How The Stride Works

Stride Works Learn what the stride threat model is, how it works, and why it's essential for cybersecurity in 2026. a simple guide for beginners. In the realm of cybersecurity, proactive threat modeling is crucial to safeguarding digital assets. one popular framework that stands out is stride, developed by microsoft. it provides a.

Stride Works The stride framework is built around six core threat categories. each category addresses specific attack vectors and vulnerabilities that can compromise an application’s integrity, confidentiality, and availability. Stride modelling anticipates threats to the target system and builds upon an overarching model of the system often via analysis of data flow diagrams, which may include a breakdown into processes, data stores, data flows, and trust boundaries. We will break down what stride is, walk through how to actually use it with three different real world ish scenarios (think apis, iot, and cloud platforms), share some hard won tips from the trenches, and even suggest some ways you could visualize this stuff later on. The stride threat model offers a structured approach to identifying vulnerabilities, staying ahead of potential threats, and integrating security into modern workflows — all without disrupting your development pipeline.
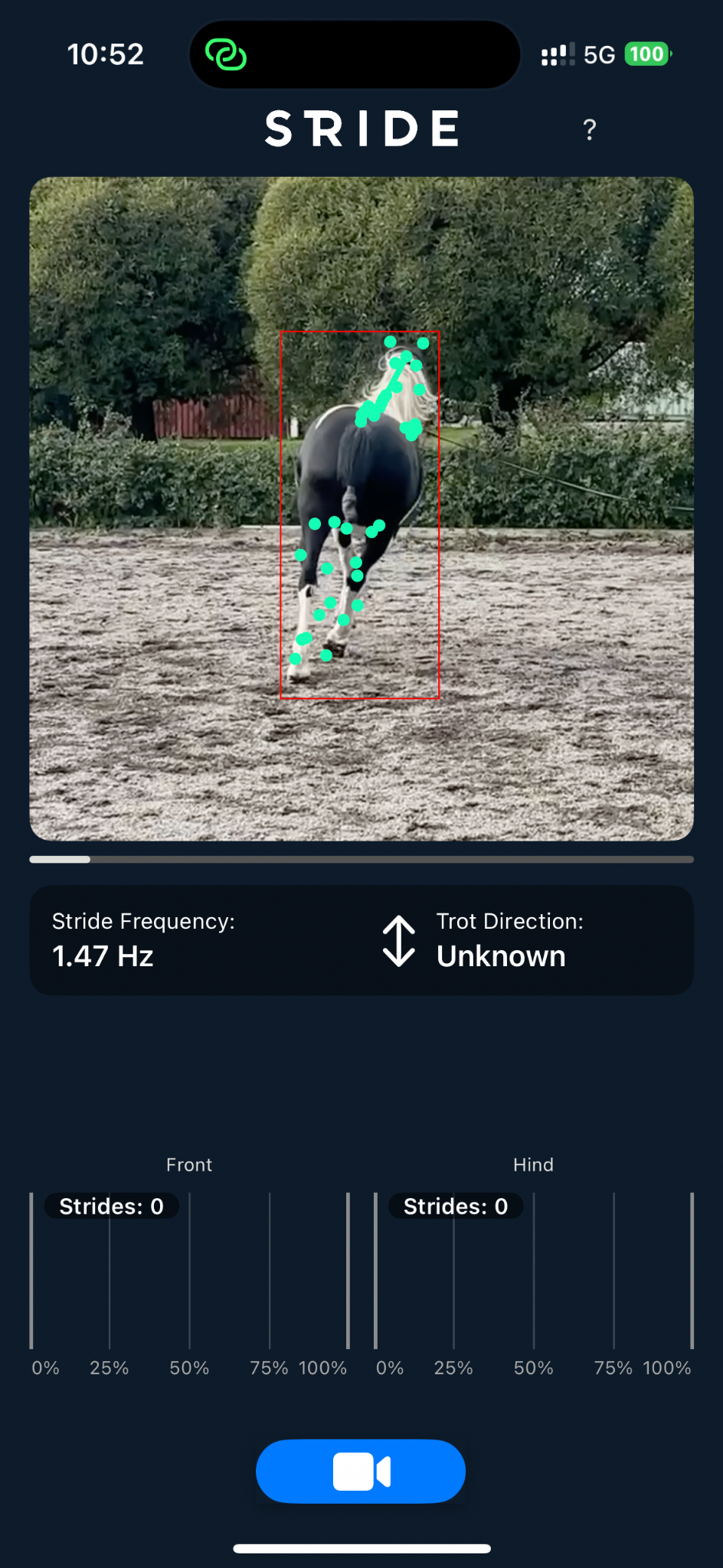
Stride Equine Gait Analysis On Your Phone We will break down what stride is, walk through how to actually use it with three different real world ish scenarios (think apis, iot, and cloud platforms), share some hard won tips from the trenches, and even suggest some ways you could visualize this stuff later on. The stride threat model offers a structured approach to identifying vulnerabilities, staying ahead of potential threats, and integrating security into modern workflows — all without disrupting your development pipeline. We'll explore how this framework works, its key benefits, and practical ways to implement it giving your security team actionable intelligence to harden defenses effectively. Stride is often applied alongside data flow diagrams (dfds) to model system architecture, data movements, trust boundaries, and user interactions. dfds provide a visual representation of how information flows through a system, making it easier to pinpoint where threats might emerge. Stride is an acronym that stands for spoofing, tampering, repudiation, information disclosure, denial of service, and elevation of privilege. this framework and mnemonic was designed to help people developing software identify the types of attacks that software tends to experience. In this article, we review stride and discuss its various elements and best practices for using it. in a few steps, we lay out the groundwork for the basics needed to start threat modeling with the stride framework.

Running And Walking Plans For Mental Wellness We'll explore how this framework works, its key benefits, and practical ways to implement it giving your security team actionable intelligence to harden defenses effectively. Stride is often applied alongside data flow diagrams (dfds) to model system architecture, data movements, trust boundaries, and user interactions. dfds provide a visual representation of how information flows through a system, making it easier to pinpoint where threats might emerge. Stride is an acronym that stands for spoofing, tampering, repudiation, information disclosure, denial of service, and elevation of privilege. this framework and mnemonic was designed to help people developing software identify the types of attacks that software tends to experience. In this article, we review stride and discuss its various elements and best practices for using it. in a few steps, we lay out the groundwork for the basics needed to start threat modeling with the stride framework.

Team About Stride Business Works Stride is an acronym that stands for spoofing, tampering, repudiation, information disclosure, denial of service, and elevation of privilege. this framework and mnemonic was designed to help people developing software identify the types of attacks that software tends to experience. In this article, we review stride and discuss its various elements and best practices for using it. in a few steps, we lay out the groundwork for the basics needed to start threat modeling with the stride framework.

Stride Mental Health About Stride
Comments are closed.