How Side Channel Attacks Work A Technical Deep Dive

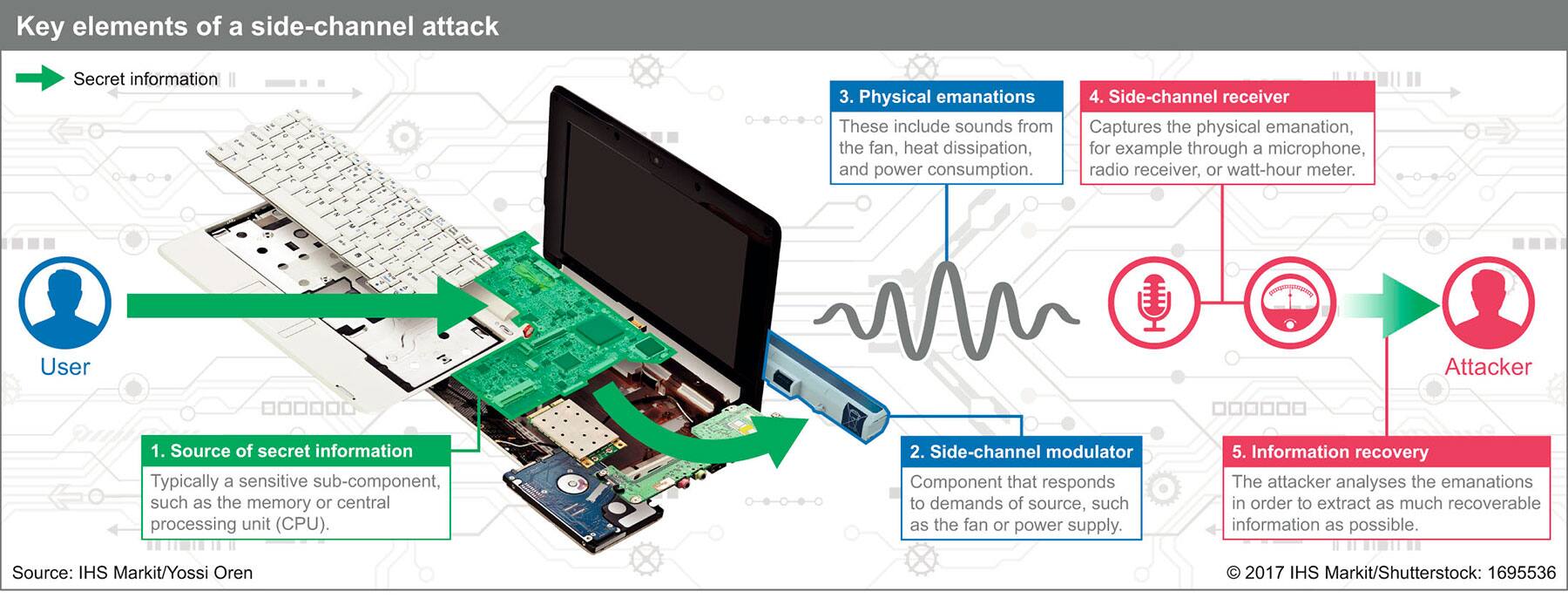
Side Channel Attacks Explained All You Need To Know Rambus In computer security, a side channel attack is a type of security exploit that uses information inadvertently leaked by a system—such as timing, power consumption, or electromagnetic or acoustic emissions—to gain unauthorized access to sensitive information. Learn what a side channel attack is, how it works and how bad actors can implement different types of attacks. examine how to prevent side channel attacks.
Side Channel Attacks Pose Growing Threat To Security Welcome to our in depth guide on side channel attacks! in this video, we'll explore what side channel attacks are, how they exploit hardware vulnerabilities, and the best practices to. Uncover the hidden world of side channel attacks: learn how hackers exploit system vulnerabilities, real world examples, and cutting edge defense strategies. This thorough research gives a full evaluation of side channel assaults, concentrating on their methodology, effect, and the increasing realm of response tactics. understanding the subtleties of side channel attacks is crucial to strengthening the security of cryptographic systems. Explore side channel attacks on cryptosystems: types, history, defenses, and quantum impacts in this detailed guide for cybersecurity experts and cryptography enthusiasts.

Side Channel Attacks Explained Types Examples Dpa Protection This thorough research gives a full evaluation of side channel assaults, concentrating on their methodology, effect, and the increasing realm of response tactics. understanding the subtleties of side channel attacks is crucial to strengthening the security of cryptographic systems. Explore side channel attacks on cryptosystems: types, history, defenses, and quantum impacts in this detailed guide for cybersecurity experts and cryptography enthusiasts. The side channel protection was based on a threshold masking scheme (3 shares, should offer security against standard differential attacks, evaluated by tvla, which we’ll cover in part 2). Such source of information beyond the output speci ed by an abstraction is called a side channel. in this lecture, we will explore the history, examples, and countermeasures of side channel attacks. Due to the significance of side channel attacks, the challenges and overheads of these attack vectors are described through the course of this study. we discuss what side channel attacks are, how they are used, and how they can be prevented through the use of obfuscation techniques. Of the many forms of side channel attacks, one of the most powerful is electromagnetic (em) attacks. in this article, we’ll describe em attacks, how they work, and take a look at specific forms of power attacks that have been used to break cryptography in the past.

Side Channel Attacks Explained Types Examples Dpa Protection The side channel protection was based on a threshold masking scheme (3 shares, should offer security against standard differential attacks, evaluated by tvla, which we’ll cover in part 2). Such source of information beyond the output speci ed by an abstraction is called a side channel. in this lecture, we will explore the history, examples, and countermeasures of side channel attacks. Due to the significance of side channel attacks, the challenges and overheads of these attack vectors are described through the course of this study. we discuss what side channel attacks are, how they are used, and how they can be prevented through the use of obfuscation techniques. Of the many forms of side channel attacks, one of the most powerful is electromagnetic (em) attacks. in this article, we’ll describe em attacks, how they work, and take a look at specific forms of power attacks that have been used to break cryptography in the past.
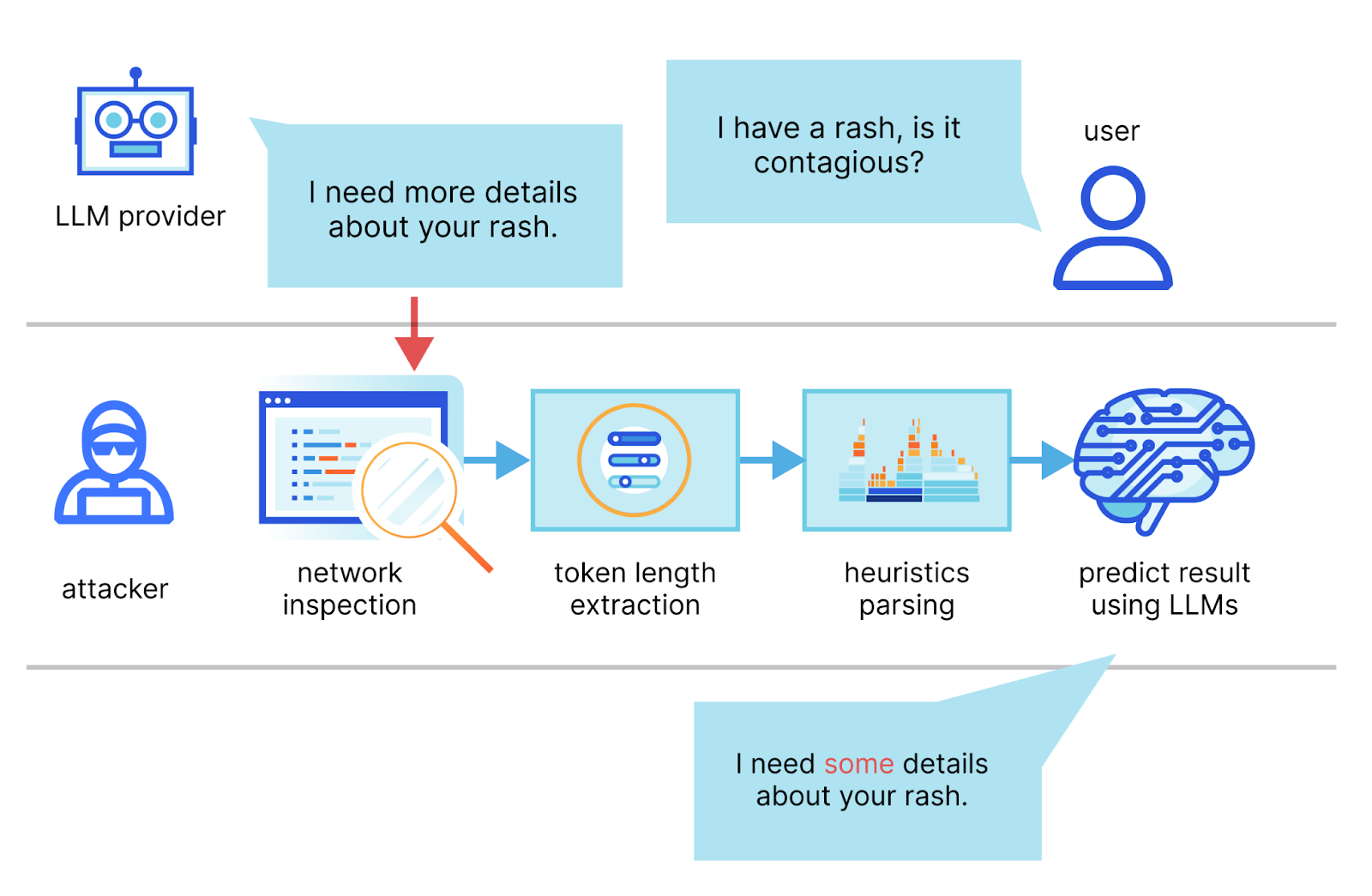
Mitigating A Token Length Side Channel Attack In Our Ai Products Due to the significance of side channel attacks, the challenges and overheads of these attack vectors are described through the course of this study. we discuss what side channel attacks are, how they are used, and how they can be prevented through the use of obfuscation techniques. Of the many forms of side channel attacks, one of the most powerful is electromagnetic (em) attacks. in this article, we’ll describe em attacks, how they work, and take a look at specific forms of power attacks that have been used to break cryptography in the past.
Comments are closed.