How Permissions Work In Aws Lambda
A Visual Introduction To Aws Lambda Permissions Harprit Learn how to manage permissions to the lambda api and your lambda resources using iam policies. Use iam policies to configure permissions for iam users to create, delete, modify, invoke, and monitor lambda functions, and view a lambda function's configuration.
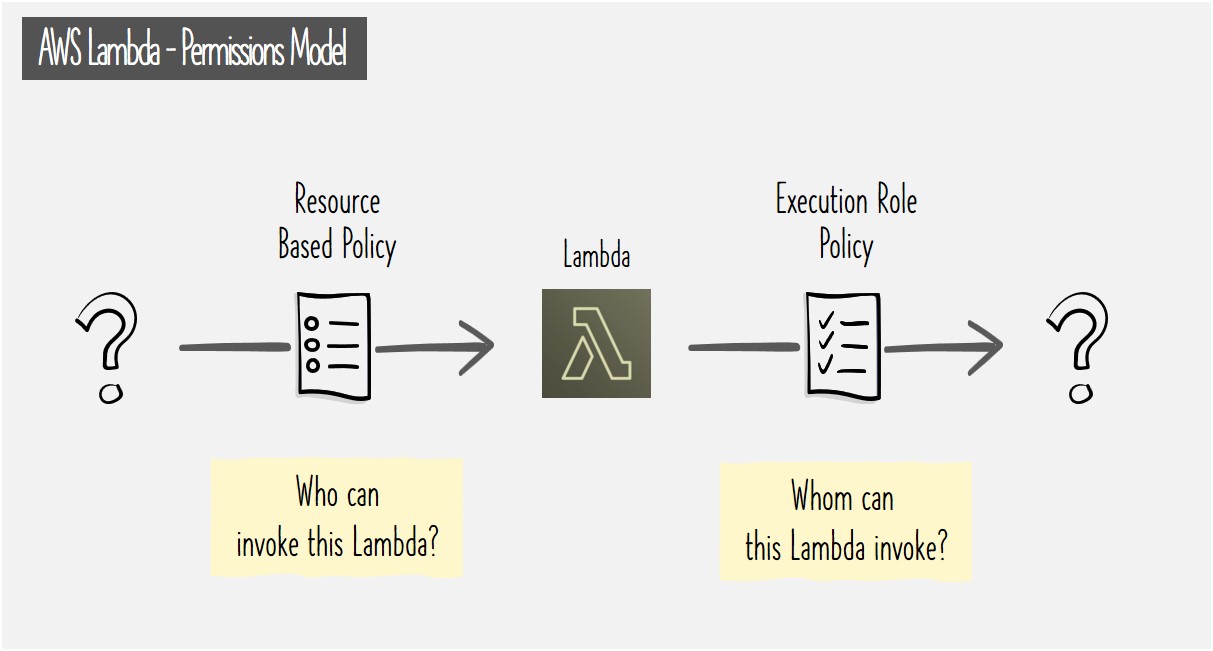
A Visual Introduction To Aws Lambda Permissions Harprit Learn how to manage permissions to the lambda api and your lambda resources using iam policies. In this article we will explore the permissions and connection capabilities that allow aws lambda and other aws services to connect to each other. lambda functions involve two aspects that determine the required permissions:. We can manage permissions in a permissions policy that you can apply to iam users, groups, or roles in order to execute lambda functions with policy definitions. In this blog post, i'll guide you through setting up permissions for your aws lambda functions. we'll cover iam policies in detail, and i'll share a handy shortcut using aws sam to streamline the process. before we dive in, let’s quickly review how lambda functions work in an event driven application.
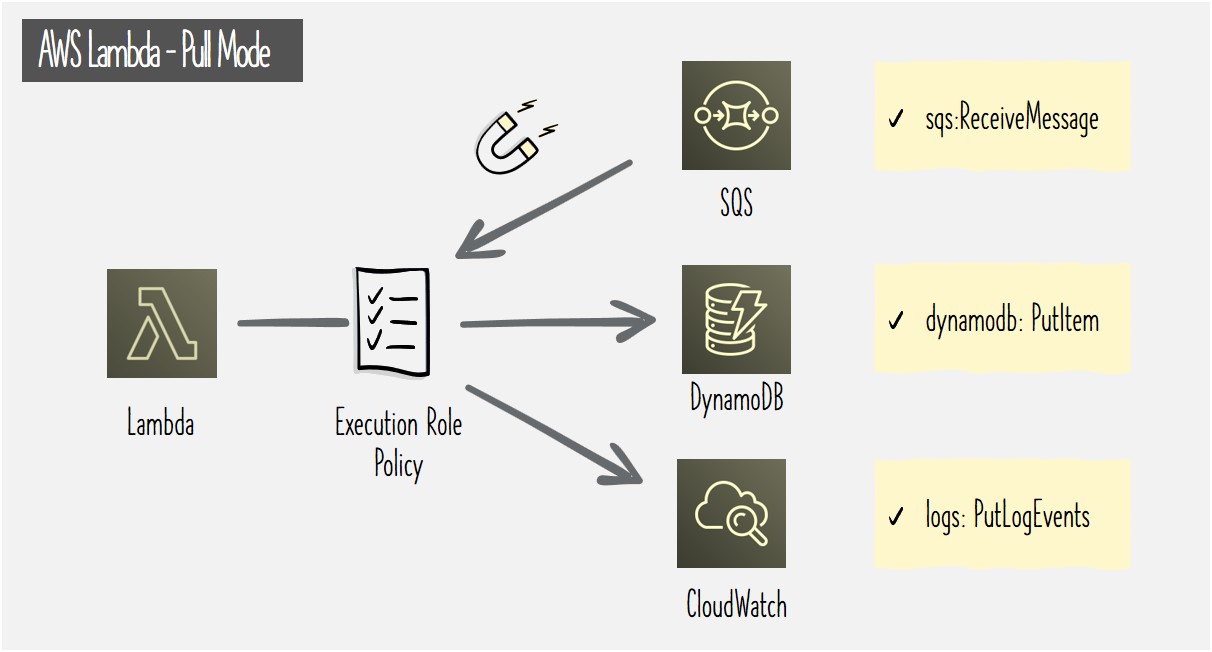
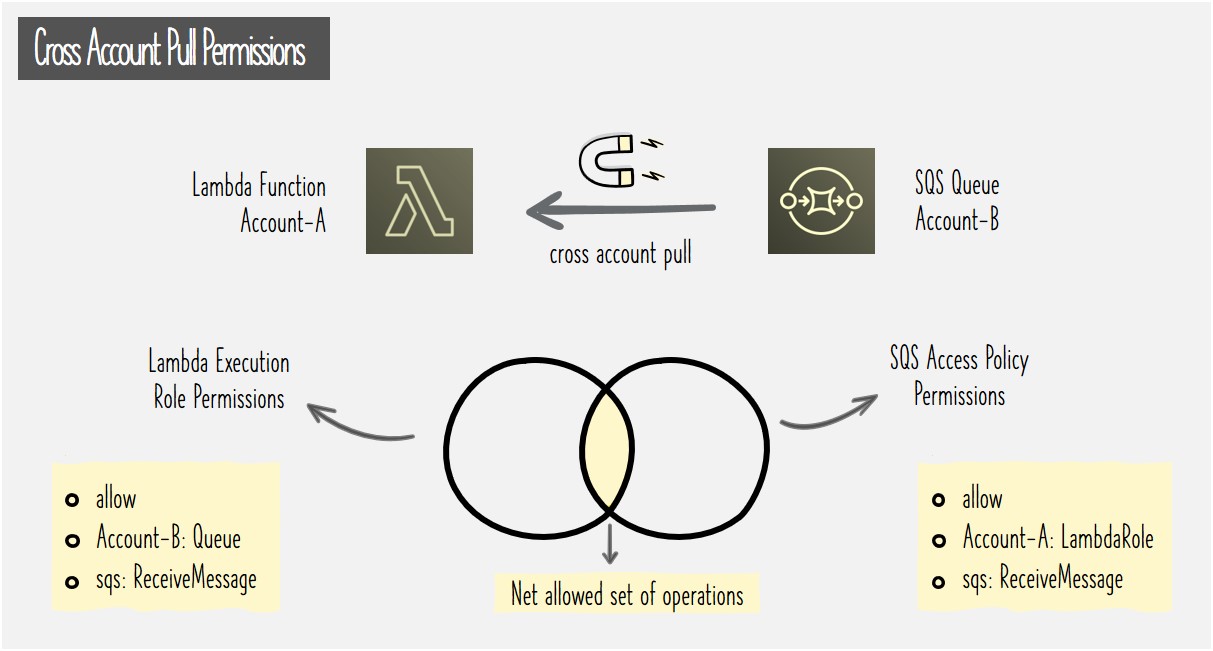
A Visual Introduction To Aws Lambda Permissions Harprit We can manage permissions in a permissions policy that you can apply to iam users, groups, or roles in order to execute lambda functions with policy definitions. In this blog post, i'll guide you through setting up permissions for your aws lambda functions. we'll cover iam policies in detail, and i'll share a handy shortcut using aws sam to streamline the process. before we dive in, let’s quickly review how lambda functions work in an event driven application. In this comprehensive 2500 word guide, i‘ll teach you expert techniques for locking down aws lambda permissions using iam roles and resource based policies. follow along and you‘ll have the knowledge to confidently restrict access to your serverless functions. Iam attaches permissions to lambda functions to ensure that only the intended services and resources should be accessed by aws lambda. by attaching the roles and permissions to the lambda function, users can minimize the unauthorized access or misuse of aws resources. Explore aws lambda iam roles and permissions in this ultimate guide. learn how to master serverless security to protect your applications and data effectively. In aws lambda, execution roles and iam permissions play a critical role in controlling which aws resources your function can access. these roles ensure that functions can interact securely with other services like s3, dynamodb, or cloudwatch without embedding credentials in your code.
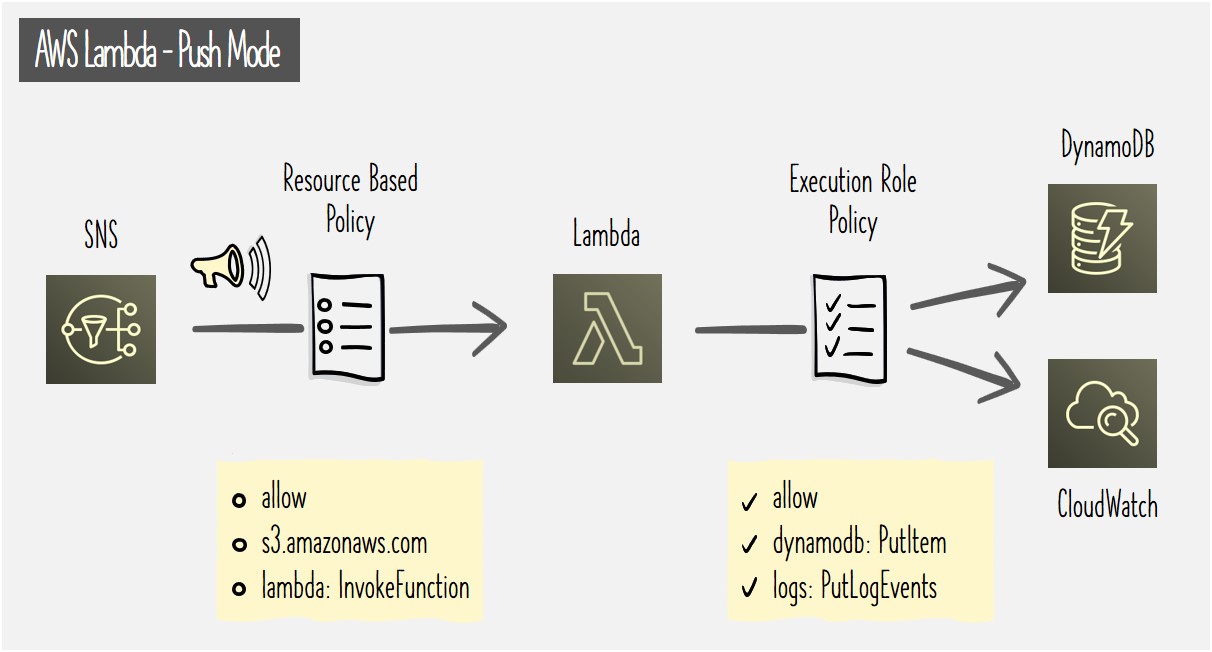
A Visual Introduction To Aws Lambda Permissions Harprit In this comprehensive 2500 word guide, i‘ll teach you expert techniques for locking down aws lambda permissions using iam roles and resource based policies. follow along and you‘ll have the knowledge to confidently restrict access to your serverless functions. Iam attaches permissions to lambda functions to ensure that only the intended services and resources should be accessed by aws lambda. by attaching the roles and permissions to the lambda function, users can minimize the unauthorized access or misuse of aws resources. Explore aws lambda iam roles and permissions in this ultimate guide. learn how to master serverless security to protect your applications and data effectively. In aws lambda, execution roles and iam permissions play a critical role in controlling which aws resources your function can access. these roles ensure that functions can interact securely with other services like s3, dynamodb, or cloudwatch without embedding credentials in your code.
Comments are closed.