How 802 1x Works

Configuring And Understanding 802 1x Port Based Authentication Pdf Learn what 802.1x authentication is, its main parts, how it works, and what you can do with it. learn why users can be authenticated, profiled, denied access, and restricted based on credentials. In this guide, we’ll discuss how to deploy 802.1x, what it’s used for, and explain why 802.1x is still vital to securing modern organization networks.

Deep Dive Into How Authentication With 802 1x Works Aranya Ab Ieee 802.1x is an ieee standard for port based network access control (pnac). it is part of the ieee 802.1 group of networking protocols. it provides an authentication mechanism to devices wishing to attach to a lan or wlan. Different from other access control mechanisms, 802.1x implements user level access control by controlling access ports. the 802.1x protocol defines two logical port entities for a physical access port — the controlled port and the uncontrolled port — to separate services from authentication. This article explains the ieee 802.1x authentication standard which defines how to authenticate devices that connect with other devices. Discover how the ieee 802.1x authentication protocol enables secure, identity based network access with eap, radius, and zero trust integration.
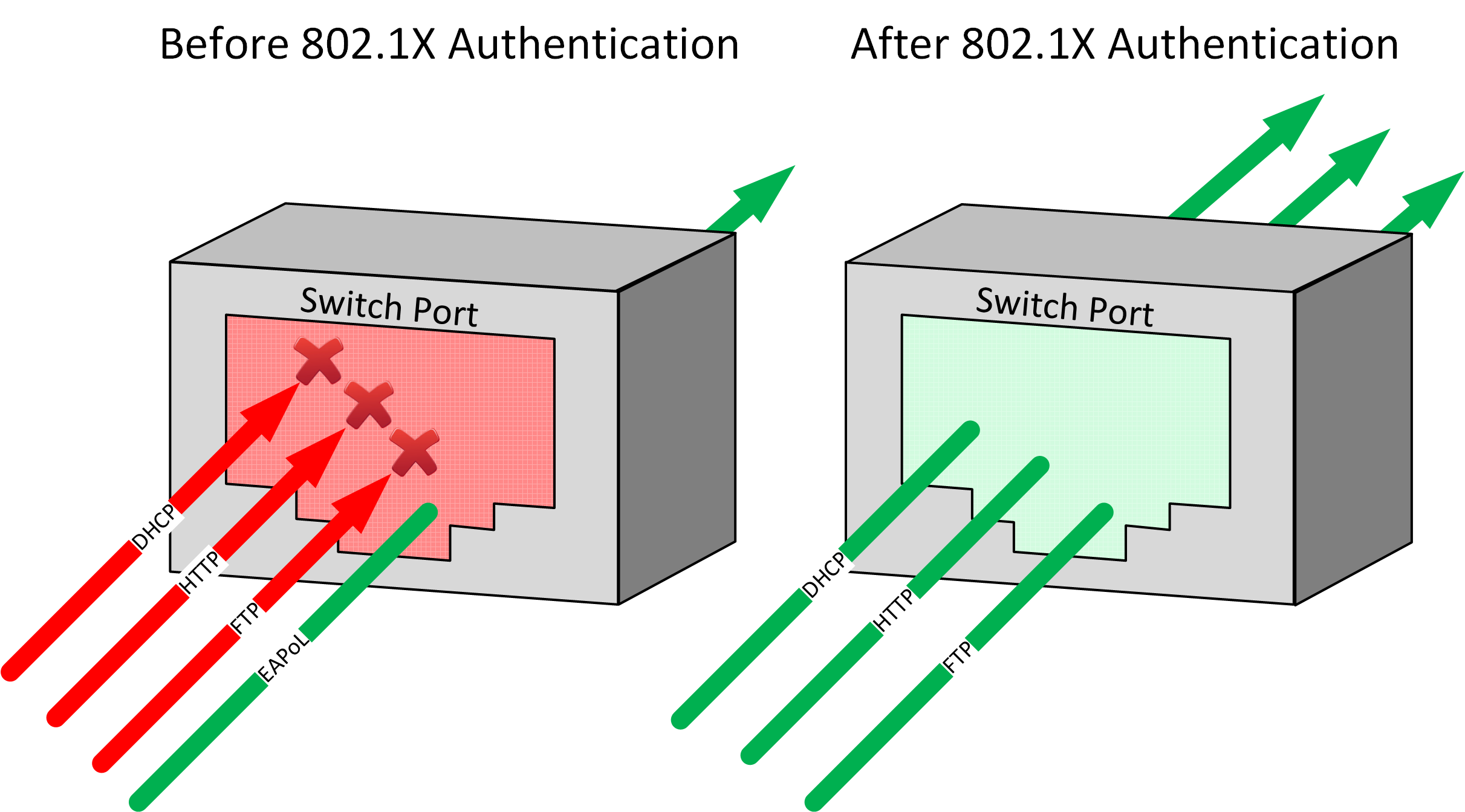
Aaa And 802 1x Authentication This article explains the ieee 802.1x authentication standard which defines how to authenticate devices that connect with other devices. Discover how the ieee 802.1x authentication protocol enables secure, identity based network access with eap, radius, and zero trust integration. The 802.1x protocol comprises three fundamental components: the supplicant, the authenticator, and the authentication server. we will carry out an in depth analysis of each of these components. The ieee 802.1x standard allows network switches and access points to hand off device authentication to a specialized server so it can be managed and updated centrally. Ieee 802.1x controls who can access the lan by authenticating each connected device. it uses eapol (extensible authentication protocol over lan) to verify identity before allowing data to pass. How the 802.1x network authentication protocol works? the 802.1x authentication process works as follows: when a supplicant (e.g., a user’s laptop) attempts to connect to a network, the authenticator (e.g., a network switch) blocks all traffic from the supplicant until it is authenticated.

Understanding 802 1x Authentication And Network Access Control Nac In The 802.1x protocol comprises three fundamental components: the supplicant, the authenticator, and the authentication server. we will carry out an in depth analysis of each of these components. The ieee 802.1x standard allows network switches and access points to hand off device authentication to a specialized server so it can be managed and updated centrally. Ieee 802.1x controls who can access the lan by authenticating each connected device. it uses eapol (extensible authentication protocol over lan) to verify identity before allowing data to pass. How the 802.1x network authentication protocol works? the 802.1x authentication process works as follows: when a supplicant (e.g., a user’s laptop) attempts to connect to a network, the authenticator (e.g., a network switch) blocks all traffic from the supplicant until it is authenticated.
Comments are closed.