How Strongdm Is Different
How Strongdm Is Different Youtube The strongdm network is comprised of a local client, gateway intermediary, and configuration layer. the local client tunnels requests from the user’s workstation to the gateway, through a single tls 1.2 secured tcp connection. strongdm supports mac, windows, and linux workstations. Strongdm is different from legacy pam vendors because it employs zero trust principles, ensuring continuous verification of access requests and dynamic, context aware access controls.
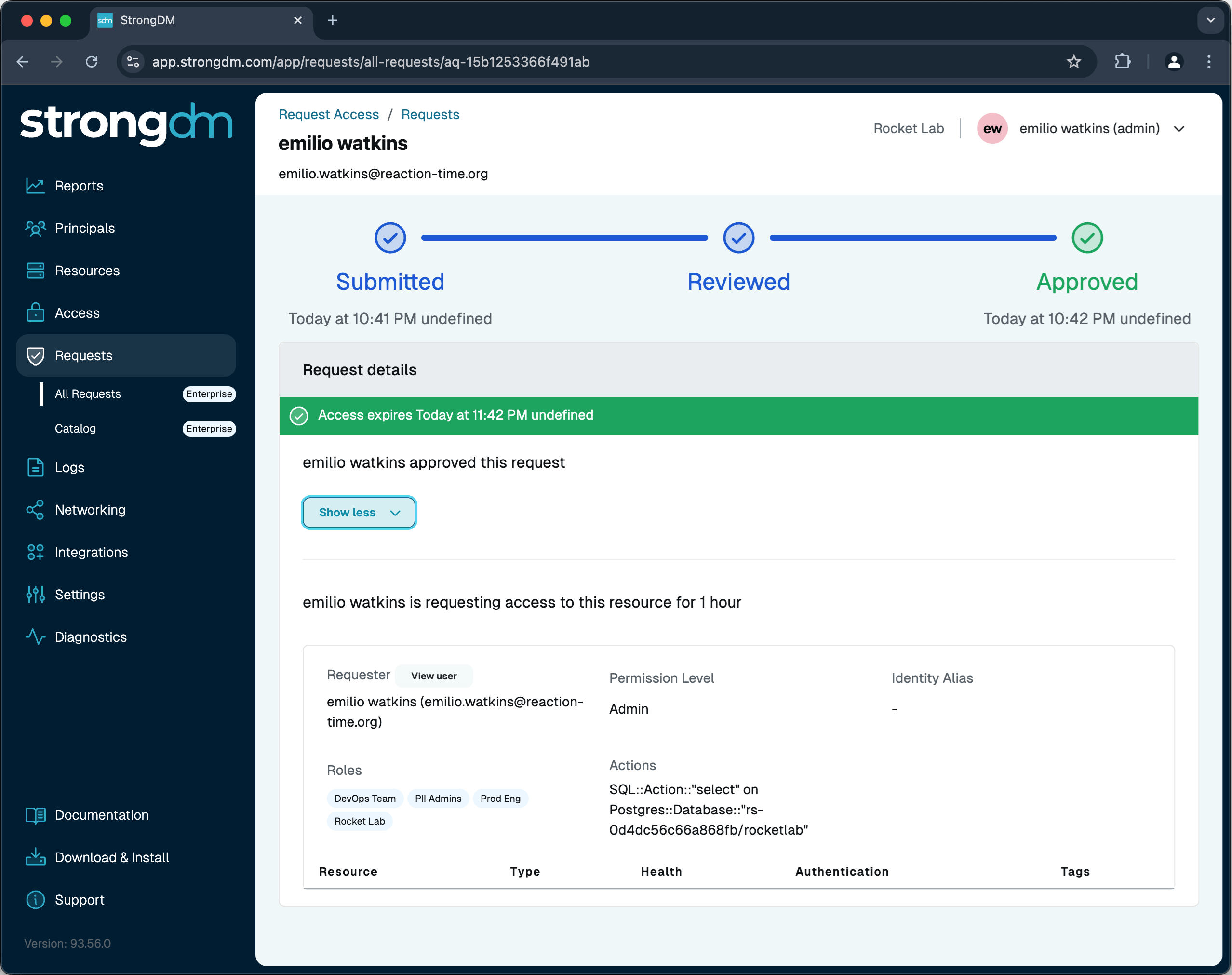
Try It Free Strongdm Explore 33 in depth strongdm reviews and insights from real users verified by gartner, and choose your business software with confidence. Strongdm will accelerate that vision by filling a critical capability gap. our existing platform excels at vault based secrets management, session based privileged access, and governance for human driven workflows. Strongdm combines authentication, authorization, networking, and observability into a single platform, providing secure and auditable access for the precise amount of time that access is needed. Strongdm takes a different approach: continuous, jit runtime authorization evaluated at the moment of action, not at session establishment. most access control systems make a binary decision at connection time: can this identity access this resource? once you're in, you're in.

About Strongdm Strongdm combines authentication, authorization, networking, and observability into a single platform, providing secure and auditable access for the precise amount of time that access is needed. Strongdm takes a different approach: continuous, jit runtime authorization evaluated at the moment of action, not at session establishment. most access control systems make a binary decision at connection time: can this identity access this resource? once you're in, you're in. Read in depth strongdm reviews from real customers and learn about the pricing, features, and more. With the help of capterra, learn about strongdm software reviews, pricing plans, popular comparisons to other network security products and more. Strongdm layers on top of your existing stack with no migration or code changes. deploy in hours, not months, and modernize your access model without breaking what works. Learn about the changes that have been made to strongdm through release notes and through summarized monthly recaps that cover changes made during the last calendar month.

Solutions Strongdm Read in depth strongdm reviews from real customers and learn about the pricing, features, and more. With the help of capterra, learn about strongdm software reviews, pricing plans, popular comparisons to other network security products and more. Strongdm layers on top of your existing stack with no migration or code changes. deploy in hours, not months, and modernize your access model without breaking what works. Learn about the changes that have been made to strongdm through release notes and through summarized monthly recaps that cover changes made during the last calendar month.
Strongdm Observability Experts Strongdm layers on top of your existing stack with no migration or code changes. deploy in hours, not months, and modernize your access model without breaking what works. Learn about the changes that have been made to strongdm through release notes and through summarized monthly recaps that cover changes made during the last calendar month.

Why Strongdm
Comments are closed.