How Security Keys Work 2fa Explained

9 Best Hardware Security Keys For Two Factor Authentication 2025 Two factor authentication (2fa) is your next line of defense—and it works. according to microsoft, 2fa blocks 99.9% of automated cyberattacks. that’s huge. whether it’s an sms otp, a fingerprint scan, or a physical security key, adding that extra step stops attackers even if your password is stolen. In this video we’re going to explain how security keys work, and show you how to choose one that’s right for you.

2fa Keys How Do They Work And What Security Advantages Do They Have Learn how two factor authentication (2fa) works in simple steps, which 2fa methods are safest, how to enable it, and what to do if you lose your device. The following sections explain how 2fa works, the methods available, key risks to consider, and best practices for implementing secure and user friendly authentication. If you want the strongest widely available account protection today, use a hardware security key. these are small physical devices, usb and or nfc, that you tap or plug in to verify your login. Learn what two factor authentication (2fa) is, how it works, and why it’s essential for protecting accounts and data. explore 2fa with microsoft security.

Are Security Keys Worth It The Pros And Cons Of This 2fa Method If you want the strongest widely available account protection today, use a hardware security key. these are small physical devices, usb and or nfc, that you tap or plug in to verify your login. Learn what two factor authentication (2fa) is, how it works, and why it’s essential for protecting accounts and data. explore 2fa with microsoft security. Two factor authentication (2fa) enhances security by requiring two forms of identification to gain access to online and physical security points. 2fa is effective in protecting against. Learn what fido2 security keys are, how they enable passwordless authentication, and why they offer stronger protection against phishing and data theft. 2fa is a security process that requires users to verify their identities with two separate types of authentication factors. this is usually a password and something else the user has access to. Various hardware security tokens. on the left and the middle two variants of the yubikey and on the right a fido token from feitian technologies [de] multi factor authentication (mfa), also known as two factor authentication (2fa), is an electronic authentication method in which a user is granted access to a website or application only after successfully presenting two or more distinct types.
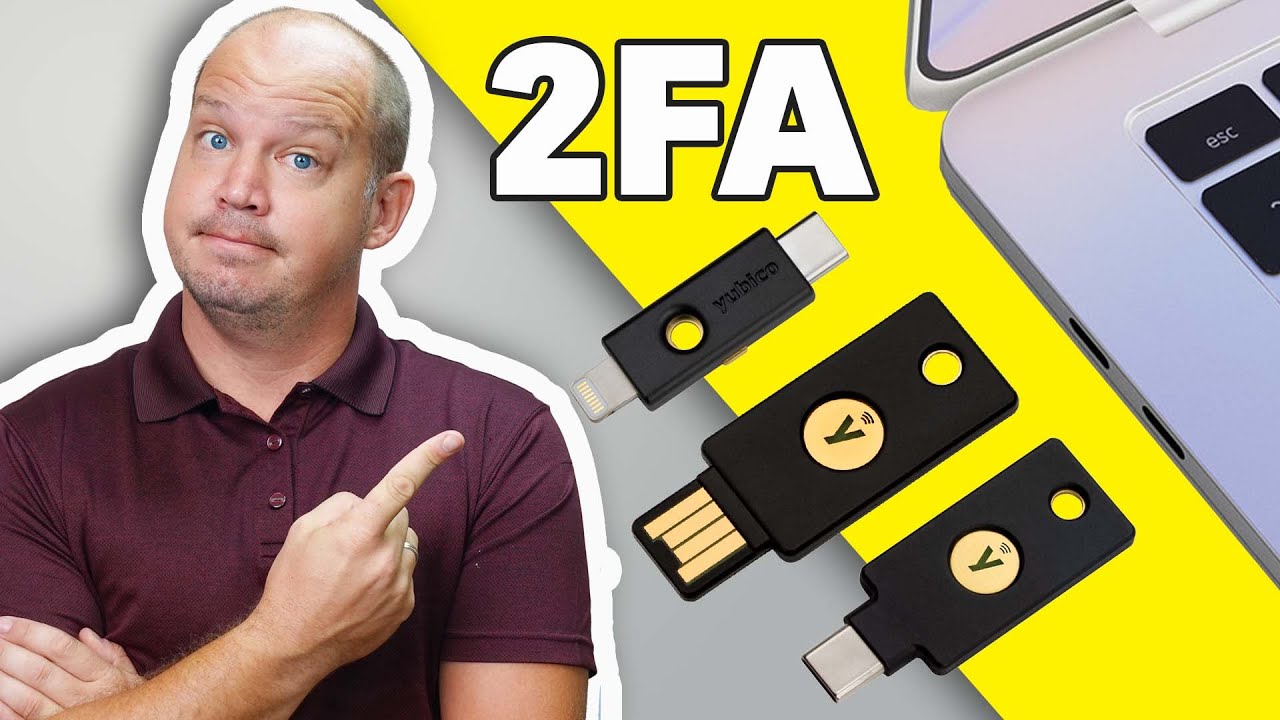
How Do 2fa Security Keys Work At Anna Tichenor Blog Two factor authentication (2fa) enhances security by requiring two forms of identification to gain access to online and physical security points. 2fa is effective in protecting against. Learn what fido2 security keys are, how they enable passwordless authentication, and why they offer stronger protection against phishing and data theft. 2fa is a security process that requires users to verify their identities with two separate types of authentication factors. this is usually a password and something else the user has access to. Various hardware security tokens. on the left and the middle two variants of the yubikey and on the right a fido token from feitian technologies [de] multi factor authentication (mfa), also known as two factor authentication (2fa), is an electronic authentication method in which a user is granted access to a website or application only after successfully presenting two or more distinct types.
Comments are closed.