Hacking Lab 0x01 Packet Capturing And Analysis
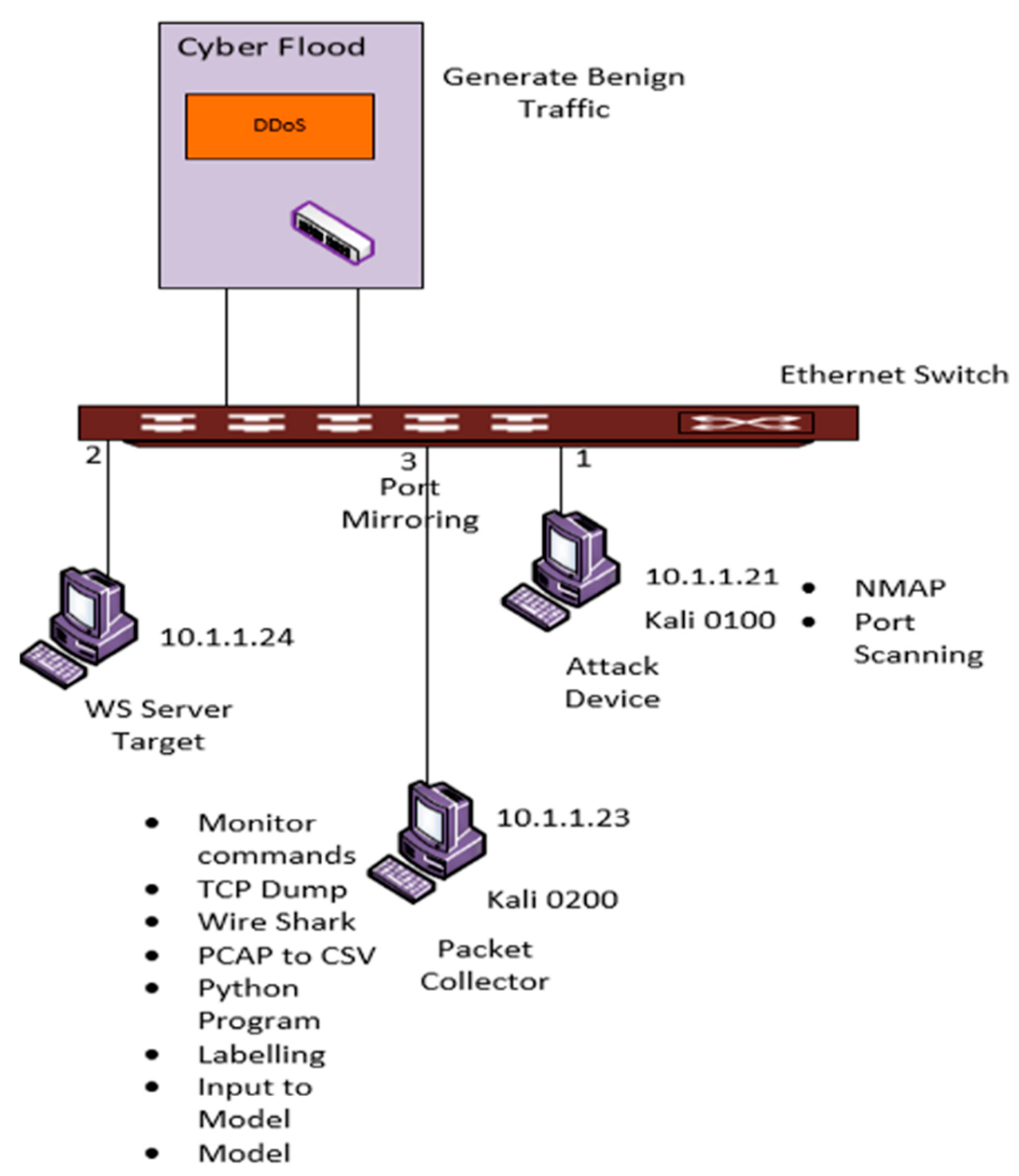
Detection Of Hacker Intention Using Deep Packet Inspection • it has two functions: 1) host identification by using ip addressing system (ipv4 and ipv6); and 2) packets routing from source to destination. • the examples of internet layer protocols are internet protocol (ip), internet control message protocol (icmp), and address resolution protocol (arp). You will explore how to capture and analyze network packets using various tools and understand the process of packet transmission to and from the owasp broken web application vm.
Wireshark Packet Analysis And Ethical Hacking Core Skills Become A Basic packet inspection: capture network traffic using wire shark and analyze basic protocols like http, dns, and smtp to understand how data is transmitted and received. Instructions: this lab must be completed individually by each student. there are two parts of this lab: ‘lab1a’and ‘lab1b’. ructions for carrying out the lab and has also got 4 questions given at the end of the hand. This command will begin gathering all packets using tcpdump, and we then use grep to find and display all post requests to us. this is an example of how tcpdump can be used in a creative fashion to display detailed information about the network. Let’s say a port on a remote host is filtered with something like an iptables based packet filter (see lecture 18) and your scanner sends it a syn packet or an icmp ping packet, you may not get back anything at all.
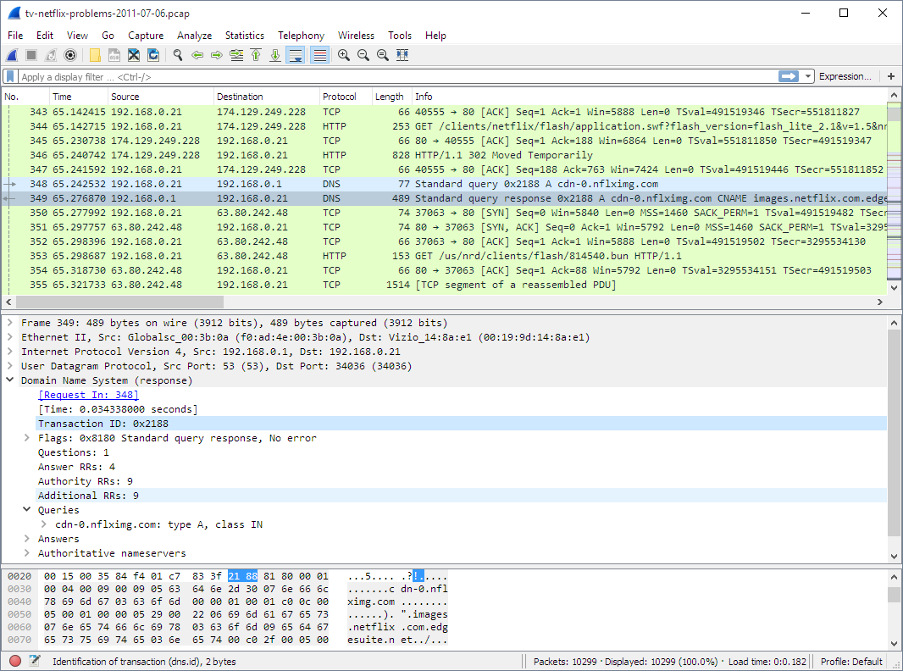
Network Packet Capture Explained This command will begin gathering all packets using tcpdump, and we then use grep to find and display all post requests to us. this is an example of how tcpdump can be used in a creative fashion to display detailed information about the network. Let’s say a port on a remote host is filtered with something like an iptables based packet filter (see lecture 18) and your scanner sends it a syn packet or an icmp ping packet, you may not get back anything at all. In this lab you will be utilising tshark to analyse packet capture (pcap) files and capture network traffic. preferably this lab will be done locally on your own machine, but you can access the lab environment during the tutorial. Solution given a packet file .pcap for analysis. with few packets, use follow > tcp stream to combine fragmented packets for easier viewing. all 14 tcp streams are mostly readable, but after a powershell script section, there’s a completely unreadable packet segment (as shown). Hacking lab 0x01 packet capturing and network forensics © paul w. poteete, 2016 overview: this lab introduces the student to packet capturing and network forensics. Ccs344 – eh lab manual free download as pdf file (.pdf), text file (.txt) or read online for free.
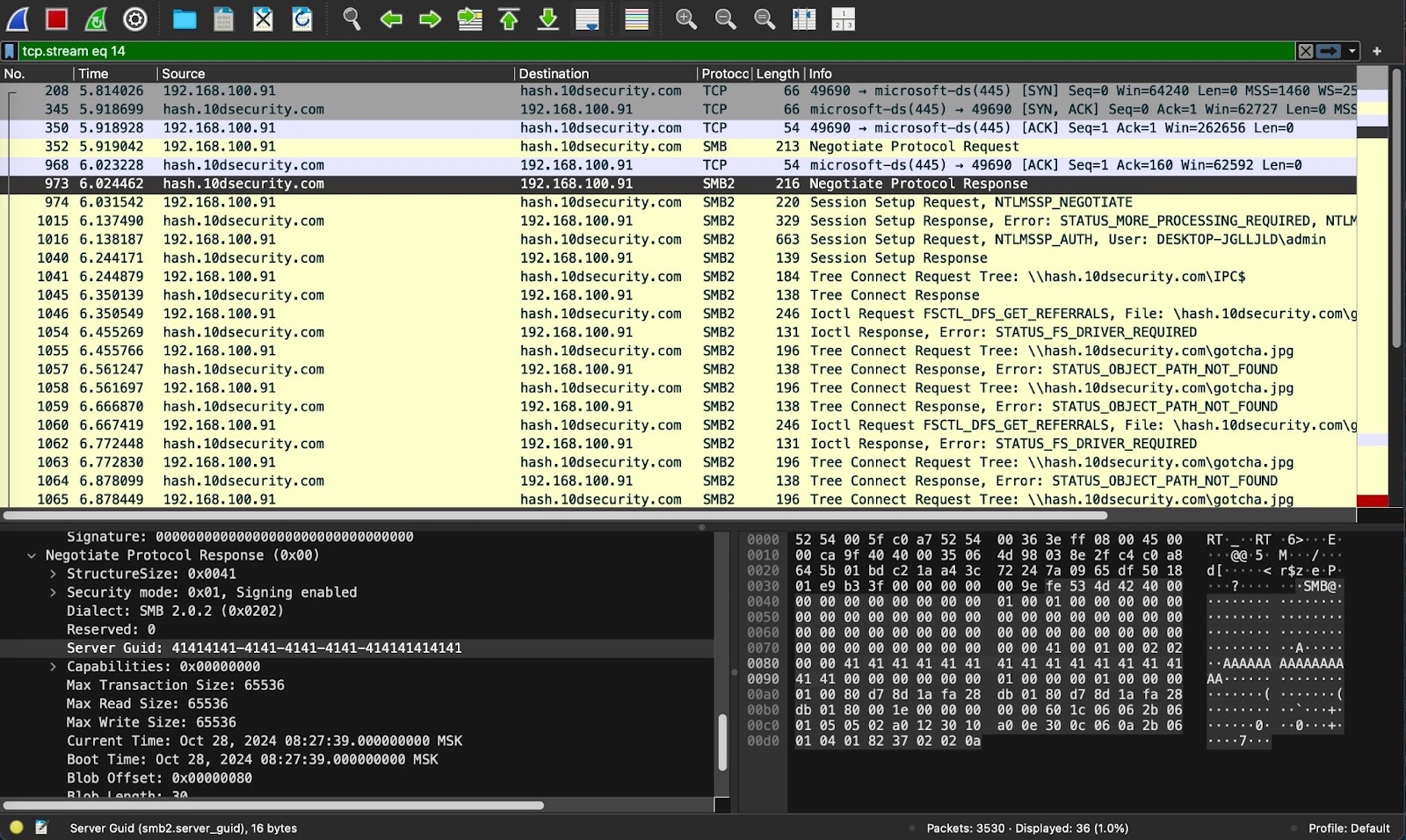
How To Capture Decrypt And Analyze Malicious Network Traffic In this lab you will be utilising tshark to analyse packet capture (pcap) files and capture network traffic. preferably this lab will be done locally on your own machine, but you can access the lab environment during the tutorial. Solution given a packet file .pcap for analysis. with few packets, use follow > tcp stream to combine fragmented packets for easier viewing. all 14 tcp streams are mostly readable, but after a powershell script section, there’s a completely unreadable packet segment (as shown). Hacking lab 0x01 packet capturing and network forensics © paul w. poteete, 2016 overview: this lab introduces the student to packet capturing and network forensics. Ccs344 – eh lab manual free download as pdf file (.pdf), text file (.txt) or read online for free.
Comments are closed.