How Post Quantum Cryptography Affects Security And Encryption

How Post Quantum Cryptography Affects Security And Encryption Current widely used public key cryptographic systems including rsa, elliptic curve cryptography (ecc), and diffie hellman key exchange are particularly vulnerable to quantum attacks. As quantum computers evolve from theoretical concepts to practical reality, they pose an existential threat to the encryption algorithms that protect everything from personal communications to national security secrets.

Post Quantum Cryptography Redjack Post quantum cryptography (pqc) has become the primary defense against the vulnerabilities that large scale quantum computing introduces to traditional cryptographic systems. Post quantum cryptography (pqc) has arisen as a vital domain, concentrating on cryptographic techniques founded on difficulties presumed to withstand quantum assaults. The technical challenges and limitations of current quantum resistant algorithms are examined, along with insights from recent research and discussions on emerging trends in post quantum. As quantum computing accelerates, explore how post quantum cryptography can strengthen cybersecurity, prevent data breaches, and meet nist standards.
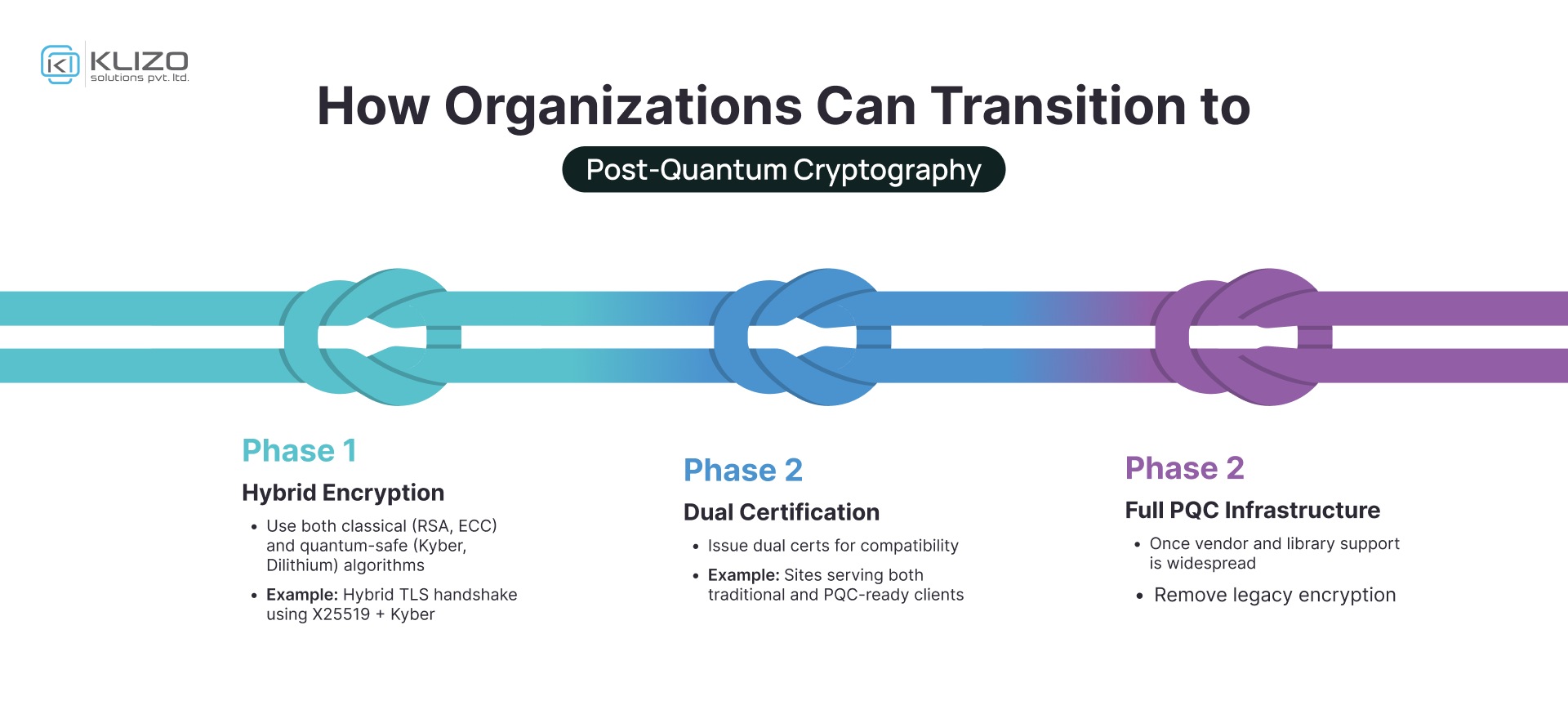
Post Quantum Cryptography The Future Of Secure Computing Klizos The technical challenges and limitations of current quantum resistant algorithms are examined, along with insights from recent research and discussions on emerging trends in post quantum. As quantum computing accelerates, explore how post quantum cryptography can strengthen cybersecurity, prevent data breaches, and meet nist standards. As researchers around the world race to build quantum computers that could break the current encryption providing security and privacy for our digital lives, nist is helping to secure our future by developing algorithms to protect our data and systems. nist has already released three post quantum cryptography standards that can be implemented now to secure a wide range of electronic. This review paper comprehensively examines the transformative impact of quantum computing on cybersecurity, highlighting vulnerabilities introduced by algorithms like shor’s and grover’s, which can break widely used encryption methods such as rsa, ecc, and aes. While post quantum cryptography uses mathematics to resist quantum attacks, quantum key distribution (qkd) takes a fundamentally different approach – using the laws of quantum mechanics to detect eavesdropping and distribute encryption keys with information theoretic security. One key concern raised by enterprises in response to the pqc risk is the timeline in which pqc threats can be realized. for instance, smart and connected vehicles that need to protect user safety and privacy will likely have lifespans that extend at least two decades, into the 2040s.
Comments are closed.