Handling Jwt Safely Mitigating Common Security Risks Preventing The
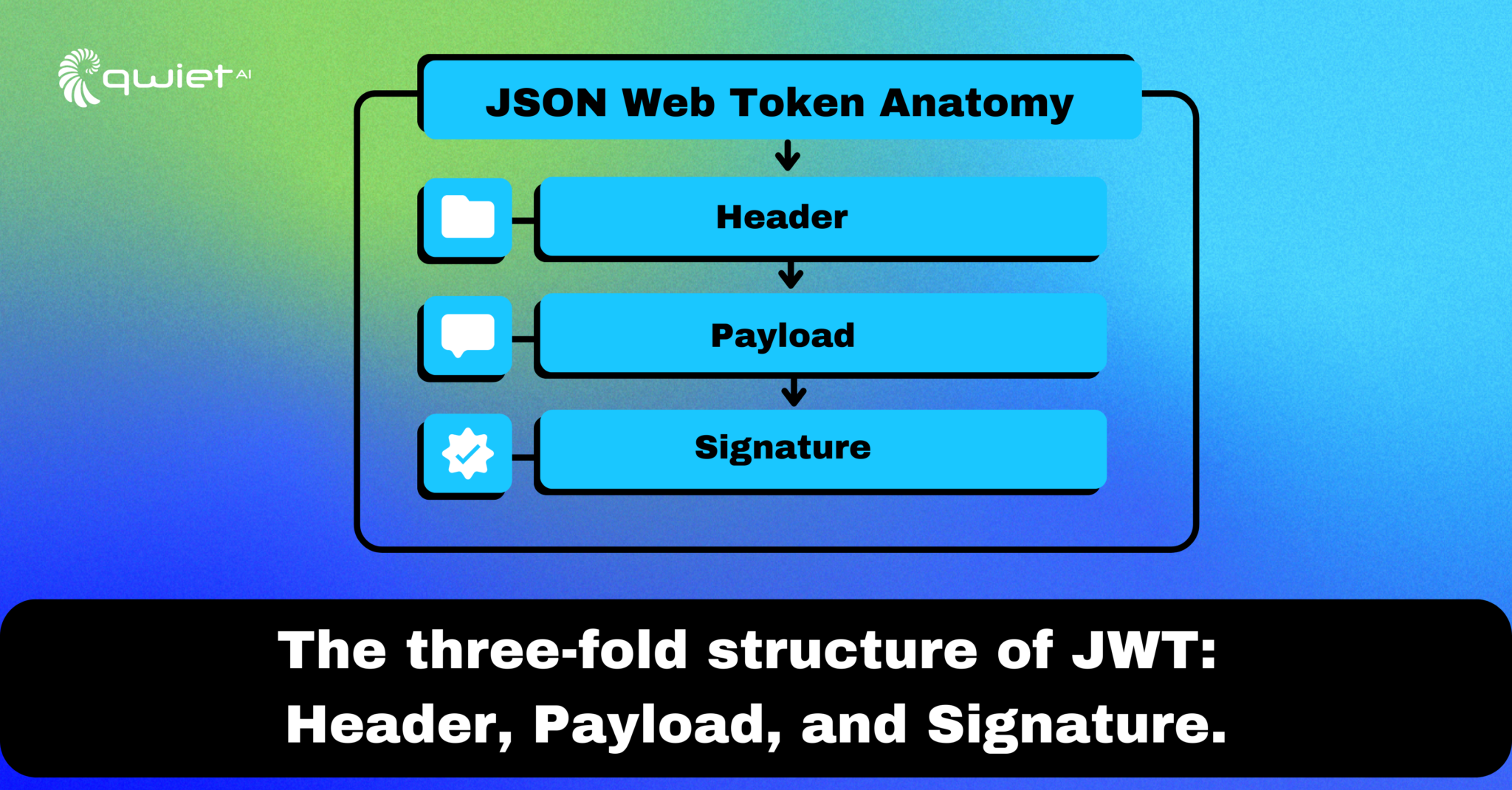
Handling Jwt Safely Mitigating Common Security Risks Preventing The Jwts are a cornerstone in modern application security, effectively and securely transmitting vital information. however, mastering their intricacies and potential vulnerabilities demands more than just theoretical understanding. Learn how jwt works, understand the most common security vulnerabilities, and apply proven best practices to protect tokens in production authentication systems.

Handling Jwt Safely Mitigating Common Security Risks Preventing The Identify and fix jwt vulnerabilities: algorithm confusion, weak secrets, and missing validation, practical hardening techniques with examples. Json web tokens (jwts) are compact and convenient, but mistakes in signing, storage, or validation can lead to account takeover. this guide explains how jwts work, common pitfalls, and a secure blueprint for production deployments. This article shows some best practices for using jwts so that you can maintain a high level of security in your applications. these practices are what we recommend at curity and are based on community standards written down in rfcs as well as our own experience from working with jwts. Master jwt best practices with our comprehensive guide. learn jwt token security, refresh token strategies, and avoid common pitfalls.
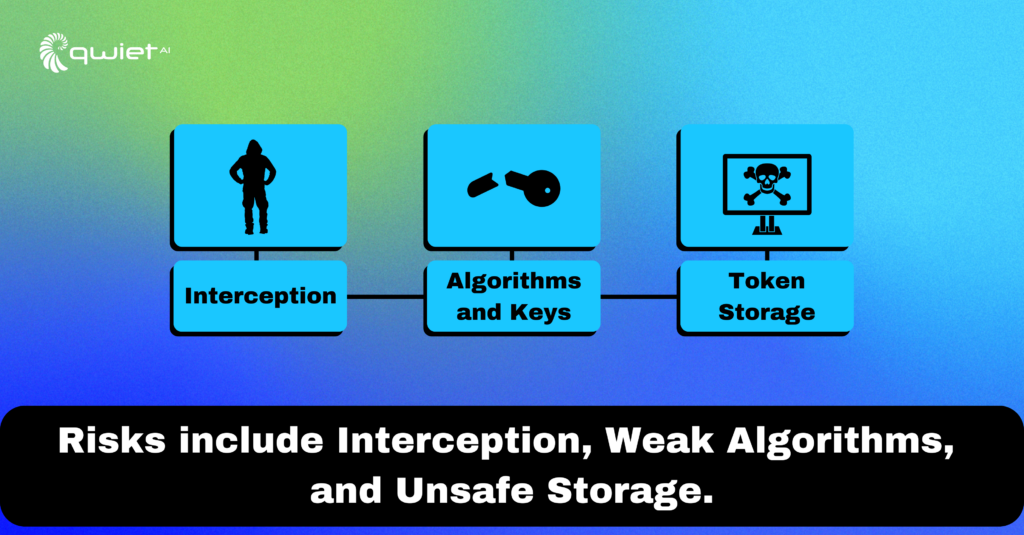
Handling Jwt Safely Mitigating Common Security Risks Preventing The This article shows some best practices for using jwts so that you can maintain a high level of security in your applications. these practices are what we recommend at curity and are based on community standards written down in rfcs as well as our own experience from working with jwts. Master jwt best practices with our comprehensive guide. learn jwt token security, refresh token strategies, and avoid common pitfalls. Learn the essential security best practices when implementing jwt in your applications to prevent vulnerabilities and ensure robust authentication. These are the 6 most common jwt token theft risks. 1. token theft via local storage. many developers store jwts in localstorage or sessionstorage for convenience. after all, they’re persistent, easy to access with javascript, and survive page reloads. Prevent common jwt mistakes: weak algorithms, improper validation, token leakage. learn secure validation, key rotation, and implementation best practices. Jwt security best practices are essential to safeguard your applications from data breaches, token forgery, and other common vulnerabilities. in this guide, we’ll explore comprehensive strategies that go beyond the basics, ensuring your jwt implementation is resilient, reliable, and trustworthy.

Handling Jwt Safely Mitigating Common Security Risks Preventing The Learn the essential security best practices when implementing jwt in your applications to prevent vulnerabilities and ensure robust authentication. These are the 6 most common jwt token theft risks. 1. token theft via local storage. many developers store jwts in localstorage or sessionstorage for convenience. after all, they’re persistent, easy to access with javascript, and survive page reloads. Prevent common jwt mistakes: weak algorithms, improper validation, token leakage. learn secure validation, key rotation, and implementation best practices. Jwt security best practices are essential to safeguard your applications from data breaches, token forgery, and other common vulnerabilities. in this guide, we’ll explore comprehensive strategies that go beyond the basics, ensuring your jwt implementation is resilient, reliable, and trustworthy.
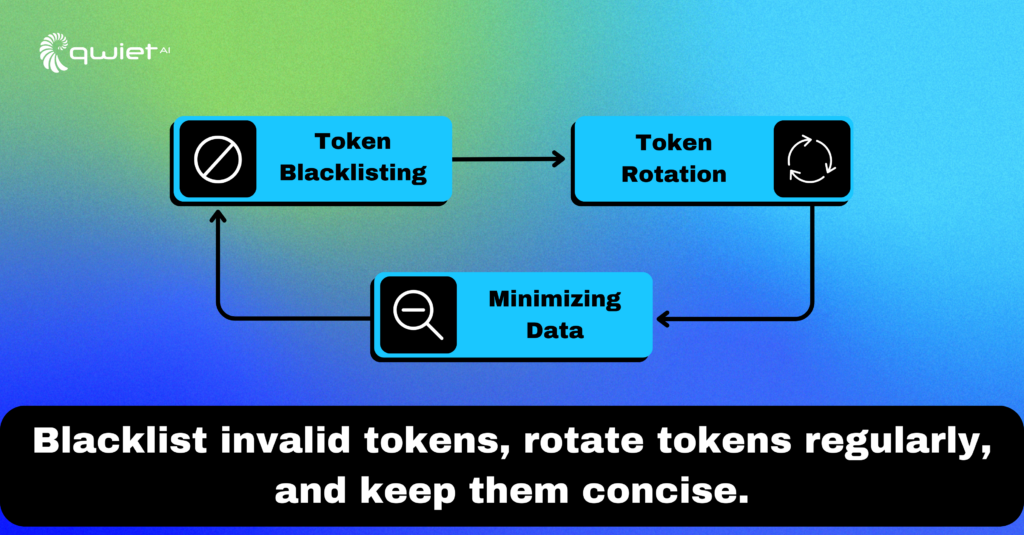
Handling Jwt Safely Mitigating Common Security Risks Preventing The Prevent common jwt mistakes: weak algorithms, improper validation, token leakage. learn secure validation, key rotation, and implementation best practices. Jwt security best practices are essential to safeguard your applications from data breaches, token forgery, and other common vulnerabilities. in this guide, we’ll explore comprehensive strategies that go beyond the basics, ensuring your jwt implementation is resilient, reliable, and trustworthy.
Comments are closed.