How Hackers Cover Their Tracks On An Exploited Linux Server With Shell

Free Video How To Secure Ssh Linux Security With Hackersploit From Attempt to hide attackers presence on the system so the system appears uncompromised. modify the system logs and delete their activity during the attack. you can mitigate damage by reducing footprint by e.g. making your access disguise a legit process. Clearing logs after gaining unauthorized access to a system, such as through hacking, is a common practice used by attackers to cover their tracks and avoid detection.
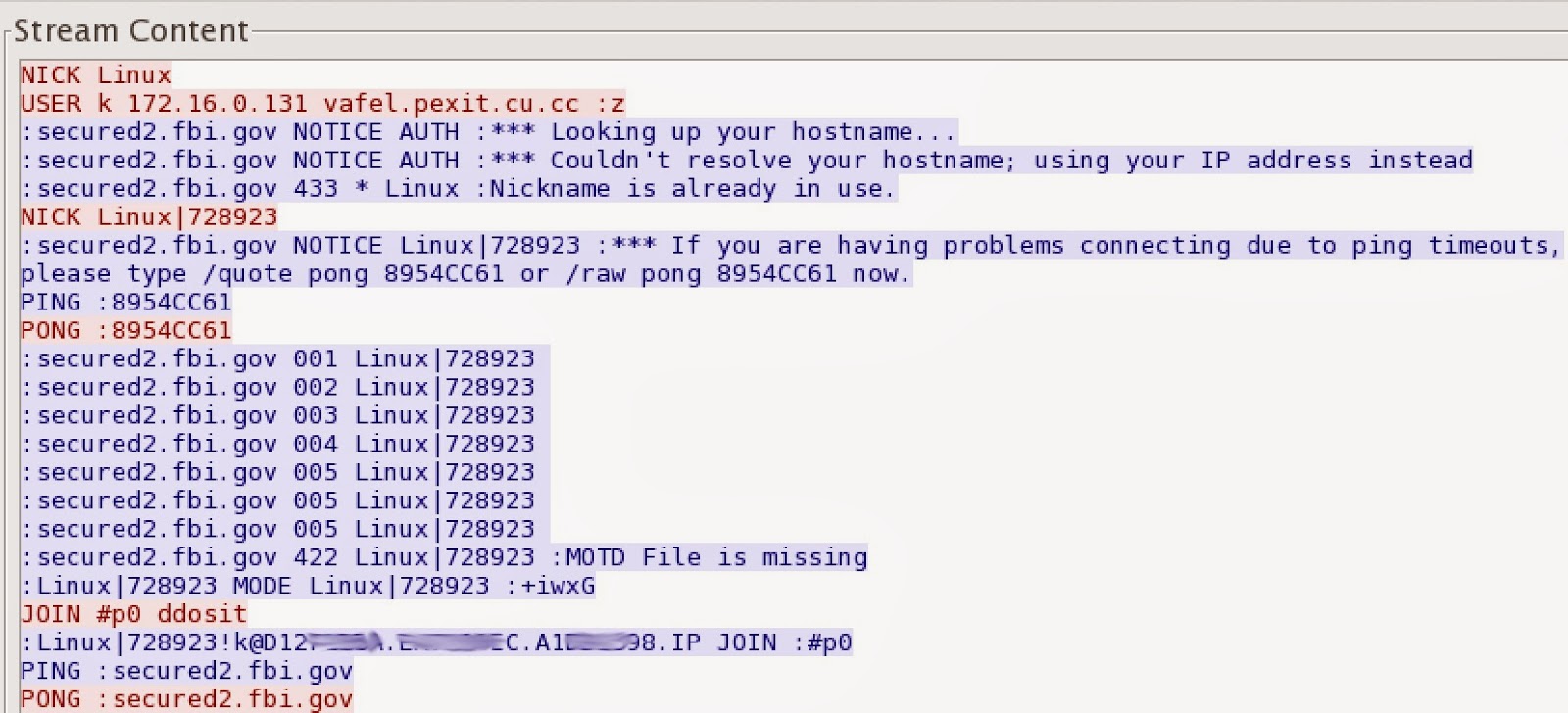
What A Successful Exploit Of A Linux Server Looks Like Ars Technica Shell script to cover your tracks on unix systems. designed for pen testing covering tracks phase, before exiting the infected server. or, permanently disable system logs for post exploitation. installation. with sudo : without sudo : you can now use the tool using the executable. Attackers often modify shell initialization files (.bashrc, .bash profile, .zshrc) to execute malicious code whenever a user logs in or opens a new terminal. this provides per user persistence that can be particularly stealthy. step‑by‑step guide explaining what this does and how to use it:. This documentation provides a comprehensive breakdown of common hacking techniques used to gain unauthorized access to a server and offers insight into preventive measures to secure servers against such attacks. Here are some tactics and techniques cybercriminals are employing to cover their tracks.
What A Successful Exploit Of A Linux Server Looks Like Ars Technica This documentation provides a comprehensive breakdown of common hacking techniques used to gain unauthorized access to a server and offers insight into preventive measures to secure servers against such attacks. Here are some tactics and techniques cybercriminals are employing to cover their tracks. Moonwalk is a 400 kb single binary executable that can clear your traces while penetration testing a unix machine. it saves the state of system logs pre exploitation and reverts that state including the filesystem timestamps post exploitation leaving zero traces of a ghost in the shell. Delete the logs and bash history on hacked linux computers to hide your tracks and avoid being detected. as a hacker, the ultimate stage of exploitation is to conceal their tracks, which entails erasing all activity and records in order to prevent detection. Learn to clear logs and bash history on hacked linux systems. follow our guide to cover your tracks and maintain stealth during penetration testing. An investigator could check the bash history to track the origin of the attack and the commands used by the attacker to compromise the system. attackers can use the following commands to clear their bash shell tracks:.

Linux Basics For Hackers 2nd Edition Getting Started With Networking Moonwalk is a 400 kb single binary executable that can clear your traces while penetration testing a unix machine. it saves the state of system logs pre exploitation and reverts that state including the filesystem timestamps post exploitation leaving zero traces of a ghost in the shell. Delete the logs and bash history on hacked linux computers to hide your tracks and avoid being detected. as a hacker, the ultimate stage of exploitation is to conceal their tracks, which entails erasing all activity and records in order to prevent detection. Learn to clear logs and bash history on hacked linux systems. follow our guide to cover your tracks and maintain stealth during penetration testing. An investigator could check the bash history to track the origin of the attack and the commands used by the attacker to compromise the system. attackers can use the following commands to clear their bash shell tracks:.
Comments are closed.