How Do Api Tokens Work Next Lvl Programming
Advanced Api Tokens How do api tokens work? in this informative video, we’ll break down the concept of api tokens and their role in accessing apis securely. A guide to api tokens and their use in securing api access. learn about the anatomy, types, and security measures of api tokens.
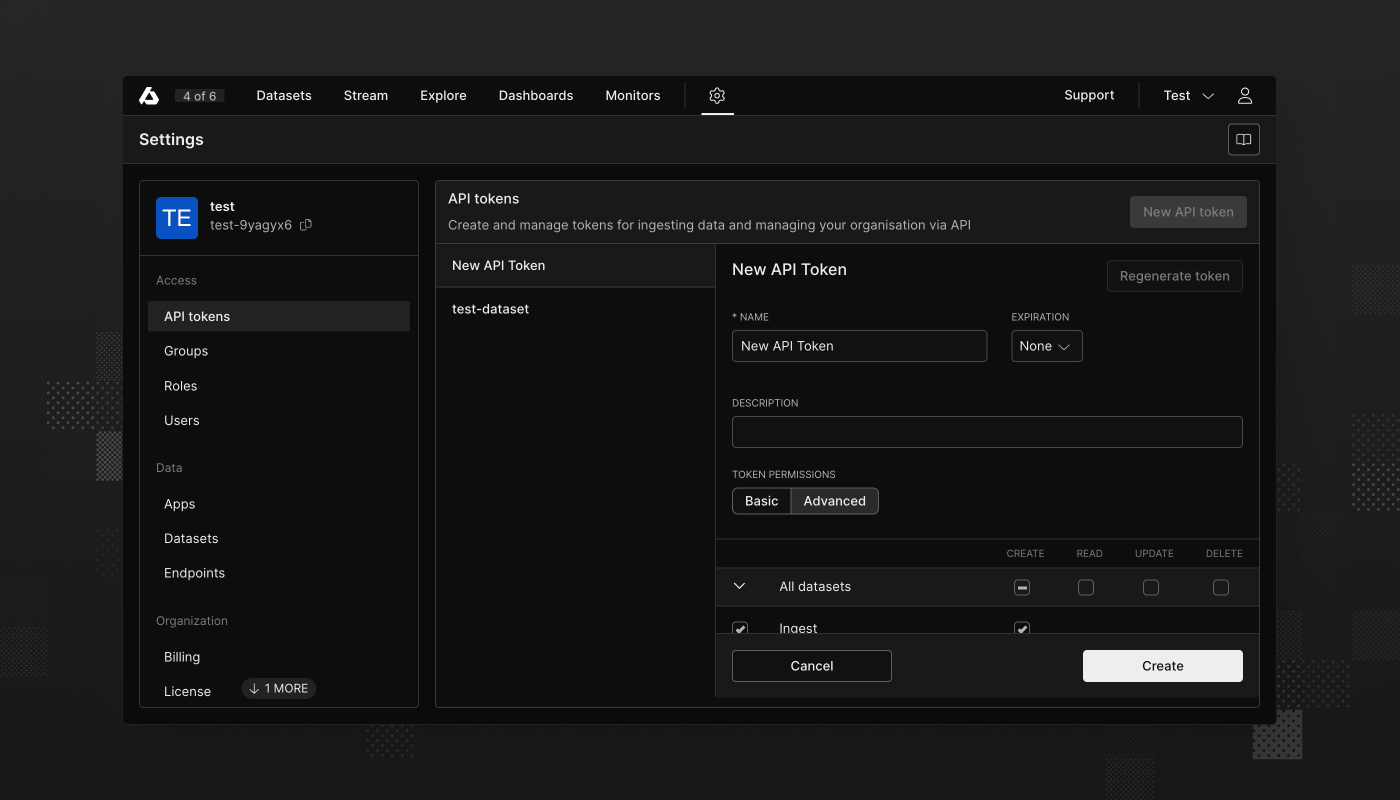
How To Create Api Tokens In Seatable Secure Guide Learn all about api tokens in this guide and learn how api tokens are utilized to ensure that apis stay protected from cybersecurity threats. Api tokens are one of the most popular methods that api developers are adopting to ensure their api assets are as secure as possible. to help you get started with api tokens, we’ve put together a thorough guide, with everything you’d ever want to know about using api tokens. Let us see what an api token is and how it works, and what are the best practices for generating and managing one's own access keys while limiting the risks associated with exposing data via apis. An api token is a unique identifier used to authenticate a user or application to access an api. it is created by the service provider and must be included in every api request to authorize access to protected resources.
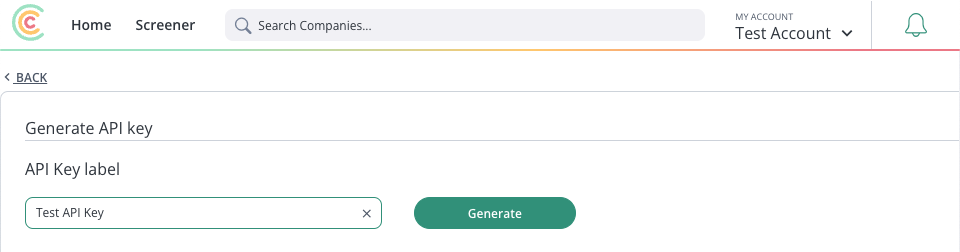
Getting Api Tokens Let us see what an api token is and how it works, and what are the best practices for generating and managing one's own access keys while limiting the risks associated with exposing data via apis. An api token is a unique identifier used to authenticate a user or application to access an api. it is created by the service provider and must be included in every api request to authorize access to protected resources. Explore the vital role of api tokens in secure data access, understanding types, best practices, and how they work with api gateways. An api token is a special code or digital string that verifies the identity of a user, application, or system when making a request to an api. think of it like a password or access card that lets your application securely connect to another system or service. By understanding how api tokens work, implementing security best practices, and choosing the appropriate authentication methods, developers can ensure the integrity and confidentiality of their apis and the data they expose. This guide will provide you with most of the “how tos” in terms of generating and securing machine to machine sessions using api tokens.
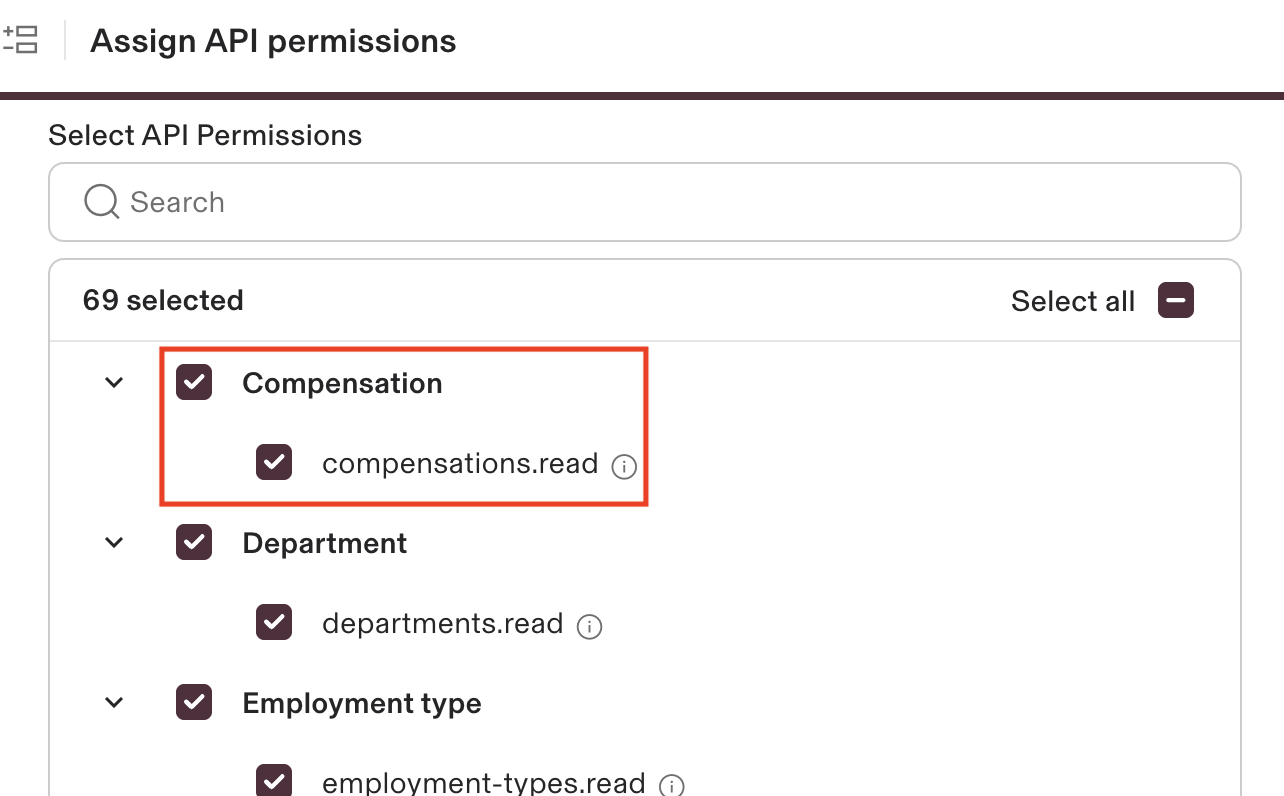
Api Token Scopes Explore the vital role of api tokens in secure data access, understanding types, best practices, and how they work with api gateways. An api token is a special code or digital string that verifies the identity of a user, application, or system when making a request to an api. think of it like a password or access card that lets your application securely connect to another system or service. By understanding how api tokens work, implementing security best practices, and choosing the appropriate authentication methods, developers can ensure the integrity and confidentiality of their apis and the data they expose. This guide will provide you with most of the “how tos” in terms of generating and securing machine to machine sessions using api tokens.

Api Tokens Cloudblue Connect By understanding how api tokens work, implementing security best practices, and choosing the appropriate authentication methods, developers can ensure the integrity and confidentiality of their apis and the data they expose. This guide will provide you with most of the “how tos” in terms of generating and securing machine to machine sessions using api tokens.
Comments are closed.