How Does Red Hat Openshift Help With Container Security

Red Hat Openshift Container Platform Download Free Pdf Cloud Adapting to today’s security challenges means protecting a mix of virtual machines, containers, and ai enabled workloads deployed across clouds, datacenters, and edge environments. The goal of this guide is to understand the incredible security benefits of using openshift container platform for your containerized workloads and how the entire red hat ecosystem plays a part in making and keeping containers secure.

Openshift Container Platform 4 13 Security And Compliance En Us Pdf Efficient openshift security ensures that containerized applications are shielded from threats, enabling a secure and resilient environment. this proactive approach to securing openshift is crucial for supporting continuous delivery and maintaining trust in the system’s reliability. Red hat openshift enables applications inside and outside kubernetes clusters to run applications where it makes the most sense. openshift's basic security includes security hardening and fips (federal information processing standard) compliant encryption (fips 140 2 level 1). The openshift container security operator is a component that helps to enhance the security of container images within an openshift cluster. it works by integrating with the quay container registry, a container image storage and distribution solution developed by red hat. Red hat openshift container platform (ocp) provides a robust and flexible environment for deploying and managing containerized applications, but navigating its security and compliance features effectively is crucial to protect data, workloads, and infrastructure.
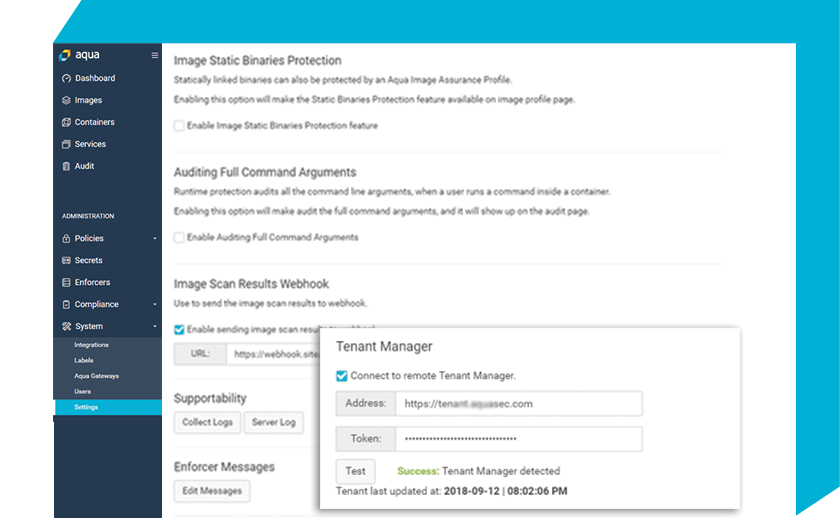
Cloud Native Security For Red Hat Openshift Aqua The openshift container security operator is a component that helps to enhance the security of container images within an openshift cluster. it works by integrating with the quay container registry, a container image storage and distribution solution developed by red hat. Red hat openshift container platform (ocp) provides a robust and flexible environment for deploying and managing containerized applications, but navigating its security and compliance features effectively is crucial to protect data, workloads, and infrastructure. Red hat® openshift container platform enables an improved security posture with the addition of many capabilities that greatly increase the security of the platform. The cyberark identity security platform delivers powerful protection for red hat openshift virtualization environments, securing access to virtual machines, red hat openshift components and containerized applications. By understanding the openshift security model, implementing strong authentication and authorization mechanisms, securing container configurations, and enforcing network policies, you can enhance the overall security posture of your applications. This article describes the benefits of using confidential containers to safeguard sensitive data and explains how confidential containers function within azure red hat openshift.
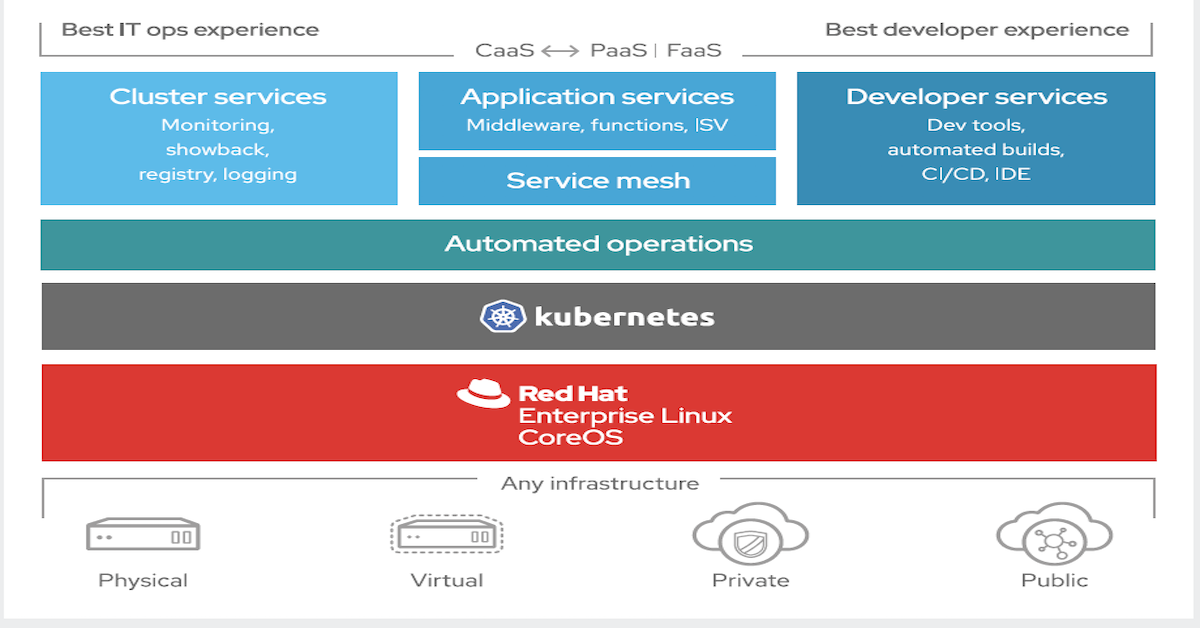
Red Hat Openshift Container Platform Datacrunch Lab Red hat® openshift container platform enables an improved security posture with the addition of many capabilities that greatly increase the security of the platform. The cyberark identity security platform delivers powerful protection for red hat openshift virtualization environments, securing access to virtual machines, red hat openshift components and containerized applications. By understanding the openshift security model, implementing strong authentication and authorization mechanisms, securing container configurations, and enforcing network policies, you can enhance the overall security posture of your applications. This article describes the benefits of using confidential containers to safeguard sensitive data and explains how confidential containers function within azure red hat openshift.

Apa Itu Red Hat Openshift Container Indonesian Cloud By understanding the openshift security model, implementing strong authentication and authorization mechanisms, securing container configurations, and enforcing network policies, you can enhance the overall security posture of your applications. This article describes the benefits of using confidential containers to safeguard sensitive data and explains how confidential containers function within azure red hat openshift.

Red Hat Openshift Container Platform White Paper Data Lakehouse With
Comments are closed.