How Does Malware Spread

How Does Malware Spread Understanding how malware spreads is crucial to preventing infections and protecting your devices and networks. cybercriminals employ various tactics to propagate malware, ranging from social engineering to exploiting vulnerabilities. Learn about malware, how cybercriminals spread malware, how you can detect malware and how you can stay protected against it.
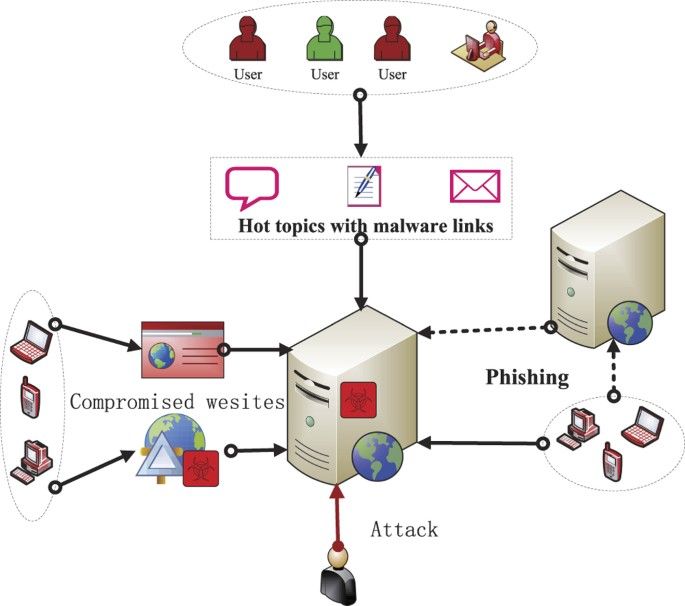
How Does Malware Spread Through The Network Darwin S Data All malware poses a threat, and the key to protecting yourself and the networks you work in is understanding how it spreads and how to stay vigilant. here are the most frequent methods used to infect devices, along with tips on how to stay safe online. Learn how malware spreads through email attachments, fake downloads, infected websites, and other common cyberattack methods. Threat actors use a variety of channels to distribute malware, including phishing attacks, compromised credentials, exploit kits, compromised msps and pirated software. Viruses and worms are both types that are made to spread, and trojans disguise themselves as something legitimate. the type of malware almost doesn't matter though — they're all bad and you.

How Does Malware Spread Citizenside Threat actors use a variety of channels to distribute malware, including phishing attacks, compromised credentials, exploit kits, compromised msps and pirated software. Viruses and worms are both types that are made to spread, and trojans disguise themselves as something legitimate. the type of malware almost doesn't matter though — they're all bad and you. Once malware infects a network or computer system, it can quickly spread to other connected devices and systems, sometimes without any action by the user. this makes malware extremely dangerous and difficult to remove once it gets a foothold. When malware is active on your network, it seeks vulnerabilities that will allow it to spread to other devices. exploiting well known and longstanding software vulnerabilities that should have been patched is a very common vector for many of the above attacks. Malware is designed to steal sensitive information, damage devices, or gain unauthorized access to networks. it can affect desktops, laptops, mobile devices, and even iot devices. This process encompasses how malicious software, commonly referred to as malware or 'virus', is able to move from one device to another. gaining an understanding of how this transmission takes place is critical in ensuring protection against such security threats.
Comments are closed.