How To Attack Ios With Android Bluetooth Hacker Cybersecurity Technology Tech Ios

How To Hack Android Macos Ios And Linux Through A Bluetooth Security researcher marc newlin shared how he discovered the bluetooth bug that leaves keyboards vulnerable to injection attacks that can allow attackers to take over user devices. A major bluetooth security flaw, cve 2023 45866 could allow threat actors to take control of android, linux, macos, and ios devices.

New Attack Steals Secret Crypto Keys From Android And Ios Phones Ars A cybersecurity specialist, marc newlin, recently discovered a new bluetooth vulnerability that enables threat actors to take over ios, android, linux, and macos devices. Security researchers have discovered a critical vulnerability in bluetooth that could allow threat actors to take control of android, linux, macos, and ios devices. The iphone makes it easy to connect to bluetooth devices, such as airtags or airpods. however, a hacker has discovered a way to hijack your iphone and flood it with prompts to connect to. A researcher has explained how android, macos, ios, ipados, and linux devices can be remotely hacked by exploiting a vulnerability in the bluetooth protocol.

New Attack Steals Secret Crypto Keys From Android And Ios Phones Ars The iphone makes it easy to connect to bluetooth devices, such as airtags or airpods. however, a hacker has discovered a way to hijack your iphone and flood it with prompts to connect to. A researcher has explained how android, macos, ios, ipados, and linux devices can be remotely hacked by exploiting a vulnerability in the bluetooth protocol. Below is a step by step guide on how to replicate the attack with your own flipper zero. please keep in mind that this information is for informational purposes only — exploiting devices you do. Attackers can exploit a critical bluetooth security vulnerability that's been lurking largely unnoticed for years on macos, ios, android, and linux device platforms. Some smartphones with older versions of android won’t get a fix, making them vulnerable to attack. we would expect other stacks and devices to be vulnerable to this issue. we haven’t yet reproduced the issues and test them in our lab, but we’re working on putting a proof of concept together as well. there may be other devices vulnerable. In late 2023, a critical vulnerability in apple’s bluetooth low energy (ble) protocol made headlines—and for good reason. cve 2023 42941, as it’s formally known, allowed a small open source gadget called the flipper zero to crash iphones by sending spoofed bluetooth pairing requests.
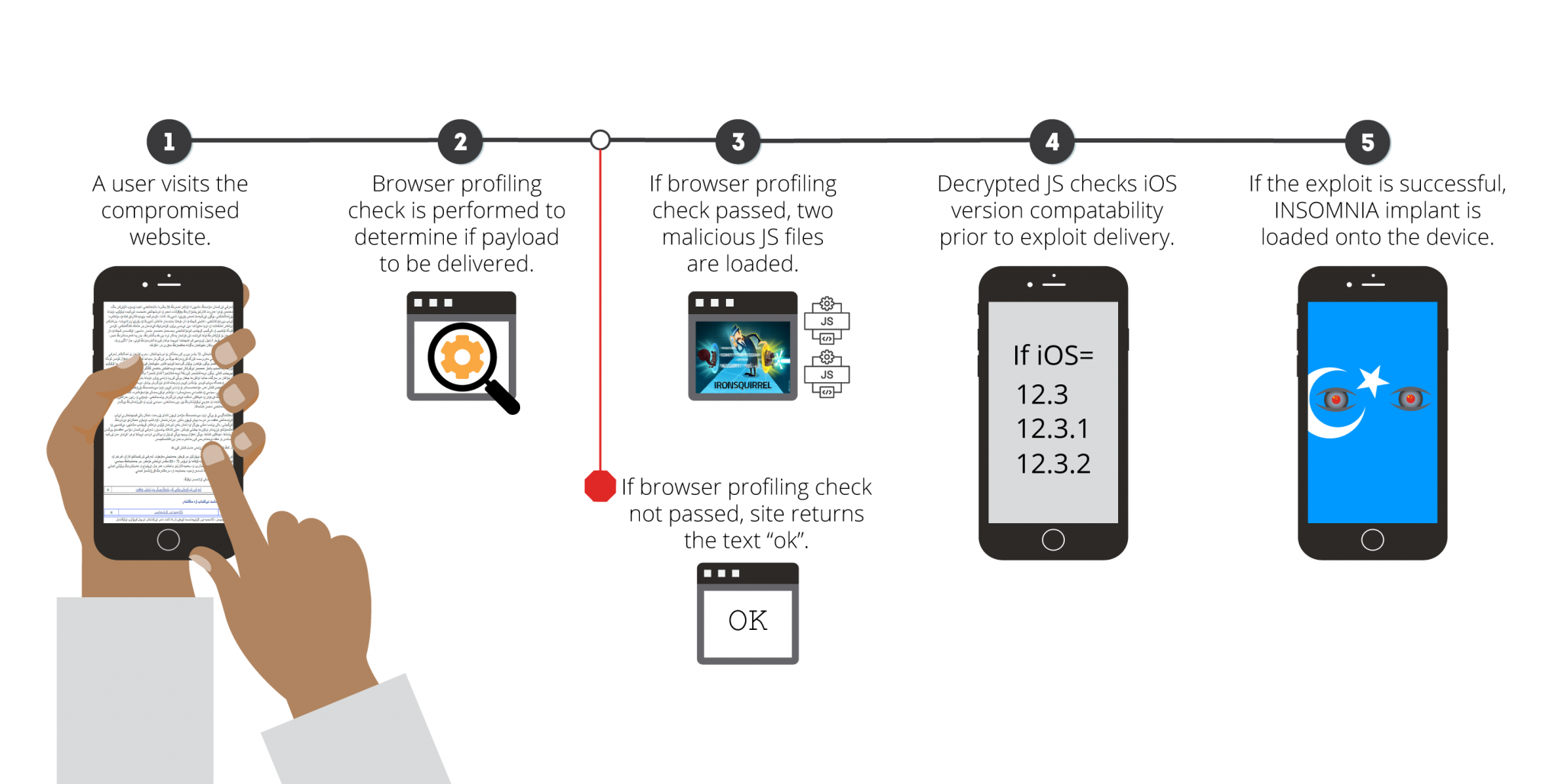
Facebook Shuts Down Hackers Who Infected Ios And Android Devices Ars Below is a step by step guide on how to replicate the attack with your own flipper zero. please keep in mind that this information is for informational purposes only — exploiting devices you do. Attackers can exploit a critical bluetooth security vulnerability that's been lurking largely unnoticed for years on macos, ios, android, and linux device platforms. Some smartphones with older versions of android won’t get a fix, making them vulnerable to attack. we would expect other stacks and devices to be vulnerable to this issue. we haven’t yet reproduced the issues and test them in our lab, but we’re working on putting a proof of concept together as well. there may be other devices vulnerable. In late 2023, a critical vulnerability in apple’s bluetooth low energy (ble) protocol made headlines—and for good reason. cve 2023 42941, as it’s formally known, allowed a small open source gadget called the flipper zero to crash iphones by sending spoofed bluetooth pairing requests.

Hackers Target Ios More Than Android New Research Warns Some smartphones with older versions of android won’t get a fix, making them vulnerable to attack. we would expect other stacks and devices to be vulnerable to this issue. we haven’t yet reproduced the issues and test them in our lab, but we’re working on putting a proof of concept together as well. there may be other devices vulnerable. In late 2023, a critical vulnerability in apple’s bluetooth low energy (ble) protocol made headlines—and for good reason. cve 2023 42941, as it’s formally known, allowed a small open source gadget called the flipper zero to crash iphones by sending spoofed bluetooth pairing requests.

Iphone Owners Told To Use Little Known Two Second Trick To Thwart
Comments are closed.