How Does Re Identification Work
Github Amit Prasad Re Identification Rethinking The Re Identifcation Object re identification (re id) is a specialized task in computer vision (cv) designed to match a specific object or individual across different non overlapping camera views or over extended periods. Re identification is the process of linking the information from a de identified data set to a particular data subject or subjects. this may be pii or it may be about identifying devices in the iot, which then means that if the device can be associated with a user, pii may be exposed.
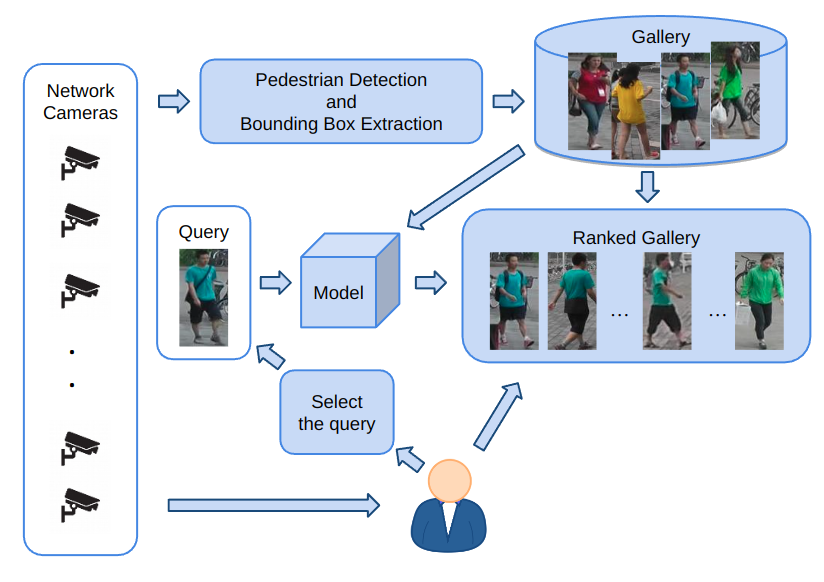
Person Re Identification Pra Lab The task of person re identification (re id) is to identify the same person in different images obtained from different cameras or at different points in time. that is, a set of images is given, which depict different people in different conditions and from different angles. Person re identification (re id) emerges as a captivating realm within computer vision, dedicated to the task of recognizing the same individual across diverse camera angles or locations. P erson re identification is a process that identifies individuals who appear in different non overlapping camera views. this process does not rely on facial recognition but instead considers clothing details, body shape features, and other attributes related to appearance. Person re identification (or person re id for short) is defined as the problem of matching people across disjoint camera views in a multi camera system. it is useful for a number of public security applications such as intelligent camera surveillance systems.
Github Junhongmit Person Reidentification System Person Re P erson re identification is a process that identifies individuals who appear in different non overlapping camera views. this process does not rely on facial recognition but instead considers clothing details, body shape features, and other attributes related to appearance. Person re identification (or person re id for short) is defined as the problem of matching people across disjoint camera views in a multi camera system. it is useful for a number of public security applications such as intelligent camera surveillance systems. In this episode, florian matusek explains how re identification of objects in video surveillance works. Whenever we meet a new person, we identify that person to be new and get to know them. if we meet the same person again, we recognize that person’s identity . this process is called. The approach is based on an expert evaluation of a dataset to designate some identifiers as "direct" and some as "indirect." proponents of this approach argue that re identification can be avoided by limiting access to "additional information" that is kept separately by the controller. It delves into three crucial facets; encompassing succinct explanations of video re id techniques along with their constraints, pivotal breakthroughs coupled with the technical hurdles faced, and the architectural framework underpinning these developments.
Full Re Identification Process Local Re Identification Download In this episode, florian matusek explains how re identification of objects in video surveillance works. Whenever we meet a new person, we identify that person to be new and get to know them. if we meet the same person again, we recognize that person’s identity . this process is called. The approach is based on an expert evaluation of a dataset to designate some identifiers as "direct" and some as "indirect." proponents of this approach argue that re identification can be avoided by limiting access to "additional information" that is kept separately by the controller. It delves into three crucial facets; encompassing succinct explanations of video re id techniques along with their constraints, pivotal breakthroughs coupled with the technical hurdles faced, and the architectural framework underpinning these developments.
Comments are closed.