploited, and outlines robust defenses that go beyond simple type safety. This article dives deep into integer overflow and underflow, explains why they occur, illustrates them with practical examples, and presents effective solutions. Arithmetic overflows and underflows in solidity: how math bugs become exploits and how to prevent them with safe invariants and checks. Integer overflow and underflow can lead to significant vulnerabilities in smart contracts, potentially allowing attackers to manipulate contract states maliciously. Remediating overflow and underflow vulnerabilities in smart contracts involves implementing checks and balances to ensure that arithmetic operations do not exceed the data type’s limits.
Comments are closed.