How To Hack Android Macos Ios And Linux Through A Bluetooth

How To Hack Android Macos Ios And Linux Through A Bluetooth Over the past six weeks, google, microsoft, linux (bluez), and apple have rolled out fixes for a bluetooth security flaw that, among other things, tricks the bluetooth host machine into. A major bluetooth security flaw, cve 2023 45866 could allow threat actors to take control of android, linux, macos, and ios devices.

How To Hack Android Macos Ios And Linux Through A Bluetooth A serious security risk has been identified in a key bluetooth vulnerability that affects many widely used operating systems, including android, ios, macos, ipados, and linux. On ios and macos, the vulnerability arises when bluetooth is enabled and a magic keyboard is paired with the device. once paired, attackers operating from a linux computer with a standard bluetooth adapter can inject keystrokes into the target device. Attackers can exploit a critical bluetooth security vulnerability that's been lurking largely unnoticed for years on macos, ios, android, and linux device platforms. A researcher has explained how android, macos, ios, ipados, and linux devices can be remotely hacked by exploiting a vulnerability in the bluetooth protocol.
Best Bluetooth Hacking App Guidelists Attackers can exploit a critical bluetooth security vulnerability that's been lurking largely unnoticed for years on macos, ios, android, and linux device platforms. A researcher has explained how android, macos, ios, ipados, and linux devices can be remotely hacked by exploiting a vulnerability in the bluetooth protocol. Pairing involves connecting and exchanging cryptographic data to secure the connection. for the user this usually involves selecting the device from a list and pressing connect. now that we understand bluetooth hid better, let’s discuss how these vulnerabilities can happen and why. A critical vulnerability in bluetooth allows attackers to take control of android, linux, macos, and ios devices, including devices in lockdown mode. this vulnerability is tracked as cve 2023 45866 and disclosed by security researcher marc newlin. Attackers can exploit a critical bluetooth security vulnerability that's been lurking largely unnoticed for years on macos, ios, android, and linux device platforms. Cerberus blue is a cutting edge, open source tool designed for bluetooth security research and penetration testing. it offers a robust suite of attacks targeting bluetooth classic and ble devices across android, ios, windows, and linux platforms.
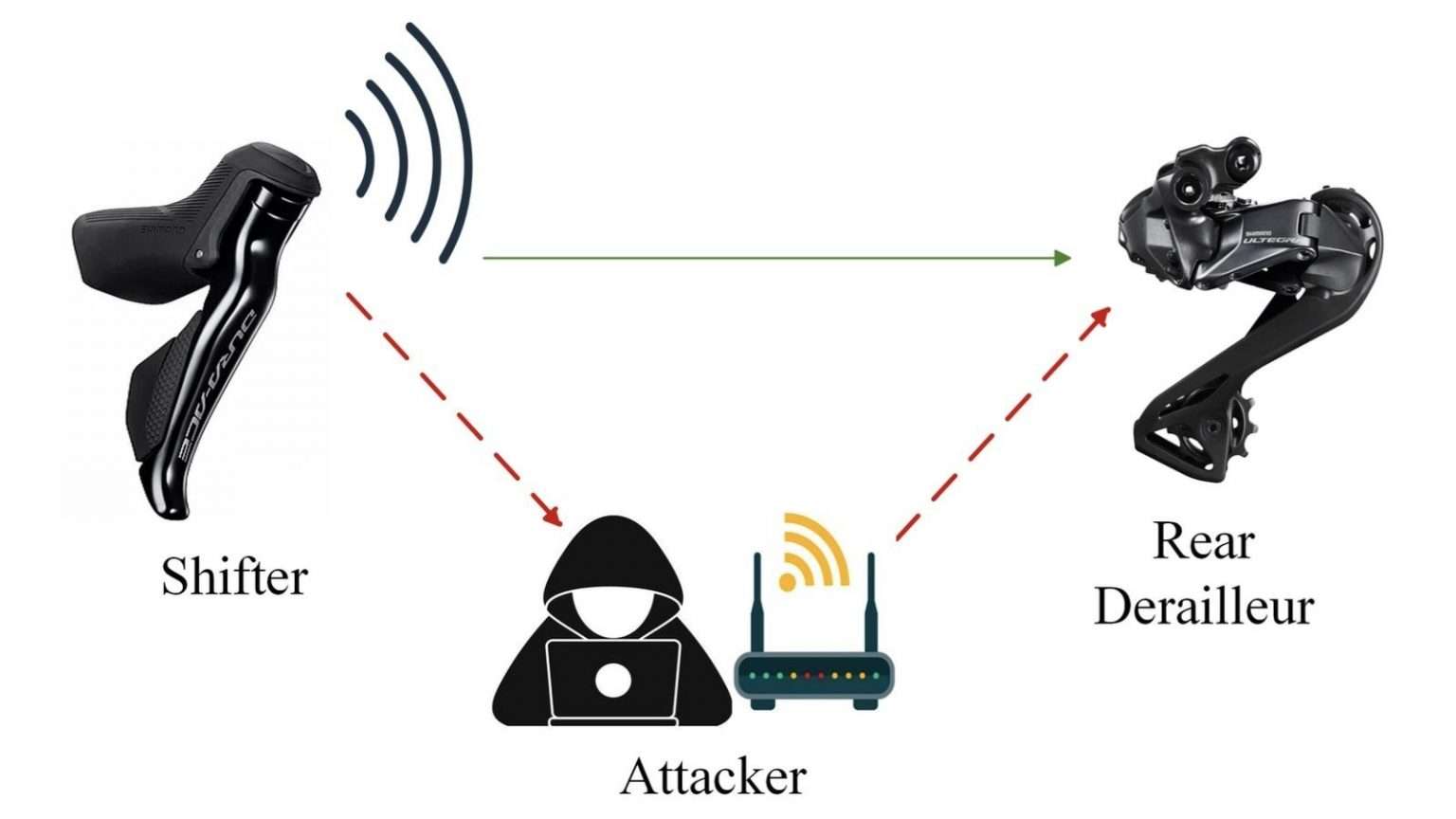
Bluetooth Hacking Explained Updated 2025 Pairing involves connecting and exchanging cryptographic data to secure the connection. for the user this usually involves selecting the device from a list and pressing connect. now that we understand bluetooth hid better, let’s discuss how these vulnerabilities can happen and why. A critical vulnerability in bluetooth allows attackers to take control of android, linux, macos, and ios devices, including devices in lockdown mode. this vulnerability is tracked as cve 2023 45866 and disclosed by security researcher marc newlin. Attackers can exploit a critical bluetooth security vulnerability that's been lurking largely unnoticed for years on macos, ios, android, and linux device platforms. Cerberus blue is a cutting edge, open source tool designed for bluetooth security research and penetration testing. it offers a robust suite of attacks targeting bluetooth classic and ble devices across android, ios, windows, and linux platforms.
Comments are closed.