How Hackers Use Github To Find Sql Injection Vulnerabilities Insane Method

Github On Twitter The Ghsecuritylab Team Shared A Quick Primer To A comprehensive sql injection detection and exploitation tool with support for multiple database types and advanced evasion techniques. To associate your repository with the sql injection topic, visit your repo's landing page and select "manage topics." github is where people build software. more than 150 million people use github to discover, fork, and contribute to over 420 million projects.
How To Secure Apis From Sql Injection Vulnerabilities Zuplo Learning The sql injection knowledge base is a comprehensive resource designed to help security professionals and developers understand, identify, and test sql injection vulnerabilities across various database systems. Stealthsql: the ultimate sql injection tool dive into the shadows of web security with stealthsql. harness the power of stealthsql to silently unveil vulnerabilities in sql databases. Objective: our study looks at open source projects written in java and python to examine the current state of sql injection vulnerabilities. we take a deeper look into the vulnerabilities’ code patterns and discuss suitable prevention methods. method: the open source projects were mined from github. Learn the exact method hackers and bug bounty hunters use to discover sql injection vulnerabilities using github code search.in this video, we’ll break down:.
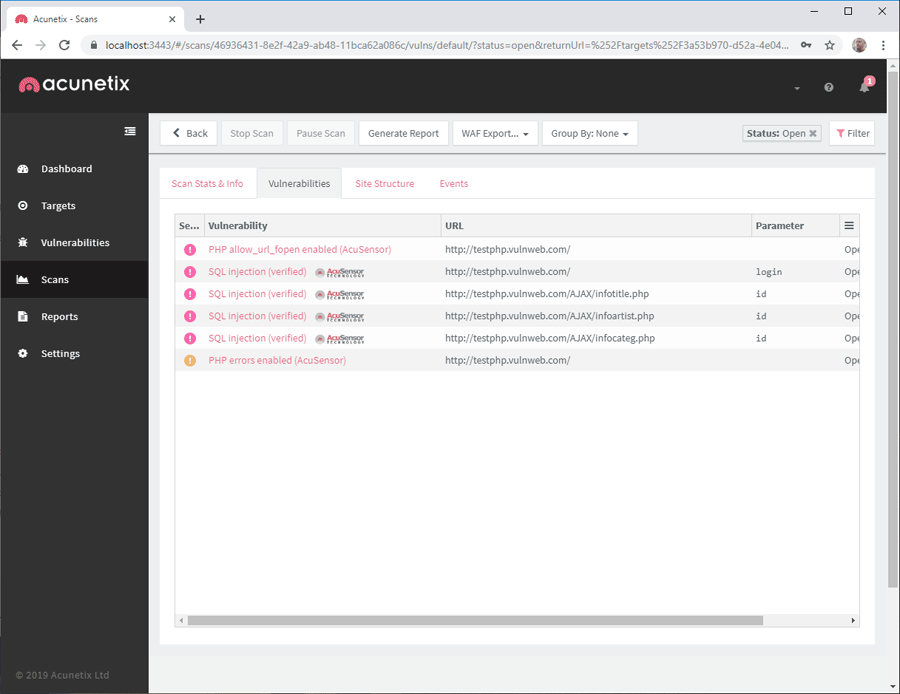
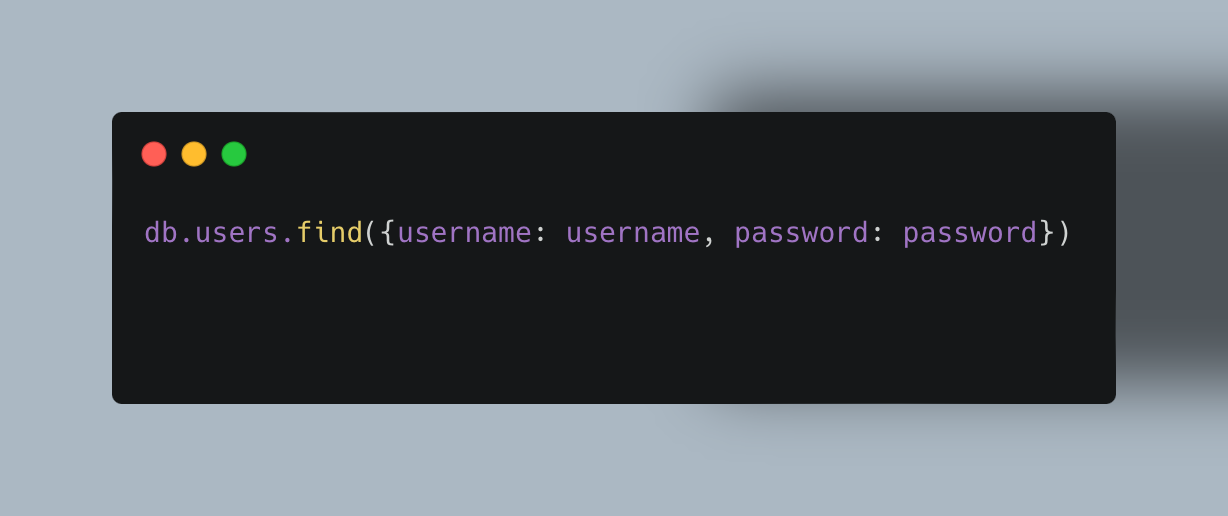
How To Test For Sql Injection Attacks Vulnerabilities Objective: our study looks at open source projects written in java and python to examine the current state of sql injection vulnerabilities. we take a deeper look into the vulnerabilities’ code patterns and discuss suitable prevention methods. method: the open source projects were mined from github. Learn the exact method hackers and bug bounty hunters use to discover sql injection vulnerabilities using github code search.in this video, we’ll break down:. In this article, i explain how to bypass waf protections and discover hidden sql injection points by targeting the server’s original ip address. want to master sql injection from the ground up? these videos covers essential tools, techniques and learning resources to help you go from beginner to pro in no time. test both get and post requests. In this guide, we explain basic and advanced sql injection (sqli) techniques, including blind sqli, time based attacks and out of band (oob) callbacks. you'll learn how to tailor payloads to the sql statement in play, incorporate them into your bug bounty workflow, and detect and exploit sqli vulnerabilities – even in hardened systems. what is sql?. Sql injection (sqli) is a vulnerability that lets attackers interfere with a web application’s database queries. but to exploit it effectively, you need to understand how databases work, where injections happen, and what makes them dangerous. let’s break it down in simple terms. Identifying vulnerabilities in sql injection, a serious web application security vulnerability, was the primary objective of the evaluation. to validate my suspicions, i began with manual testing and then employed automated tools to probe the system further.
Comments are closed.